Authorities entities, military corporations, and civilian end users in Ukraine and Poland have been focused as component of a series of campaigns made to steal sensitive details and gain persistent remote access to the contaminated techniques.
The intrusion established, which stretches from April 2022 to July 2023, leverages phishing lures and decoy documents to deploy a downloader malware named PicassoLoader, which acts as a conduit to launch Cobalt Strike Beacon and njRAT.
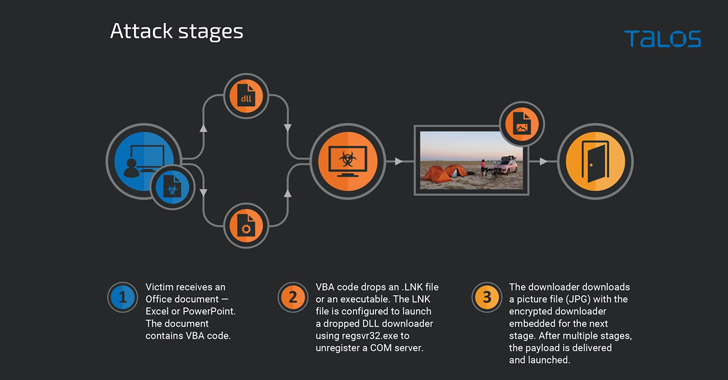
“The assaults utilized a multistage infection chain initiated with malicious Microsoft Workplace documents, most generally working with Microsoft Excel and PowerPoint file formats,” Cisco Talos researcher Vanja Svajcer stated in a new report. “This was followed by an executable downloader and payload hid in an picture file, probable to make its detection far more difficult.”
Some of the pursuits have been attributed to a risk actor named GhostWriter (aka UAC-0057 or UNC1151), whose priorities are reported to align with the Belarusian governing administration.
It truly is truly worth noting that a subset of these attacks has already been documented around the earlier year by Ukraine’s Pc Crisis Reaction Group (CERT-UA) and Fortinet FortiGuard Labs, a single of which utilized macro-laden PowerPoint documents to supply Agent Tesla malware in July 2022.
The infection chains purpose to convince victims to help macros, with the VBA macro engineered to fall a DLL downloader recognized as PicassoLoader that subsequently reaches out to an attacker-managed internet site to fetch the upcoming-phase payload, a respectable graphic file that embeds the final malware.
The disclosure comes as CERT-UA in depth a variety of phishing operations distributing the SmokeLoader malware as well as a smishing attack created to gain unauthorized manage of targets’ Telegram accounts.
Past month, CERT-UA disclosed a cyber espionage marketing campaign aimed at point out businesses and media associates in Ukraine that would make use of email and immediate messengers to distribute files, which, when launched, results in the execution of a PowerShell script named LONEPAGE to fetch following-phase browser stealer (THUMBCHOP) and keylogger (CLOGFLAG) payloads.
Forthcoming WEBINARShield From Insider Threats: Grasp SaaS Security Posture Management
Nervous about insider threats? We’ve bought you lined! Sign up for this webinar to explore simple techniques and the insider secrets of proactive security with SaaS Security Posture Administration.
Be part of These days
GhostWriter is one particular among the several threat actors that have established their sights on Ukraine. This also consists of the Russian nation-point out group APT28, which has been noticed making use of HTML attachments in phishing e-mail that prompt recipients to improve their UKR.NET and Yahoo! passwords owing to suspicious activity detected in their accounts so as to redirect them to bogus landing internet pages that finally steal their qualifications.
The development also follows the adoption of a “conventional 5-stage playbook” by hackers associated with the Russian navy intelligence (GRU) in their disruptive operations from Ukraine in a “deliberate hard work to improve the pace, scale, and depth” of their attacks.
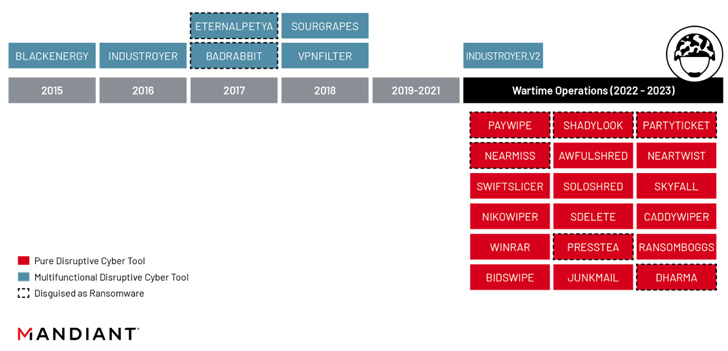
This includes taking edge of residing-on-the-edge infrastructure to achieve preliminary accessibility, working with living-off-the-land approaches to carry out reconnaissance, lateral movement and info theft to limit their malware footprint and evade detection, producing persistent, privileged access by means of group coverage objects (GPO), deploying wipers, and telegraphing their acts by way of hacktivist personas on Telegram.
“The gains the playbook affords are notably suited for a fast-paced and remarkably contested running environment, indicating that Russia’s wartime aims have possible guided the GRU’s decided on tactical programs of action,” Google-owned Mandiant mentioned.
Identified this article appealing? Observe us on Twitter and LinkedIn to read far more distinctive articles we post.
Some parts of this article are sourced from:
thehackernews.com

 TeamTNT’s Silentbob Botnet Infecting 196 Hosts in Cloud Attack Campaign
TeamTNT’s Silentbob Botnet Infecting 196 Hosts in Cloud Attack Campaign