In a sign that cybersecurity researchers continue to be underneath the radar of destructive actors, a evidence-of-notion (PoC) has been found on GitHub, concealing a backdoor with a “crafty” persistence technique.
“In this instance, the PoC is a wolf in sheep’s apparel, harboring destructive intent underneath the guise of a harmless understanding resource,” Uptycs scientists Nischay Hegde and Siddartha Malladi claimed. “Functioning as a downloader, it silently dumps and executes a Linux bash script, all the though disguising its operations as a kernel-level system.”
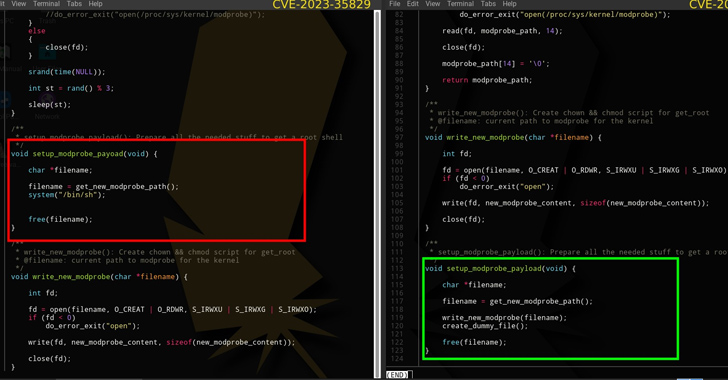
The repository masquerades as a PoC for CVE-2023-35829, a a short while ago disclosed large-severity flaw in the Linux kernel. It has since been taken down, but not ahead of it was forked 25 instances. A different PoC shared by the similar account, ChriSanders22, for CVE-2023-20871, a privilege escalation bug impacting VMware Fusion, was forked 2 times.
Uptypcs also identified a 2nd GitHub profile made up of a bogus PoC for CVE-2023-35829. It is continue to accessible as of crafting and has been forked 19 instances. A nearer evaluation of the dedicate record displays that the improvements had been pushed by ChriSanders22, suggesting it was forked from the initial repository.

The backdoor will come with a wide assortment of capabilities to steal delicate info from compromised hosts as well as enable a danger actor to obtain distant entry by including their SSH critical to the .ssh/licensed_keys file.
“The PoC intends for us to operate a make command that is an automation device utilized to compile and create executables from supply code data files,” the scientists discussed. “But inside of the Makefile resides a code snippet that builds and executes the malware. The malware names and operates a file named kworker, which provides the $House/.neighborhood/kworker path in $Dwelling/.bashrc, thus setting up its persistence.”
Approaching WEBINARShield Versus Insider Threats: Grasp SaaS Security Posture Administration
Concerned about insider threats? We’ve got you coated! Be a part of this webinar to explore realistic techniques and the secrets and techniques of proactive security with SaaS Security Posture Administration.
Be part of Currently
The enhancement comes just about a thirty day period right after VulnCheck learned a selection of faux GitHub accounts posing as security researchers to distribute malware less than the guise of PoC exploits for preferred program these types of as Discord, Google Chrome, Microsoft Exchange Server, Signal, and WhatsApp.
Customers who have downloaded and executed the PoCs are encouraged to unauthorized SSH keys, delete the kworker file, erase the kworker path from the bashrc file, and test /tmp/.iCE-unix.pid for probable threats.
“Even though it can be demanding to distinguish legit PoCs from misleading ones, adopting protected practices this kind of as tests in isolated environments (e.g., digital devices) can offer a layer of safety,” the scientists explained.
Found this post attention-grabbing? Adhere to us on Twitter and LinkedIn to study extra exclusive written content we article.
Some parts of this article are sourced from:
thehackernews.com

 Rockwell Automation ControlLogix Bugs Expose Industrial Systems to Remote Attacks
Rockwell Automation ControlLogix Bugs Expose Industrial Systems to Remote Attacks