An “intense” superior persistent threat (APT) team regarded as SideWinder has been linked to above 1,000 new assaults because April 2020.
“Some of the principal attributes of this danger actor that make it stand out amid the many others, are the sheer quantity, significant frequency and persistence of their assaults and the huge assortment of encrypted and obfuscated malicious parts employed in their operations,” cybersecurity agency Kaspersky mentioned in a report that was offered at Black Hat Asia this thirty day period.
SideWinder, also called Rattlesnake or T-APT-04, is claimed to have been active since at minimum 2012 with a track history of concentrating on armed service, defense, aviation, IT companies, and lawful corporations in Central Asian nations around the world this kind of as Afghanistan, Bangladesh, Nepal, and Pakistan.

Kaspersky’s APT trends report for Q1 2022 published late previous thirty day period unveiled that the danger actor is actively growing the geography of its targets beyond its target profile to other nations and locations, which includes Singapore.
SideWinder has also been noticed capitalizing the ongoing Russo-Ukrainian war as a lure in its phishing campaigns to distribute malware and steal sensitive facts.
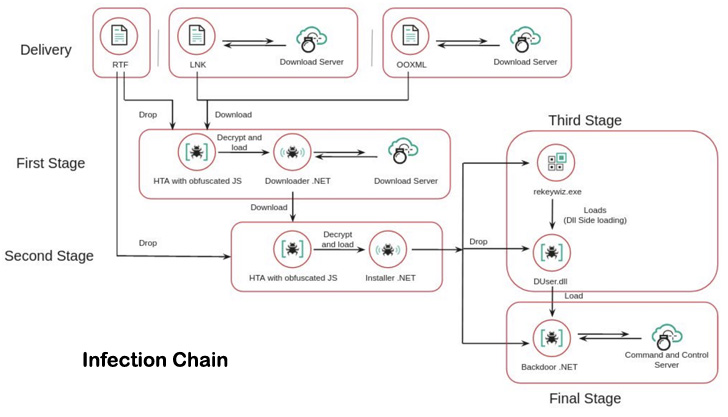
The adversarial collective’s infection chains are notable for incorporating malware-rigged paperwork that choose edge of a remote code vulnerability in the Equation Editor component of Microsoft Business office (CVE-2017-11882) to deploy malicious payloads on compromised devices.
In addition, SideWinder’s toolset employs a number of innovative obfuscation routines, encryption with unique keys for every malicious file, multi-layer malware, and splitting command-and-command (C2) infrastructure strings into distinctive malware factors.
The 3-stage an infection sequence commences with the rogue files dropping a HTML Software (HTA) payload, which subsequently hundreds a .NET-dependent module to set up a 2nd-phase HTA part which is created to deploy a .NET-centered installer.

This installer, in the following section, is equally liable for establishing persistence on the host and loading the final backdoor in memory. The implant, for its section, is capable of harvesting information of interest as very well as method data, between some others.
No fewer than 400 domains and subdomains have been place to use by the threat actor over the previous two several years. To insert an additional layer of stealth, the URLs applied for C2 domains are sliced into two components, the to start with portion of which is involved in the .NET installer and the latter half is encrypted inside the 2nd phase HTA module.
“This risk actor has a rather substantial stage of sophistication using a variety of an infection vectors and highly developed attack procedures,” Noushin Shabab of Kaspersky reported, urging that organizations use up-to-date variations of Microsoft Business to mitigate such assaults.
Uncovered this report intriguing? Comply with THN on Facebook, Twitter and LinkedIn to read far more exclusive content we article.
Some parts of this article are sourced from:
thehackernews.com

