A Microsoft developing in Europe. (efes, CC0, through Wikimedia Commons)
A a short while ago found phishing rip-off that convincingly impersonates the Microsoft Windows emblem with an HTML table serves as a new reminder of how social engineers can abuse a variety of components in e-mail to idiot both of those human recipients and specific security methods.
The plan initially commenced to arise late very last year into January and will involve applying a desk to establish a 2×2 grid of cells, and then filling them in with shades to make the desk search just like the iconic Windows logo. The existence of this fraudulent, yet reliable-wanting brand lends more credibility to phishing emails, and in accordance to Inky they can idiot some conventional Safe Email Gateways that are likely to forget the existence of tables as a suspicious component.
“This new tactic most probably originated in a solitary phishing kit and is now adopted in many kits,” said Bukar Alibe, cyber security analyst at Inky.
Although this precise scam may perhaps be new, it’s just the hottest phishing tactic to incorporate HTML tables. For occasion, “previously HTML tables have been abused by working with combos of black and white cells to generate graphics that search like URLs. This is no for a longer period utilised mainly because it looks visually various and suspicious when as opposed to a typical hyperlink,” reported Alibe pointed out.
A further related method utilized to bypass text filters is to make a desk, erase all borders from it, configure it to bunch the numerous knowledge cells collectively, and then add parts of text to the individual cells to make it glance like typical text.
“Attackers… split up destructive words and phrases and location pieces of the word in distinct adjacent cells,” said Alibe. “For instance, a bitcoin filter can be thwarted by inserting ‘bi,’ ‘tco,’ and ‘in’ in distinctive cells. This can make it readable for individuals and obfuscated for unsophisticated scanners.”
In this newest marketing campaign, Inky uncovered a collection of e-mail employing the fake Microsoft emblem in an endeavor to get recipients to click a destructive url, open a weaponized attachment or call a fraud phone range “where an evil operative tries to extract individual and economic info,” the report states.
Illustrations of these phishes included a pretend new fax notification from SharePoint, that includes a website link that employed an open redirect to consider victims to a compromised web advancement resource internet site, where destructive content was injected into their laptop. Other lures included a fake Workplace 365 email with a phone password expiration a phony voicemail notification. The attack system, a destructive hyperlink, was hid in an HTML attachment.
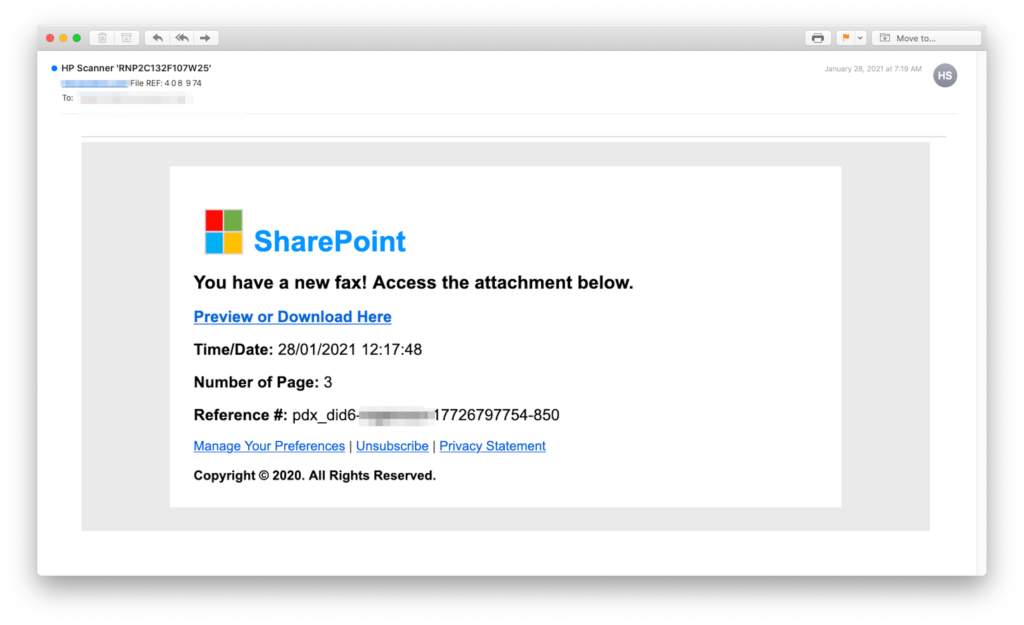 A SharePoint-themed phishing email showcasing a bogus Windows emblem.
A SharePoint-themed phishing email showcasing a bogus Windows emblem.
The marketing campaign also leveraged other nicely-worn tactics, like “open redirects, abused cloud web pages, booby trapped HTML attachments, hijacked email internet marketing campaign tools, and zero-font character stuffing.”
Roy Rotem, Avanan co-founder and head of info science, verified the presence of these faux Microsoft logo attacks, noting that “we’re starting to see an boost this year.”
“These attacks creatively use HTML and CSS to impersonate logos, makes and more,” Rotem explained. “We see tons of obfuscation techniques against Workplace 365, and a lot of of them are also profitable towards standard, legacy email gateways. These assaults are attention-grabbing mainly because you can’t depend on the HTML/CSS static assessment that conventional options use.”
Luckily, firms equipped with extra highly developed, fashionable email security methods – specially these with device studying and/or personal computer eyesight – ought to be capable to establish the pretend emblem and deflect this attack.
“In this scenario, a equipment would see an HTML desk, but laptop or computer vision would area that this meant desk is seeking to be a Microsoft logo,” the report claims. “With that information, the detection procedure can look at to see irrespective of whether the sender seriously is Microsoft.”
Rotem described an productive procedure to protect against these kinds of obfuscation assaults: “render the HTML email overall body in a sandbox, and conduct graphic analysis… and implement cognitive AI styles to obtain similarities and impersonation tries. By using headless browsers, you can properly render the web page and utilize AI picture-recognition designs to figure out if there is any impersonation on the website page. This security layer is not just productive in opposition to this precise attack, but in opposition to a wide selection of obfuscation attempts in the HTML of the email.”
Some parts of this article are sourced from:
www.scmagazine.com


 iPhone and Mac sales are way up from the start of the pandemic
iPhone and Mac sales are way up from the start of the pandemic