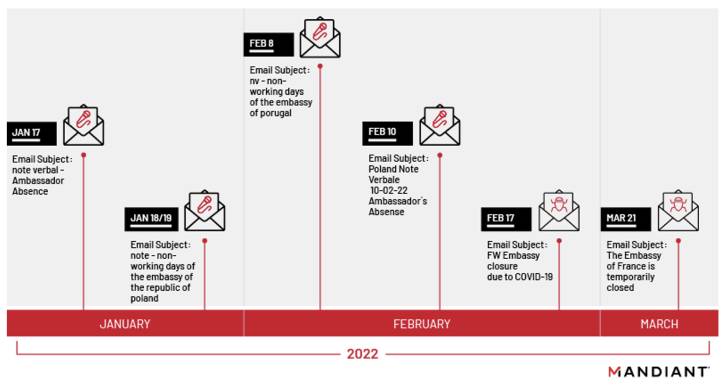
A Russian state-sponsored threat actor has been observed focusing on diplomatic and governing administration entities as section of a collection of phishing strategies commencing on January 17, 2022.
Danger intelligence and incident response firm Mandiant attributed the assaults to a hacking team tracked as APT29 (aka Cozy Bear), with some set of the activities affiliated with the crew assigned the moniker Nobelium (aka UNC2452/2652).
“This newest wave of spear phishing showcases APT29’s enduring pursuits in obtaining diplomatic and international policy data from governments all over the earth,” the Mandiant reported in a report posted very last 7 days.
The initial entry is explained to have been aided by means of spear-phishing email messages masquerading as administrative notices, using legitimate but compromised email addresses from other diplomatic entities.
These e-mail incorporate an HTML dropper attachment referred to as ROOTSAW (aka EnvyScout) that, when opened, triggers an an infection sequence that delivers and executes a downloader dubbed BEATDROP on a goal system.
Prepared in C, BEATDROP is made to retrieve next-stage malware from a distant command-and-handle (C2) server. It achieves this by abusing Atlassian’s Trello assistance to retailer victim info and fetch AES-encrypted shellcode payloads to be executed.
Also utilized by APT29 is a resource named BOOMMIC (aka VaporRage) to set up a foothold inside of the setting, adopted by escalating their privileges in the compromised network for lateral motion and extensive reconnaissance of hosts.
What is much more, a subsequent operational shift observed in February 2022 observed the threat actor pivoting absent from BEATDROP in favor of a C++-based loader referred to as BEACON, potentially reflecting the group’s capacity to periodically change their TTPs to continue to be underneath the radar.
BEACON, programmed in C or C++, is component of the Cobalt Strike framework that facilitates arbitrary command execution, file transfer, and other backdoor features this sort of as capturing screenshots and keylogging.

The advancement follows the cybersecurity firm’s final decision to merge the uncategorized cluster UNC2452 into APT29, whilst noting the extremely advanced group’s propensity for evolving and refining its specialized tradecraft to obfuscate exercise and limit its electronic footprint to avoid detection.

Nobelium, notably, breached numerous enterprises by means of a source chain attack in which the adversary accessed and tampered with SolarWinds supply code, and utilized the vendor’s legit program updates to spread the malware to purchaser methods.
“The reliable and steady advancement in TTPs speaks to its disciplined nature and motivation to stealthy operations and persistence,” Mandiant stated, characterizing APT29 as an “evolving, disciplined, and really competent threat actor that operates with a heightened degree of operational security (OPSEC) for the functions of intelligence selection.”
The results also coincide with a exclusive report from Microsoft, which observed Nobelium attempting to breach IT firms serving govt consumers in NATO member states, working with the accessibility to siphon information from Western foreign coverage companies.
Discovered this write-up fascinating? Stick to THN on Fb, Twitter and LinkedIn to examine much more exclusive written content we post.
Some parts of this article are sourced from:
thehackernews.com


 The Wikimedia Foundation won't accept crypto donations anymore
The Wikimedia Foundation won't accept crypto donations anymore