A beforehand undocumented remote accessibility trojan (RAT) written in the Go programming language has been noticed disproportionately targeting entities in Italy, Spain, and the U.K.
Known as Nerbian RAT by company security business Proofpoint, the novel malware leverages COVID-19-themed lures to propagate as part of a small quantity email-borne phishing campaign that started off on April 26, 2022.
“The newly determined Nerbian RAT leverages multiple anti-examination factors spread throughout quite a few stages, including several open-resource libraries,” Proofpoint researchers claimed in a report shared with The Hacker News.
“It is written in operating method (OS) agnostic Go programming language, compiled for 64-little bit devices, and leverages numerous encryption routines to even more evade network analysis.”
The messages, amounting to fewer than 100 in selection, purport to be from the Earth Wellness Firm about safety steps similar to COVID-19, urging probable victims to open a macro-laced Microsoft Term doc to accessibility the “most current health guidance.”
Enabling the macros shows COVID-19 steering, like ways for self-isolation, while in the history, the embedded macro triggers an infection chain that delivers a payload known as “UpdateUAV.exe”, which acts as dropper for Nerbian RAT (“MoUsoCore.exe”) from a distant server.
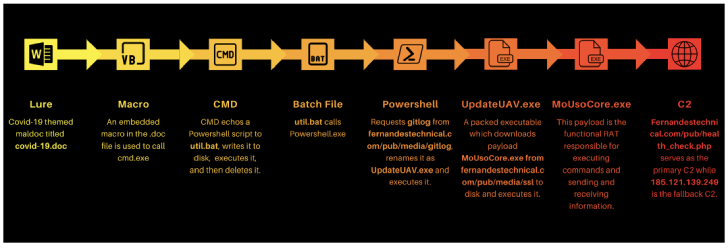
The dropper also would make use of the open-supply Chacal “anti-VM framework” to make reverse engineering tricky, working with it to carry out anti-reversing checks and terminating alone should it experience any debuggers or memory investigation courses.
The distant entry trojan, for its component, is outfitted to log keystrokes, capture screenshots, and execute arbitrary instructions, before exfiltrating the final results back to the server.
Even though both equally the dropper and the RAT are claimed to have been created by the same writer, the identification of the threat actor remains unknown as yet.
On top of that, Proofpoint cautioned that the dropper could be custom-made to deliver various payloads in long term assaults, whilst in its existing type, it can only retrieve the Nerbian RAT.
“Malware authors continue on to work at the intersection of open-source capacity and legal possibility,” Sherrod DeGrippo, vice president of threat study and detection at Proofpoint, reported in a assertion.
Observed this article attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to go through a lot more distinctive content material we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Facebook faces lawsuit in Kenya over poor working conditions for moderators
Facebook faces lawsuit in Kenya over poor working conditions for moderators