Cybersecurity researchers have disclosed a new type of Workplace malware dispersed as portion of a destructive email marketing campaign that qualified a lot more than 80 clients worldwide in an try to management sufferer equipment and steal data remotely.
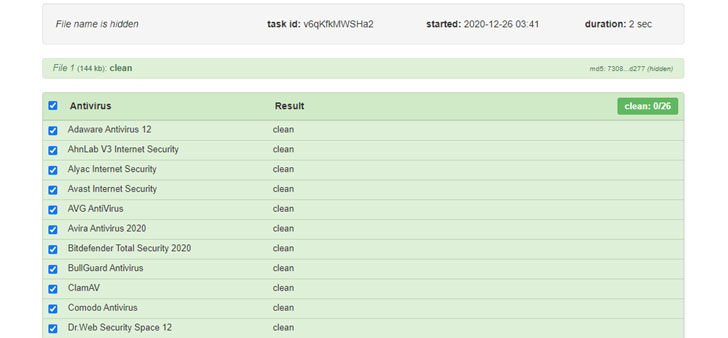
The device — dubbed “APOMacroSploit” — is a macro exploit generator that permits the user to create an Excel doc able of bypassing antivirus software program, Windows Antimalware Scan Interface (AMSI), and even Gmail and other email-primarily based phishing detection.
APOMacroSploit is believed to be the function of two French-based risk actors “Apocaliptique” and “Nitrix,” who are approximated to have made at the very least $5000 in considerably less than two months advertising the solution on HackForums.net.

About 40 hackers in overall are said to be driving the operation, utilizing 100 unique email senders in a slew of attacks concentrating on users in additional than 30 unique nations around the world. The attacks had been spotted for the initial time at the conclusion of November 2020, according to cybersecurity firm Check out Position.
“The malware an infection commences when the dynamic content material of the hooked up XLS doc is enabled, and an XLM macro immediately starts downloading a Windows technique command script,” the organization explained in a Tuesday report.
This procedure command script is retrieved from cutt.ly, which directs to servers hosting numerous BAT scripts that have the nickname of the buyers inserted connected to the filenames. The scripts are also responsible for executing the malware (“fola.exe”) on Windows programs, but not ahead of adding the malware locale in the exclusion path of Windows Defender and disabling Windows cleanup.
In 1 of the assaults, the malware — a Delphi Crypter followed by a next-phase distant accessibility Trojan known as BitRAT — was discovered hosted on a Bulgarian web-site catering to health care devices and provides, implying that the attackers breached the site to retail outlet the malicious executable.
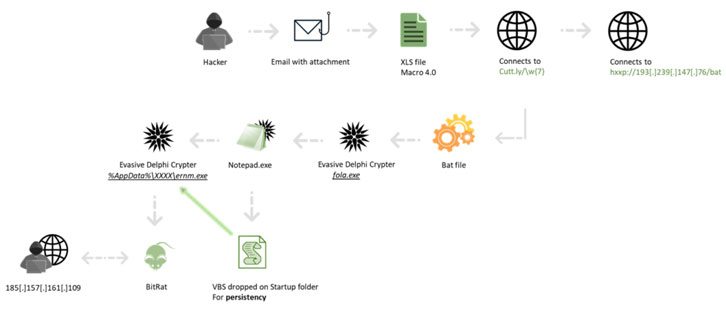
The strategy of using “crypters” or “packers” has come to be ever more preferred between menace actors to not only compress but also to make malware samples extra evasive and reverse engineer.
BitRAT, which was formally documented very last August, comes with features to mine cryptocurrencies, hack webcams, log keystrokes, obtain and upload arbitrary information, and remotely manage the procedure through a command-and-control server, which in this case fixed to a sub-domain of a reputable Bulgarian internet site for video clip surveillance devices.
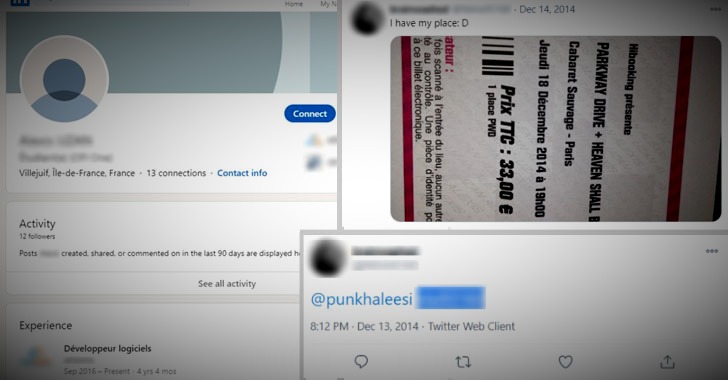
Even further investigation by Test Place involved chasing the electronic path still left by the two operators — which include two League of Legends participant profiles — ultimately leading the scientists to unmask the genuine id of Nitrix, who disclosed his actual title on Twitter when he posted a photograph of a ticket he purchased for a live performance in December 2014.
Though Nitrix is a program developer from Noisy-Le-Grand with 4 decades of practical experience as a program developer, Apocaliptique’s use of option names these as “apo93” or “apocaliptique93” has stirred up possibilities that the specific may possibly also be a French resident, as “93” is the colloquial name for the French division of Seine-Saint-Denis.
Check out Stage Research mentioned it experienced alerted legislation enforcement authorities about the identities of the attackers.
Located this article interesting? Abide by THN on Fb, Twitter and LinkedIn to study more exceptional content material we post.
Some parts of this article are sourced from:
thehackernews.com

 NHS Phishing Scam Promises #COVID19 Vaccine
NHS Phishing Scam Promises #COVID19 Vaccine