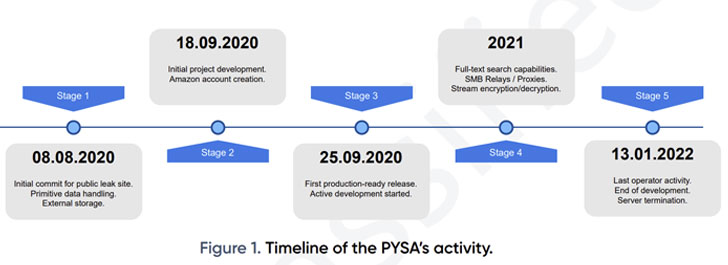
An 18-thirty day period-extended investigation of the PYSA ransomware operation has exposed that the cybercrime cartel followed a 5-phase program improvement cycle from August 2020, with the malware authors prioritizing features to increase the performance of its workflows.
This integrated a person-pleasant software like a total-text search motor to aid the extraction of metadata and permit the risk actors to discover and access sufferer information immediately.
“The team is identified to carefully exploration high-value targets before launching its assaults, compromising organization methods and forcing organizations to spend massive ransoms to restore their information,” Swiss cybersecurity firm PRODAFT reported in an exhaustive report posted last week.
PYSA, short for “Secure Your Process, Amigo” and a successor of the Mespinoza ransomware, was initial noticed in December 2019 and has emerged as the 3rd most widespread ransomware strain detected for the duration of the fourth quarter of 2021.
Given that September 2020, the cybercriminal gang is believed to have exfiltrated delicate information and facts belonging to as many as 747 victims until its servers were being taken offline earlier this January.

Most of its victims are located in the U.S. and Europe, with the group mostly striking authorities, health care, and educational sectors. “The U.S. was the most-impacted place, accounting for 59.2% of all PYSA events described, followed by the U.K. at 13.1%,” Intel 471 noted in an assessment of ransomware attacks recorded from Oct to December 2021.
PYSA, like other ransomware people, is recognized to follow the “major game looking” approach of double extortion, which consists of publicizing the stolen facts need to a victim refuse to comply with the group’s needs.
Just about every eligible file is encrypted and specified a “.pysa” extension, decoding which demands the RSA non-public vital that can only be attained following shelling out the ransom. Practically 58% of the PYSA victims are stated to have built electronic payments.
PRODAFT, which was capable to find a publicly available .git folder managed by PYSA operators, discovered one of the project’s authors as “[email protected],” a menace actor who is thought to be located in a country that observes daylight savings time primarily based on the commit history.
At least 11 accounts, a majority of which had been made on January 8, 2021, are stated to be in charge of the in general procedure, the investigation has disclosed. That mentioned, 4 of these accounts — named t1, t3, t4, and t5 — account for around 90% of activity on the group’s administration panel.
Other operational security blunders built by the group’s members also designed it attainable to identify a hidden provider working on the TOR anonymity network — a hosting company (Snel.com B.V.) found in the Netherlands — presenting a glimpse into the actor’s methods.
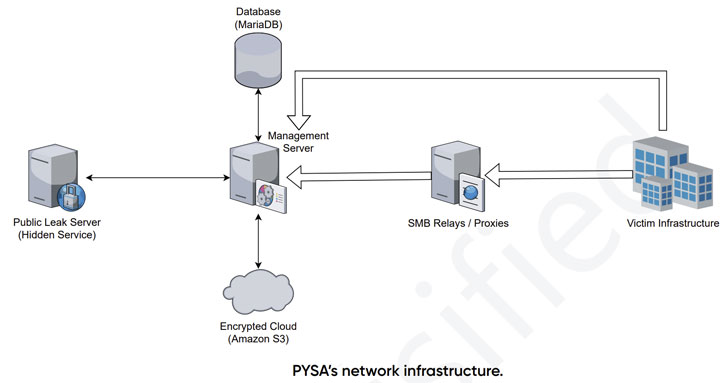
PYSA’s infrastructure also is made up of dockerized containers, which include community leak servers, database, and administration servers, as perfectly as an Amazon S3 cloud to shop the encrypted data files, which quantity to a large 31.47TB.

Also set to use is a personalized leak management panel to lookup private files in the data files exfiltrated from victims’ internal networks prior to encryption. Other than applying the Git version handle program to manage the advancement processes, the panel by itself is coded in PHP 7.3.12 making use of the Laravel framework.
What’s much more, the administration panel exposes a range of API endpoints that allows the technique to checklist files, down load documents, and analyze the data files for whole-text look for, which is created to categorize the stolen sufferer information and facts into broad groups for easy retrieval.
“The team is supported by capable developers who utilize modern operational paradigms to the group’s advancement cycle,” the researcher claimed. “It indicates a professional natural environment with very well-structured division of duties, alternatively than a loose network of semi-autonomous threat actors.”
If everything, the conclusions are however another indicator that ransomware gangs like PYSA and Conti operate and are organized like reputable application companies, even including an HR division to recruit new hires and an “worker of the month” award for tackling complicated complications.
The disclosure also will come as a report from cybersecurity business Sophos found that two or additional menace actor teams spent at least 5 months inside of the network of an unnamed regional U.S. authorities agency right before deploying a LockBit ransomware payload at the start off of the 12 months.
Observed this report attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to go through much more distinctive written content we put up.
Some parts of this article are sourced from:
thehackernews.com


 Benchmarking Linux Security – Latest Research Findings
Benchmarking Linux Security – Latest Research Findings