Two substantial-severity security vulnerabilities, which went undetected for various several years, have been uncovered in a legit driver that is aspect of Avast and AVG antivirus options.
“These vulnerabilities make it possible for attackers to escalate privileges enabling them to disable security items, overwrite program parts, corrupt the working technique, or execute destructive functions unimpeded,” SentinelOne researcher Kasif Dekel mentioned in a report shared with The Hacker News.
Tracked as CVE-2022-26522 and CVE-2022-26523, the flaws reside in a reputable anti-rootkit kernel driver named aswArPot.sys and are said to have been launched in Avast variation 12.1, which was introduced in June 2016.
Specifically, the shortcomings are rooted in a socket relationship handler in the kernel driver that could guide to privilege escalation by operating code in the kernel from a non-administrator consumer, most likely producing the working method to crash and exhibit a blue display screen of demise (BSoD) mistake.
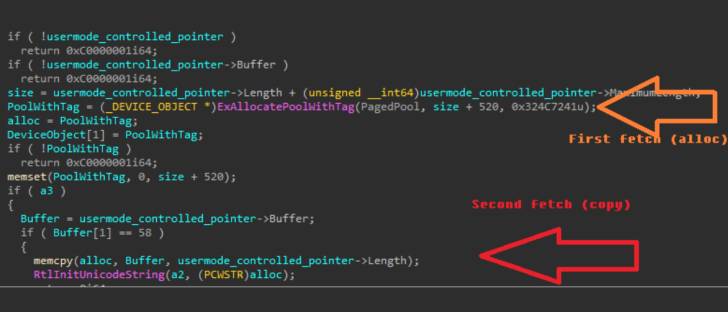
Worryingly, the flaws could also be exploited as component of a 2nd-stage browser attack or to complete a sandbox escape, leading to far-reaching implications.
Pursuing dependable disclosure on December 20, 2021, Avast tackled the issues in version 22.1 of the program unveiled on February 8, 2022. “Rootkit driver BSoD was fastened,” the corporation claimed in its release notes.
Though there is no evidence that these flaws ended up abused in the wild, the disclosure comes merely times right after Development Micro specific an AvosLocker ransomware attack that leveraged another issue in the very same driver to terminate antivirus methods on the compromised procedure.
Found this short article appealing? Comply with THN on Fb, Twitter and LinkedIn to read through much more special written content we publish.
Some parts of this article are sourced from:
thehackernews.com


 Heroku Forces User Password Resets Following GitHub OAuth Token Theft
Heroku Forces User Password Resets Following GitHub OAuth Token Theft