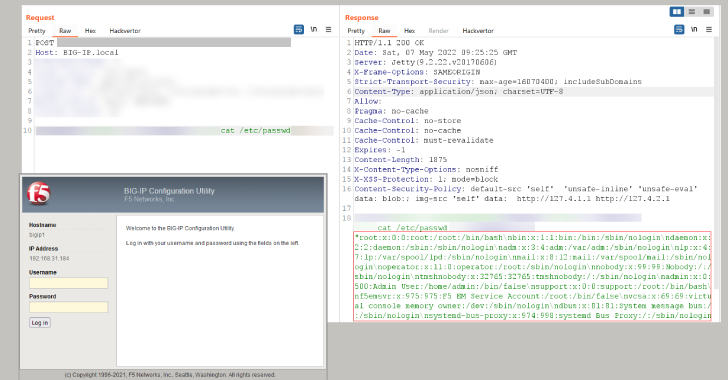
Times after F5 produced patches for a critical distant code execution vulnerability affecting its Big-IP relatives of goods, security scientists are warning that they were being ready to produce an exploit for the shortcoming.
Tracked CVE-2022-1388 (CVSS score: 9.8), the flaw relates to an iControl Relaxation authentication bypass that, if productively exploited, could lead to distant code execution, allowing for an attacker to achieve preliminary accessibility and just take control of an influenced system.
This could selection everywhere from deploying cryptocurrency miners to deploying web shells for comply with-on assaults, this sort of as facts theft and ransomware.
“We have reproduced the clean CVE-2022-1388 in F5’s Significant-IP,” cybersecurity firm Beneficial Systems mentioned in a tweet on Friday. “Patch ASAP!”
The critical security vulnerability impacts the next variations of Big-IP merchandise –
- 16.1. – 16.1.2
- 15.1. – 15.1.5
- 14.1. – 14.1.4
- 13.1. – 13.1.4
- 12.1. – 12.1.6
- 11.6.1 – 11.6.5
Fixes are obtainable in variations 17.., 16.1.2.2, 15.1.5.1, 14.1.4.6, and 13.1.5. Firmware versions 11.x and 12.x will not get security updates and buyers relying on those people variations really should contemplate upgrading to a more recent edition or apply the workarounds –
- Block iControl Rest entry through the self IP deal with
- Block iControl Rest accessibility through the administration interface, and
- Modify the Huge-IP httpd configuration
Final month, cybersecurity authorities from Australia, Canada, New Zealand, the U.K., and the U.S. jointly warned that “threat actors aggressively focused newly disclosed critical software package vulnerabilities versus wide focus on sets, together with community and personal sector corporations globally.”
With the F5 Big-IP flaw found trivial to exploit, destructive hacking crews are predicted to stick to suit, earning it imperative that influenced companies utilize the patches.
Uncovered this article attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to study extra special articles we publish.
Some parts of this article are sourced from:
thehackernews.com

 Some BMWs are shipping without Android Auto or CarPlay to avoid delays
Some BMWs are shipping without Android Auto or CarPlay to avoid delays