Operators associated with the Lazarus sub-team BlueNoroff have been linked to a sequence of cyberattacks focusing on modest and medium-sized companies worldwide with an aim to drain their cryptocurrency resources, in what is actually nonetheless an additional financially inspired operation mounted by the prolific North Korean point out-sponsored actor.
Russian cybersecurity organization Kaspersky, which is monitoring the intrusions less than the identify “SnatchCrypto,” famous that the marketing campaign has been managing considering the fact that at 2017, incorporating the assaults are aimed at startups in the FinTech sector positioned in China, Hong Kong, India, Poland, Russia, Singapore, Slovenia, the Czech Republic, the U.A.E., the U.S., Ukraine, and Vietnam.
“The attackers have been subtly abusing the have confidence in of the personnel working at focused organizations by sending them a comprehensive-highlighted Windows backdoor with surveillance features, disguised as a contract or an additional business file,” the scientists reported. “In get to ultimately empty the victim’s crypto wallet, the actor has produced substantial and harmful methods: intricate infrastructure, exploits and malware implants.”

BlueNoroff, and the more substantial Lazarus umbrella, are regarded for deploying a assorted arsenal of malware for a multi-pronged assault on corporations to illicitly procure cash, together with relying on a blend of innovative phishing methods and innovative malware, for the sanctions-hit North Korean regime and deliver revenue for its nuclear weapons and ballistic missile systems.
If something, these cyber offensives are paying out off large time. In accordance to a new report revealed by blockchain analytics agency Chainalysis, the Lazarus Team has been joined to seven attacks on cryptocurrency platforms that extracted just about $400 million worthy of of digital belongings in 2021 on your own, up from $300 million in 2020.
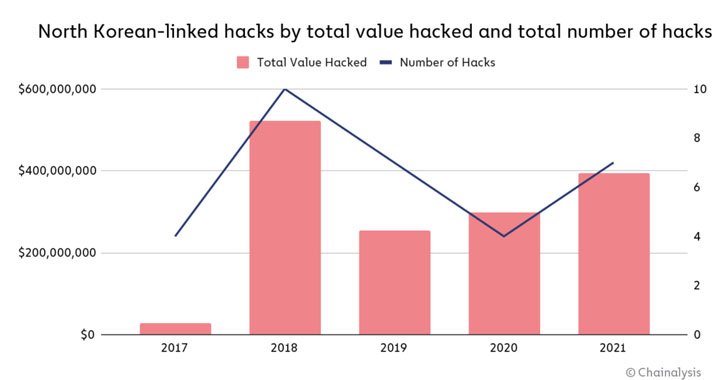
“These assaults targeted mostly investment decision firms and centralized exchanges […] to siphon funds out of these organizations’ internet-related ‘hot’ wallets into DPRK-managed addresses,” the researchers stated. “Once North Korea obtained custody of the cash, they commenced a watchful laundering approach to go over up and money out” by mixers to obscure the trail.
Documented destructive action involving the nation-condition actor have acquire the sort of cyber-enabled heists against international economical establishments, notably the SWIFT banking network hacks in 2015-2016, with recent strategies ensuing in the deployment of a backdoor referred to as AppleJeus that poses as a cryptocurrency investing system to plunder and transfer funds to their accounts.
The SnatchCrypto attacks are no diverse in that they concoct elaborate social engineering schemes to make have confidence in with their targets by posing as reputable enterprise capitalist corporations, only to use bait the victims into opening malware-laced files that retrieve a payload designed to run a malicious executable received over an encrypted channel from a distant server.
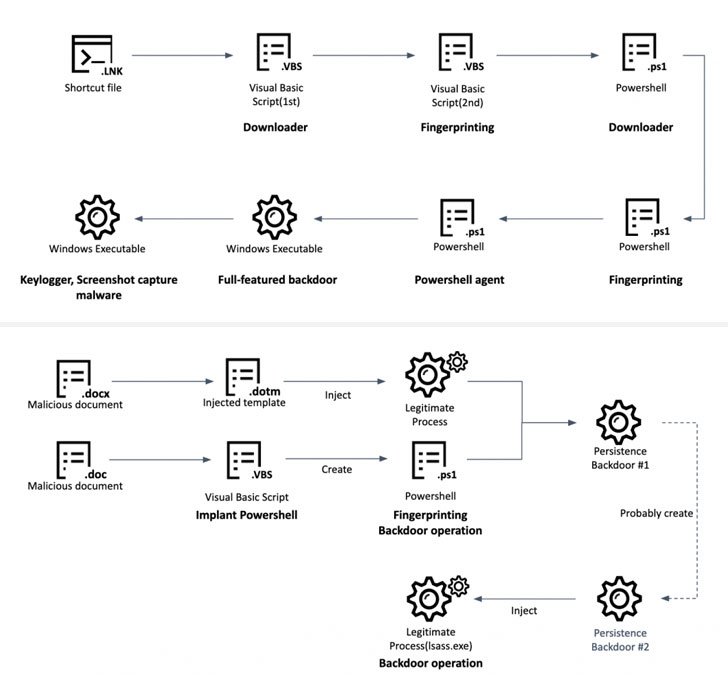
An different technique used to result in the infection chain is the use of Windows shortcut files (“.LNK”) to fetch the subsequent-stage malware, a Visible Basic Script, that then functions a soar off issue to execute a sequence of middleman payloads, just before putting in a complete-showcased backdoor that comes with “enriched” capabilities to seize screenshots, history keystrokes, steal details from Chrome browser, and execute arbitrary commands.

The ultimate aim of the attacks, on the other hand, is to observe economic transactions of the compromised customers and steal cryptocurrency. Ought to a probable goal use a Chrome extension like Metamask to control crypto wallets, the adversary stealthily moves to locally replace the main component of the extension with a bogus model that alerts the operators every single time a significant transfer is kicked off to an additional account.
To siphon the resources, destructive code injection is carried out to intercept and modify the transaction facts on demand from customers. “The attackers modify not only the recipient [wallet] handle, but also press the amount of currency to the restrict, basically draining the account in one transfer,” the researchers defined.
“Cryptocurrency is a closely focused sector when it arrives to cybercrime thanks to the decentralized character of the currencies and the point that, not like with credit score card or lender transfers, the transaction transpires promptly and is impossible to reverse,” Erich Kron, security recognition advocate at KnowBe4, explained in a assertion.
“Nation-states, in particular those underneath strict tariffs or other money limitations, can advantage tremendously by stealing and manipulating cryptocurrency. Several times, a cryptocurrency wallet can comprise several forms of cryptocurrency, earning them a really appealing target,” Kron extra.
Uncovered this write-up intriguing? Abide by THN on Fb, Twitter and LinkedIn to go through much more exceptional articles we article.
Some parts of this article are sourced from:
thehackernews.com


 Three Plugins with Same Bug Put 84K WordPress Sites at Risk
Three Plugins with Same Bug Put 84K WordPress Sites at Risk