An ongoing campaign is targeting Facebook Organization accounts with bogus messages to harvest victims’ qualifications using a variant of the Python-primarily based NodeStealer and potentially just take in excess of their accounts for comply with-on malicious routines.
“The attacks are reaching victims largely in Southern Europe and North The us across diverse segments, led by the manufacturing providers and technology sectors,” Netskope Risk Labs researcher Jan Michael stated in an evaluation posted Thursday.
To start with documented by Meta in May perhaps 2023, NodeStealer originated as a JavaScript malware able of pilfering cookies and passwords from web browsers to compromise Facebook, Gmail, and Outlook accounts.

Palo Alto Networks Unit 42, very last thirty day period, exposed a separate attack wave that took spot in December 2022 using a Python edition of the malware, with select iterations also intended to carry out cryptocurrency theft.
The most recent findings from Netskope counsel the Vietnamese danger actors guiding the operation have likely resumed their attack attempts, not to mention undertake tactics applied by other adversaries working out of the region with the exact same goals.
Just previously this week, Guardio Labs disclosed how fraudulent messages sent via Fb Messenger from a botnet of faux and hijacked individual accounts are getting leveraged to provide ZIP or RAR archive information to provide the stealer malware to unsuspecting recipients.
The similar modus operandi acts as the original vector for the NodeStealer intrusion chains to distribute RAR files hosted on Facebook’s written content delivery network (CDN).
“Illustrations or photos of defective solutions were applied as bait to persuade owners or admins of Facebook company pages to obtain the malware payload,” Michael described.
Approaching WEBINARIdentity is the New Endpoint: Mastering SaaS Security in the Present day Age
Dive deep into the foreseeable future of SaaS security with Maor Bin, CEO of Adaptive Shield. Uncover why identity is the new endpoint. Secure your place now.
Supercharge Your Techniques
These archives occur equipped with a batch script that, when executed, opens the Chrome web browser and normally takes the target to a benign web website page. But in the background, a PowerShell command is operate to retrieve additional payloads, which include the Python interpreter and the NodeStealer malware.
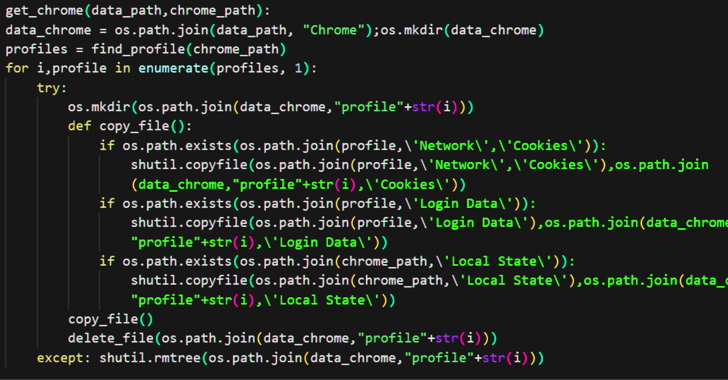
The stealer, aside from capturing qualifications and cookies – irrespective of whether it is from Fb or not – from numerous web browsers, is created to acquire technique metadata and exfiltrate the information around Telegram.
“As opposed to before variants, the new NodeStealer variant takes advantage of batch documents to obtain and run Python scripts, and steal qualifications and cookies from numerous browsers and for various web sites,” Michael reported.
“This marketing campaign may be a doorway to a far more targeted attack later on considering that they have by now gathered helpful details. Attackers who have stolen Fb cookies and credentials can use them to consider more than the account, make fraudulent transactions leveraging the legit business enterprise webpage.”
Located this posting fascinating? Comply with us on Twitter and LinkedIn to browse additional exceptional content we publish.
Some parts of this article are sourced from:
thehackernews.com

 Cybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads
Cybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads