Cybercriminals are significantly leveraging malicious LNK data files as an first access method to download and execute payloads this kind of as Bumblebee, IcedID, and Qakbot.
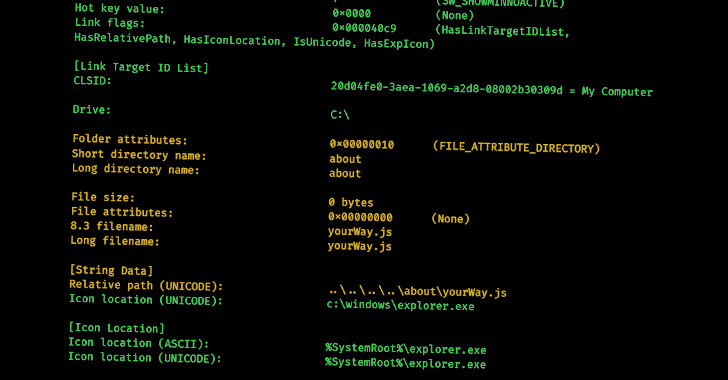
A modern analyze by cybersecurity experts has proven that it is possible to identify interactions concerning unique menace actors by examining the metadata of malicious LNK information, uncovering information this sort of as the unique applications and approaches utilized by distinct teams of cybercriminals, as very well as possible inbound links in between seemingly unrelated assaults.
“With the raising usage of LNK documents in attack chains, it truly is rational that risk actors have started developing and applying instruments to create such files,” Cisco Talos researcher Guilherme Venere claimed in a report shared with The Hacker Information.
This consists of instruments like NativeOne’s mLNK Builder and Quantum Builder, which let subscribers to generate rogue shortcut files and evade security methods.
Some of the major malware households that have utilised LNK data files for original access contain Bumblebee, IcedID, and Qakbot, with Talos pinpointing connections among Bumblebee and IcedID as perfectly as Bumblebee and Qakbot by inspecting the artifacts’ metadata.
Specifically, multiple samples of LNK files primary to IcedID and Qakbot infections and all those that ended up utilised in various Bumblebee strategies have all been discovered to share the very same Drive Serial Range.
LNK files have also been employed by innovative persistent menace (APT) groups like Gamaredon (aka Armageddon) in its attacks aimed at Ukrainian federal government entities.
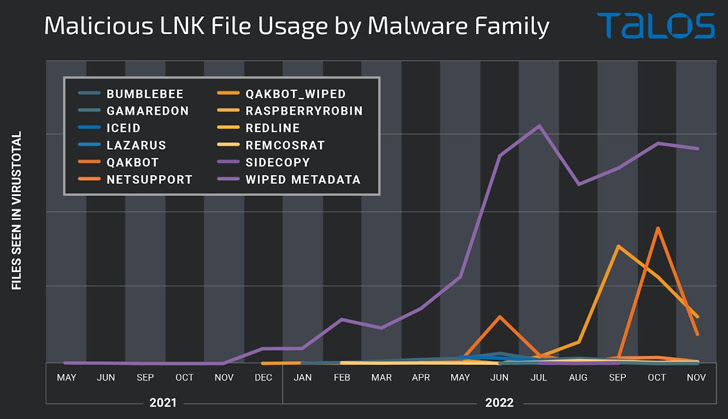
The noticeable spike in strategies applying destructive shortcuts is noticed as a reactive reaction to Microsoft’s choice to disable macros by default in Office paperwork downloaded from the Internet, prompting menace actors to embrace choice attachment kinds and shipping mechanisms to distribute malware.
Latest analyses from Talos and Trustwave have disclosed how APT actors and commodity malware families alike are weaponizing Excel add-in (XLL) information and Publisher macros to fall remote entry trojans on compromised devices.
What’s extra, danger actors have been noticed using benefit of rogue Google Adverts and research engine optimization (Search engine optimization) poisoning to thrust off-the-shelf malware like BATLOADER, IcedID, Rhadamanthys Stealer, and Vidar to victims searching for a slew of respectable software package.
BATLOADER, related with an intrusion set tracked by Pattern Micro as Drinking water Minyades, is an “evasive and evolutionary malware” which is able of installing more malware, such as Cobalt Strike, Qakbot, Raccoon Stealer, RedLine Stealer, SmokeLoader, Vidar, and ZLoader.
“Attackers are imitating the internet websites of well-known application initiatives to trick victims into infecting their computers and getting look for engine adverts to travel site visitors there,” HP Wolf Security researcher Patrick Schläpfer stated.
Observed this post fascinating? Observe us on Twitter and LinkedIn to go through additional unique content we publish.
Some parts of this article are sourced from:
thehackernews.com

 6 Types of Risk Assessment Methodologies + How to Choose
6 Types of Risk Assessment Methodologies + How to Choose