The risk actor driving the BlackRock and ERMAC Android banking trojans has unleashed still an additional malware for rent referred to as Hook that introduces new capabilities to accessibility documents saved in the gadgets and produce a remote interactive session.
ThreatFabric, in a report shared with The Hacker Information, characterised Hook as a novel ERMAC fork that is advertised for sale for $7,000 per month even though featuring “all the capabilities of its predecessor.”
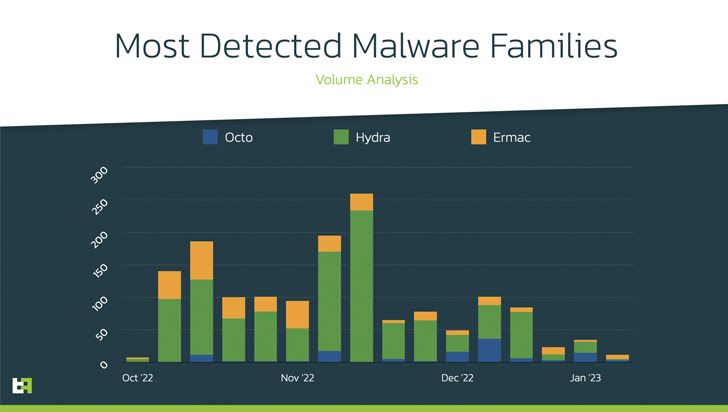
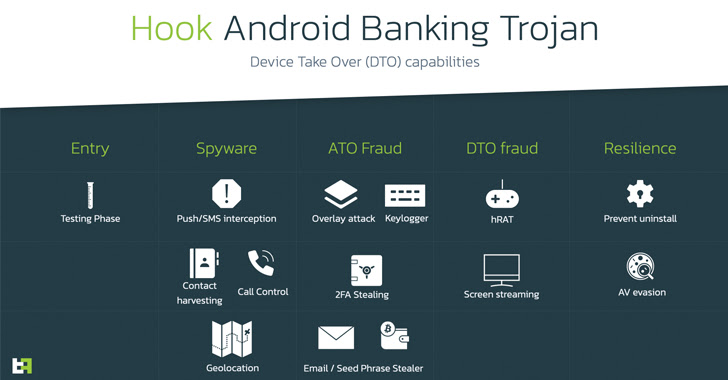
“In addition, it also provides to its arsenal Distant Entry Tooling (RAT) abilities, joining the ranks of households such as Octo and Hydra, which are able doing a whole Product Just take Above (DTO), and finish a total fraud chain, from PII exfiltration to transaction, with all the intermediate techniques, with out the need of additional channels,” the Dutch cybersecurity organization said.
A the greater part of the money apps focused by the malware are found in the U.S., Spain, Australia, Poland, Canada, Turkey, the U.K., France, Italy, and Portugal.
Hook is the handiwork of a threat actor regarded as DukeEugene and represents the newest evolution of ERMAC, which was first disclosed in September 2021 and is primarily based on another trojan named Cerberus that experienced its supply code leaked in 2020.
“Ermac has normally been driving Hydra and Octo in terms of capabilities and features,” ThreatFabric researcher Dario Durando explained to The Hacker News by way of email. “This is also recognised amid danger actors, who favor these two family members above Ermac.”
“The absence of some type of RAT abilities is a big issue for a modern-day Android Banker, as it does not deliver the possibility to complete Product Acquire About (DTO), which is the fraud methodology that is most likely to be thriving and not detected by fraud scoring engines or fraud analysts. This is most probably what induced the growth of this new malware variant.”
Like other Android malware of its ilk, the malware abuses Android’s accessibility solutions APIs to carry out overlay assaults and harvest all types of sensitive facts this kind of as contacts, call logs, keystrokes, two-issue authentication (2FA) tokens, and even WhatsApp messages.
It also athletics an expanded list of apps to incorporate ABN AMRO and Barclays, whilst the malicious samples them selves masquerade as the Google Chrome web browser to dupe unsuspecting consumers into downloading the malware:
- com.lojibiwawajinu.guna
- com.damariwonomiwi.docebi
- com.yecomevusaso.pisifo
Among the the other key attributes to be additional to Hook is the means to remotely perspective and interact with the monitor of the contaminated unit, attain information, extract seed phrases from crypto wallets, and monitor the phone’s locale, blurring the line amongst spy ware and banking malware.
ThreatFabric claimed the Hook artifacts observed so far in a tests stage, but noted it could be shipped by way of phishing campaigns, Telegram channels, or in the sort of Google Enjoy Retail store dropper apps.
“The most important disadvantage of building a new malware is normally getting sufficient believe in by other actors, but with the standing of DukeEugene amongst criminals, it is extremely likely that this will not be an issue for Hook,” Durando mentioned.
Identified this posting fascinating? Comply with us on Twitter and LinkedIn to study more distinctive content we submit.
Some parts of this article are sourced from:
thehackernews.com

 New Research Delves into the World of Malicious LNK Files and Hackers Behind Them
New Research Delves into the World of Malicious LNK Files and Hackers Behind Them