An unnamed authorities entity involved with the United Arab Emirates (U.A.E.) was focused by a most likely Iranian danger actor to breach the victim’s Microsoft Exchange Server with a “straightforward still productive” backdoor dubbed PowerExchange.
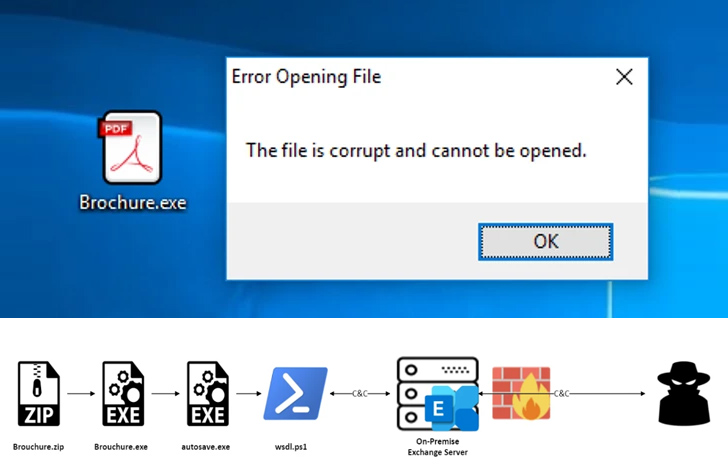
In accordance to a new report from Fortinet FortiGuard Labs, the intrusion relied on email phishing as an initial accessibility pathway, leading to the execution of a .NET executable contained with a ZIP file attachment.
The binary, which masquerades as a PDF document, functions as a dropper to execute the remaining payload, which then launches the backdoor.
PowerExchange, prepared in PowerShell, employs textual content data files connected to e-mails for command-and-regulate (C2) interaction. It allows the risk actor to operate arbitrary payloads and add and down load files from and to the program.
The customized implant achieves this by making use of the Trade Web Providers (EWS) API to link to the victim’s Trade Server and takes advantage of a mailbox on the server to send and receive encoded instructions from its operator.
“The Trade Server is accessible from the internet, preserving C2 communication to external servers from the equipment in the organizations,” Fortinet scientists explained. “It also functions as a proxy for the attacker to mask himself.”
That claimed, it really is at this time not identified how the danger actor managed to attain the area credentials to hook up to the goal Exchange Server.
Fortinet’s investigation also uncovered Exchange servers that have been backdoored with a number of web shells, a single of which is known as ExchangeLeech (aka System.Web.ServiceAuthentication.dll), to attain persistent distant entry and steal consumer credentials.
Impending WEBINARZero Rely on + Deception: Discover How to Outsmart Attackers!
Find how Deception can detect advanced threats, cease lateral movement, and enrich your Zero Have confidence in system. Join our insightful webinar!
Preserve My Seat!
PowerExchange is suspected to be an upgraded edition of TriFive, which was beforehand employed by the Iranian nation-stage actor APT34 (aka OilRig) in intrusions focusing on government organizations in Kuwait.
Furthermore, conversation by means of internet-dealing with Exchange servers is a tried-and-tested tactic adopted by the OilRig actors, as observed in the case of Karkoff and MrPerfectionManager.
“Employing the victim’s Trade server for the C2 channel allows the backdoor to mix in with benign visitors, therefore ensuring that the menace actor can easily steer clear of virtually all network-centered detections and remediations within and outdoors the target organization’s infrastructure,” the researchers mentioned.
Found this report attention-grabbing? Comply with us on Twitter and LinkedIn to read through additional distinctive material we post.
Some parts of this article are sourced from:
thehackernews.com


 Alert: Brazilian Hackers Targeting Users of Over 30 Portuguese Banks
Alert: Brazilian Hackers Targeting Users of Over 30 Portuguese Banks