A latest Hive ransomware attack carried out by an affiliate concerned the exploitation of “ProxyShell” vulnerabilities in the Microsoft Exchange Server that ended up disclosed very last year to encrypt an unnamed customer’s network.
“The actor managed to achieve its malicious aims and encrypt the natural environment in considerably less than 72 hours from the original compromise,” Varonis security researcher, Nadav Ovadia, claimed in a submit-mortem investigation of the incident.
Hive, which was very first observed in June 2021, follows the lucrative ransomware-as-a-assistance (RaaS) plan adopted by other cybercriminal groups in new a long time, enabling affiliates to deploy the file-encrypting malware right after attaining a foothold into their victims’ networks.

ProxyShell — tracked as CVE-2021-31207, CVE-2021-34523, and CVE-2021-34473 — will involve a mix of security feature bypass, privilege escalation, and distant code execution in the Microsoft Exchange Server, effectively granting the attacker the capacity to execute arbitrary code on affected servers.
The issues have been tackled by Microsoft as part of its Patch Tuesday updates for April and May well 2021.
In this situation, successful exploitation of the flaws permitted the adversary to deploy web shells on the compromised server, employing them to run malicious PowerShell code with Procedure privileges to develop a new backdoor administrator user, hijack the domain admin account, and conduct lateral movement.
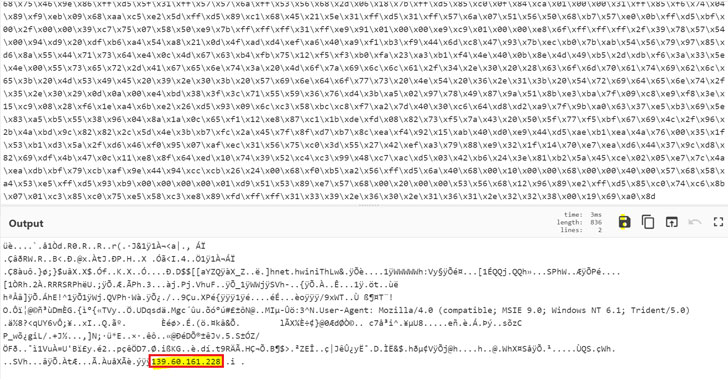
The web shells made use of in the attack are claimed to have been sourced from a community git repository and given filenames made up of a random mix of people to evade detection, Ovadia explained. Also executed was an added obfuscated PowerShell script that’s part of the Cobalt Strike framework.
From there, the danger actor moved to scan the network for worthwhile files, in advance of proceeding to deploy the Golang ransomware executable (named “Windows.exe”) to entire the encryption course of action and exhibit the ransom notice to the target.
Other functions carried out by the malware consist of deleting shadow copies, turning off security solutions, and clearing Windows event logs to keep away from detection, protect against restoration, and guarantee that the encryption occurs devoid of any hiccup.
If just about anything, the conclusions are but a different indicator that patching for recognised vulnerabilities is crucial to thwarting cyberattacks and other nefarious things to do.
“Ransomware assaults have grown considerably about the earlier a long time and keep on being the preferred strategy of menace actors aiming to improve revenue,” Ovadia said. “It may perhaps possibly hurt an organization’s track record, disrupt typical operations and guide to non permanent, and quite possibly long-lasting, loss of sensitive information.”
Discovered this article fascinating? Observe THN on Facebook, Twitter and LinkedIn to read much more exclusive articles we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Two-Thirds of Global Banks Report Surge in Destructive Attacks
Two-Thirds of Global Banks Report Surge in Destructive Attacks