A lately identified wave of malware assaults has been spotted working with a variety of tactics to enslave inclined equipment with quick-to-guess administrative qualifications to co-decide them into a network with the objective of illegally mining cryptocurrency.
“The malware’s primary tactic is to spread by taking benefit of vulnerable systems and weak administrative credentials. After they’ve been contaminated, these techniques are then employed to mine cryptocurrency,” Akamai security researcher Larry Cashdollar explained in a produce-up posted final week.
The PHP malware — codenamed “Capoae” (small for “Сканирование,” the Russian phrase for “Scanning”) — is explained to be shipped to the hosts via a backdoored addition to a WordPress plugin named “download-keep an eye on,” which receives installed after properly brute-forcing WordPress admin qualifications. The assaults also involve the deployment of a Golang binary with decryption features, with the obfuscated payloads retrieved by leveraging the trojanized plugin to make a GET ask for from an actor-controlled area.
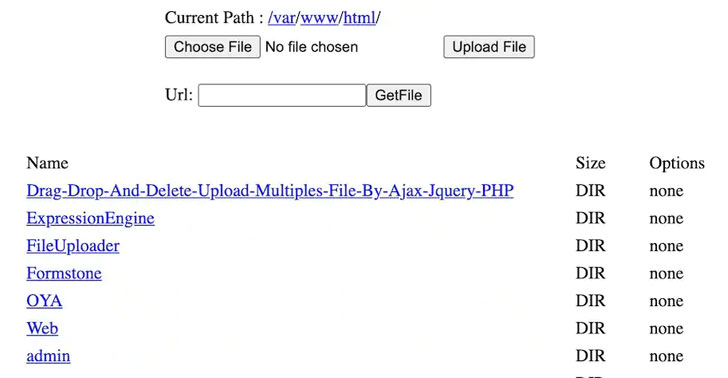
Also provided is a feature to decrypted and execute supplemental payloads, while the Golang binary usually takes gain of exploits for a number of distant code execution flaws in Oracle WebLogic Server (CVE-2020-14882), NoneCms (CVE-2018-20062), and Jenkins (CVE-2019-1003029 and CVE-2019-1003030) to brute force its way into programs managing SSH and in the end launch the XMRig mining application.

What’s a lot more, the attack chain stands out for its persistence methods, which involves deciding upon a reputable-on the lookout program path on the disk where process binaries are probably to be uncovered as perfectly as generating a random 6-character filename which is then subsequently employed to copy alone into the new site on the method just before deleting the malware upon execution.
“The Capoae campaign’s use of many vulnerabilities and strategies highlights just how intent these operators are on finding a foothold on as lots of machines as achievable,” Cashdollar explained. “The very good information is, the identical tactics we recommend for most corporations to keep devices and networks protected nonetheless utilize in this article.”
“Don’t use weak or default qualifications for servers or deployed apps,” Cashdollar included. “Make certain you might be preserving these deployed applications up to day with the most up-to-date security patches and check in on them from time to time. Maintaining an eye out for larger than ordinary process useful resource use, odd/unexpected functioning procedures, suspicious artifacts and suspicious access log entries, etcetera., will assistance you perhaps detect compromised equipment.”
Found this article intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to read far more exclusive articles we post.
Some parts of this article are sourced from:
thehackernews.com

 Farming Group Warns of Supply Chain Chaos After Ransomware Attack
Farming Group Warns of Supply Chain Chaos After Ransomware Attack