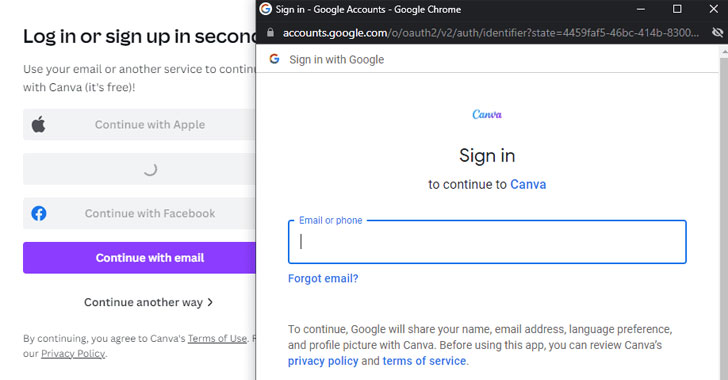
A novel phishing method named browser-in-the-browser (BitB) attack can be exploited to simulate a browser window within the browser in purchase to spoof a reputable domain, therefore building it possible to phase convincing phishing attacks.
According to penetration tester and security researcher, who goes by the deal with mrd0x_, the system normally takes edge of third-occasion one indicator-on (SSO) solutions embedded on internet websites these as “Signal in with Google” (or Fb, Apple, or Microsoft).
When the default actions when a person tries to indicator in by way of these solutions is to be greeted by a pop-up window to total the authentication process, the BitB attack aims to replicate this overall course of action utilizing a blend of HTML and CSS code to generate an entirely fabricated browser window.
“Incorporate the window design and style with an iframe pointing to the malicious server hosting the phishing web site, and it can be fundamentally indistinguishable,” mrd0x_ said in a complex produce-up printed past 7 days. “JavaScript can be very easily applied to make the window surface on a url or button click on, on the webpage loading and so on.”
While this system drastically tends to make it easier to mount successful social engineering strategies, it truly is really worth noting that possible victims have to have to be redirected to a phishing area that can exhibit this sort of a bogus authentication window for credential harvesting.
“But as soon as landed on the attacker-owned website, the person will be at simplicity as they sort their qualifications absent on what seems to be the respectable site (simply because the reputable URL says so),” mrd0x_ added.
Located this write-up exciting? Observe THN on Fb, Twitter and LinkedIn to browse much more exceptional written content we submit.
Some parts of this article are sourced from:
thehackernews.com


 The Morning After: Russian cosmonauts boarded the ISS in blue and yellow jumpsuits
The Morning After: Russian cosmonauts boarded the ISS in blue and yellow jumpsuits