Scientists have exposed a new targeted email campaign aimed at French entities in the development, authentic estate, and governing administration sectors that leverages the Chocolatey Windows deal manager to deliver a backdoor termed Serpent on compromised devices.
Organization security company Proofpoint attributed the attacks to a very likely highly developed danger actor dependent on the tactics and the victimology styles observed. The final aim of the campaign stays presently unidentified.
“The menace actor tried to set up a backdoor on a probable victim’s gadget, which could allow distant administration, command and control (C2), facts theft, or provide other extra payloads,” Proofpoint scientists reported in a report shared with The Hacker News.
The phishing entice that triggers the an infection sequence would make use of a resume-themed subject line, with the hooked up macro-embedded Microsoft Term document masquerading as facts associated to the European Union’s Normal Data Safety Regulation (GDPR).
Enabling the macros benefits in its execution, which retrieves a seemingly harmless graphic file hosted on a distant server but essentially is made up of a Foundation64-encoded PowerShell script that’s obscured utilizing steganography, a minimal-employed process of concealing destructive code in an picture or audio in get to circumvent detection.
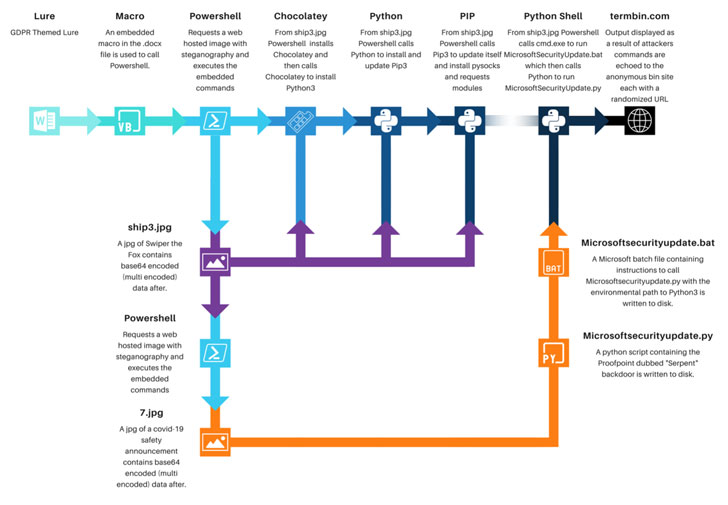
The PowerShell script, in transform, is engineered to put in the Chocolatey utility on the Windows machine, which is then used to set up the Python deal installer pip, the latter of which functions as conduit to set up the PySocks proxy library.
Also retrieved by the identical PowerShell script is a different impression file from the identical distant server that involves the camouflaged Python backdoor dubbed Serpent, which will come with abilities to execute commands transmitted from the C2 server.
In addition to steganography, the use of commonly acknowledged resources these kinds of as Chocolatey as an original payload for comply with-on deployment of legitimate Python deals is an attempt to keep under the radar and not be flagged as a risk, Proofpoint reported.
The attacks have not unearthed associations with a previously discovered actor or group, but are suspected to be the operate of a subtle hacking crew.
“This is a novel application of a wide range of systems that are frequently legitimately applied within organizations,” Sherrod DeGrippo, vice president of menace research and detection at Proofpoint, reported in a assertion.
“It capitalizes on numerous organizations’, precisely specialized groups, motivation to let their users to be ‘self-sufficient’ in regards to self-tooling and offer professionals. Furthermore, the use of steganography is strange and something we do not see on a regular basis.”
Observed this short article exciting? Stick to THN on Facebook, Twitter and LinkedIn to read through a lot more distinctive content we publish.
Some parts of this article are sourced from:
thehackernews.com


 ‘CryptoRom’ Crypto Scam Abusing iPhone Features to Target Mobile Users
‘CryptoRom’ Crypto Scam Abusing iPhone Features to Target Mobile Users