At minimum six distinctive Russia-aligned actors launched no a lot less than 237 cyberattacks against Ukraine from February 23 to April 8, like 38 discrete destructive attacks that irrevocably destroyed information in hundreds of programs throughout dozens of companies in the place.
“Collectively, the cyber and kinetic actions perform to disrupt or degrade Ukrainian government and armed forces features and undermine the public’s trust in people identical institutions,” the company’s Electronic Security Device (DSU) said in a particular report.
The main malware families that have been leveraged for destructive exercise as component of Russia’s relentless electronic assaults contain: WhisperGate, HermeticWiper (FoxBlade aka KillDisk), HermeticRansom (SonicVote), IssacWiper (Lasainraw), CaddyWiper, DesertBlade, DoubleZero (FiberLake), and Industroyer2.

WhisperGate, HermeticWiper, IssacWiper, and CaddyWiper are all knowledge wipers made to overwrite knowledge and render machines unbootable, though DoubleZero is a .NET malware able of details deletion. DesertBlade, also a info wiper, is explained to have been introduced against an unnamed broadcasting organization in Ukraine on March 1.
SonicVote, on the other hand, is a file encryptor detected in conjunction with HermeticWiper to disguise the intrusions as a ransomware attack, though Industroyer2 especially targets operational technology to sabotage critical industrial manufacturing and procedures.
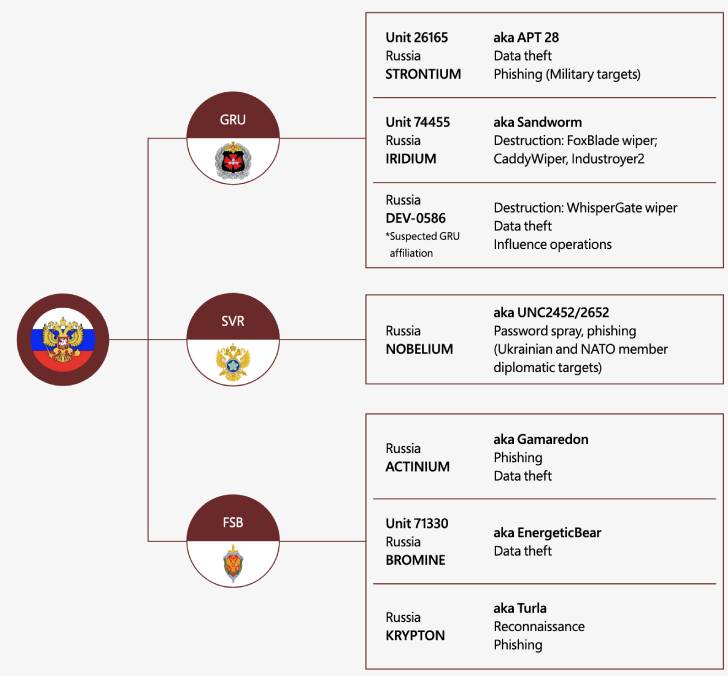
Microsoft attributed HermeticWiper, CaddyWiper, and Industroyer2 with moderate self-confidence to a Russian condition-sponsored actor named Sandworm (aka Iridium). The WhisperGate assaults have been tied to a earlier unfamiliar cluster dubbed DEV-0586, which is believed to be affiliated to Russia’s GRU military intelligence.
32% of the total 38 destructive attacks are estimated to have singled out Ukrainian government organizations at the countrywide, regional and city amounts, with over 40% of the assaults aimed at organizations in critical infrastructure sectors in the nations.

In addition, Microsoft reported it noticed Nobelium, the danger actor blamed for the 2020 SolarWinds source chain attack, making an attempt to breach IT companies serving govt shoppers in NATO member states, applying the accessibility to siphon data from Western overseas policy companies.

Other destructive assaults include phishing strategies concentrating on military entities (Fancy Bear aka Strontium) and governing administration officials (Primitive Bear aka Actinium) as effectively as details theft (Energetic Bear aka Bromine) and reconnaissance (Venomous Bear aka Krypton) operations.
“Russia’s use of cyberattacks seems to be strongly correlated and in some cases right timed with its kinetic navy functions targeting companies and establishments crucial for civilians,” Tom Burt, corporate vice president of buyer security and trust, reported.
“Provided Russian danger actors have been mirroring and augmenting armed forces steps, we feel cyberattacks will proceed to escalate as the conflict rages. It can be likely the assaults we’ve noticed are only a fraction of activity concentrating on Ukraine.”
Observed this write-up intriguing? Abide by THN on Fb, Twitter and LinkedIn to go through a lot more unique articles we publish.
Some parts of this article are sourced from:
thehackernews.com


