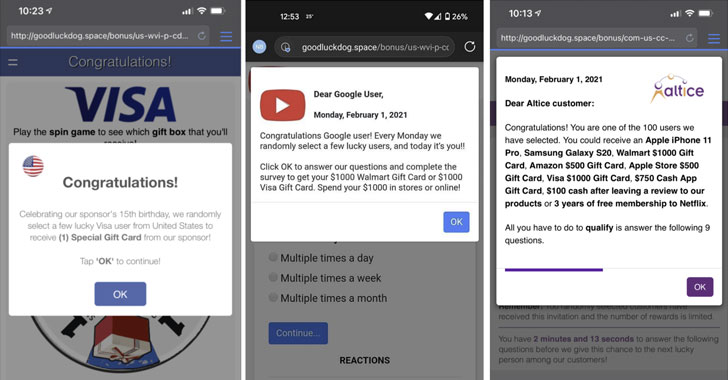
A malvertising team identified as “ScamClub” exploited a zero-working day vulnerability in WebKit-based mostly browsers to inject destructive payloads that redirected users to fraudulent web-sites reward card scams.
The attacks, 1st spotted by advertisement security organization Confiant in late June 2020, leveraged a bug (CVE-2021–1801) that permitted destructive functions to bypass the iframe sandboxing plan in the browser engine that powers Safari and Google Chrome for iOS and operate destructive code.

Specifically, the system exploited the manner how WebKit handles JavaScript party listeners, consequently producing it attainable to split out of the sandbox linked with an ad’s inline body aspect even with the presence of “let-top rated-navigation-by-consumer-activation” attribute that explicitly forbids any redirection until the click on party occurs inside the iframe.
To exam this speculation, the scientists set about developing a uncomplicated HTML file containing a cross-origin sandboxed iframe and a button outside the house it that triggered an celebration to obtain the iframe and redirect the clicks to rogue internet sites.
“The […] button is outside the house of the sandboxed body after all,” Confiant researcher Eliya Stein claimed. “Even so, if it does redirect, that signifies we have a browser security bug on our arms, which turned out to be the circumstance when examined on WebKit dependent browsers, namely Safari on desktop and iOS.”
Subsequent liable disclosure to Apple on June 23, 2020, the tech big patched WebKit on December 2, 2020, and subsequently addressed the issue “with improved iframe sandbox enforcement” as aspect of security updates unveiled previously this month for iOS 14.4 and macOS Major Sur.
Confiant explained the operators of ScamClub have shipped more than 50 million destructive impressions more than the past 90 times, with as lots of as 16MM impacted ads becoming served in a single working day.
“On the strategies facet, this attacker traditionally favors what we refer to as a ‘bombardment’ system,” Stein elaborated.
“As a substitute of attempting to fly less than the radar, they flood the advert tech ecosystem with tons of horrendous demand from customers effectively conscious that the vast majority of it will be blocked by some variety of gatekeeping, but they do this at very superior volumes in the hopes that the tiny share that slips by way of will do sizeable problems.”
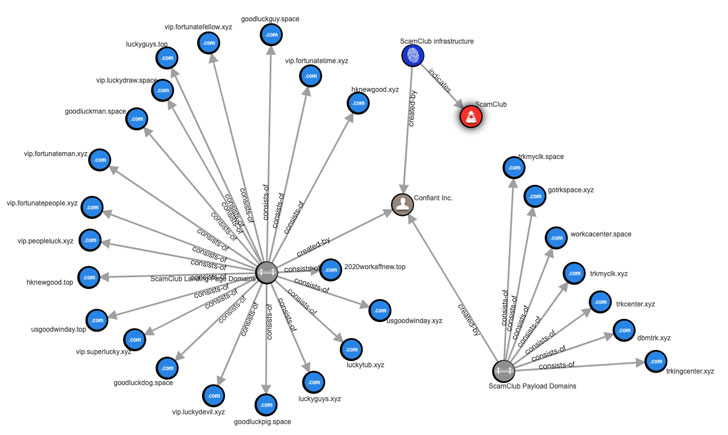
Confiant has also revealed a list of internet sites used by the ScamClub team to run its new rip-off marketing campaign.
Observed this post exciting? Abide by THN on Facebook, Twitter and LinkedIn to browse additional unique information we article.
Some parts of this article are sourced from:
thehackernews.com

 Epic Games is behind North Dakota’s anti-App Store bill
Epic Games is behind North Dakota’s anti-App Store bill