Cybersecurity researchers have uncovered a selection of malicious deals in the NPM registry exclusively concentrating on a range of prominent businesses dependent in Germany to carry out provide chain attacks.
“When compared with most malware uncovered in the NPM repository, this payload would seem specially dangerous: a very-innovative, obfuscated piece of malware that functions as a backdoor and will allow the attacker to choose complete regulate over the infected machine,” scientists from JFrog said in a new report.
The DevOps enterprise said that evidence points to it being possibly the get the job done of a innovative menace actor or a “extremely intense” penetration examination.
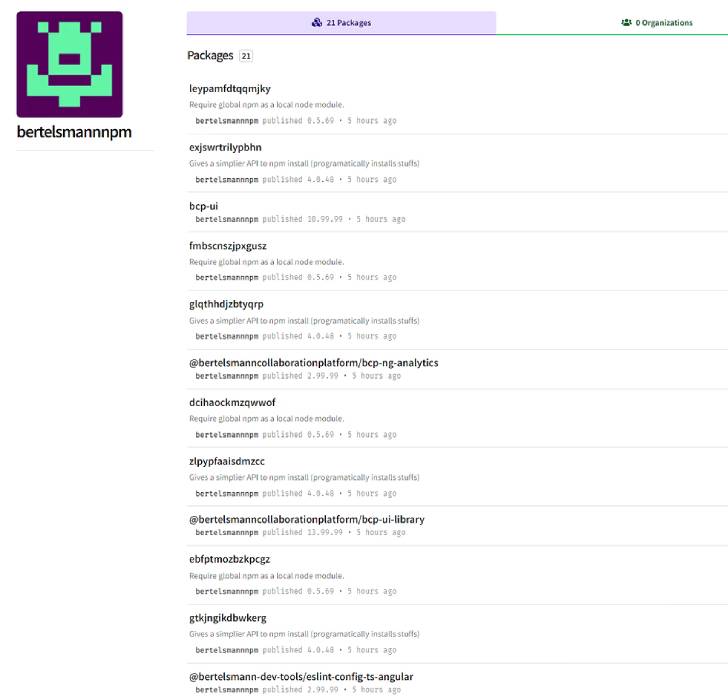
All the rogue packages, most of which have due to the fact been removed from the repository, have been traced to 4 “maintainers” – bertelsmannnpm, boschnodemodules, stihlnodemodules, and dbschenkernpm — indicating an endeavor to impersonate legit companies like Bertelsmann, Bosch, Stihl, and DB Schenker.
Some of the package deal names are mentioned to be very specific, raising the possibility that the adversary managed to determine the libraries hosted in the companies’ interior repositories with the objective of staging a dependency confusion attack.
The results establish on a report from Snyk late previous month that in depth 1 of the offending offers, “gxm-reference-web-auth-server,” noting that the malware is concentrating on an not known organization that has the identical offer in their private registry.
“The attacker(s) most likely experienced information and facts about the existence of this sort of a package deal in the company’s private registry,” the Snyk security exploration crew claimed.
Contacting the implant an “in-house advancement,” JFrog pointed out that the malware harbors two elements, a dropper that sends data about the contaminated equipment to a distant telemetry server ahead of decrypting and executing a JavaScript backdoor.
The backdoor, while missing a persistence mechanism, is made to acquire and execute instructions sent from a challenging-coded command-and-handle server, evaluate arbitrary JavaScript code, and add data files back again to the server.
“The attack is remarkably qualified and depends on difficult-to-get insider information,” the researchers said. But on the other hand, “the usernames established in the NPM registry did not attempt to hide the focused company.”
Discovered this short article fascinating? Follow THN on Fb, Twitter and LinkedIn to study a lot more exclusive content we submit.
Some parts of this article are sourced from:
thehackernews.com


 Sony's Xperia 1 IV smartphone features 'the world's first true optical zoom lens'
Sony's Xperia 1 IV smartphone features 'the world's first true optical zoom lens'