Microsoft and authentication solutions service provider Okta stated they are investigating claims of a probable breach alleged by the LAPSUS$ extortionist gang.
The improvement, which was very first claimed by Vice and Reuters, arrives following the cyber criminal team posted screenshots and supply code of what it reported have been the companies’ inside assignments and units on its Telegram channel.
The leaked 37GB archive displays that the team might have accessed the repositories associated to Microsoft’s Bing, Bing Maps, and Cortana, with the images highlighting Okta’s Atlassian suite and in-house Slack channels.

“For a support that powers authentication devices to many of the biggest organizations (and FEDRAMP permitted) I consider these security measures are pretty bad,” the hacking cartel wrote on Telegram.
On top of this, the group alleged that it breached LG Electronics (LGE) for the “2nd time” in a year.
Invoice Demirkapi, a security researcher at Zoom, observed that “LAPSUS$ seems to have gotten accessibility to the Cloudflare tenant with the capacity to reset employee passwords,” incorporating the company “failed to publicly admit any breach for at the very least two months.”
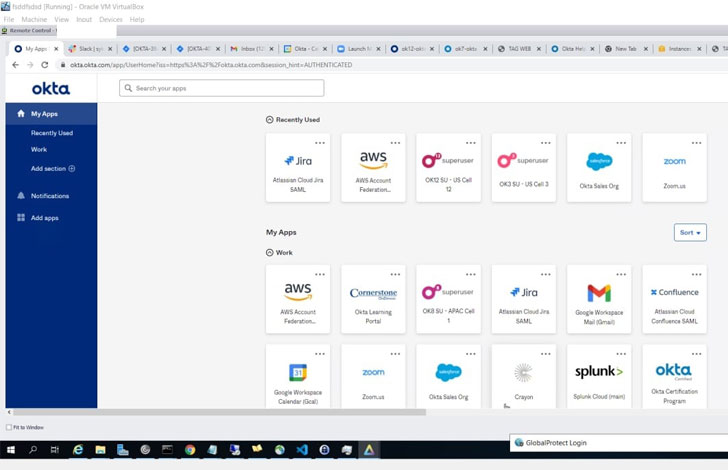
LAPSUS$ has given that clarified that it did not breach Okta’s databases and that “our target was ONLY on Okta customers.” This could pose critical implications for other government agencies and companies that rely on Okta to authenticate user access to inside devices.
“In late January 2022, Okta detected an endeavor to compromise the account of a 3rd-occasion customer support engineer operating for one particular of our subprocessors. The issue was investigated and contained by the subprocessor,” Okta CEO Todd McKinnon reported in a tweet.
“We consider the screenshots shared on the internet are linked to this January celebration. Centered on our investigation to day, there is no proof of ongoing malicious activity outside of the action detected in January,” McKinnon extra.
Cloudflare, in response, claimed it really is resetting the Okta qualifications of staff who have altered their passwords in the previous 4 months, out of abundance of warning.

Unlike traditional ransomware groups that abide by the double extortion playbook of thieving facts from a sufferer and then encrypting that info in return for a payment, the new entrant to the risk landscape focuses extra on knowledge theft and using it to blackmail the targets.
In the months due to the fact it went lively in late December 2021, the cybercrime gang has racked up a prolonged list of higher-profile victims, which includes Impresa, NVIDIA, Samsung, Mercado Libre, Vodafone, and most just lately Ubisoft.
“Any prosperous attack against a service company or program developer can have even further impact past the scope of that preliminary attack,” Mike DeNapoli, lead security architect of Cymulate, said in a assertion. “End users of the products and services and platforms ought to be alerted to the truth that there are feasible source-chain attacks that will have to have to be defended towards.”
Discovered this short article interesting? Comply with THN on Fb, Twitter and LinkedIn to read through additional distinctive material we article.
Some parts of this article are sourced from:
thehackernews.com


 Serpent Backdoor Slithers into Orgs Using Chocolatey Installer
Serpent Backdoor Slithers into Orgs Using Chocolatey Installer