Hackers with suspected ties to Iran are actively concentrating on academia, govt businesses, and tourism entities in the Center East and neighboring areas as element of an espionage marketing campaign aimed at information theft.
Dubbed “Earth Vetala” by Pattern Micro, the most up-to-date discovering expands on past exploration published by Anomali past month, which observed evidence of malicious activity aimed at UAE and Kuwait federal government companies by exploiting ScreenConnect remote administration software.
The cybersecurity agency joined the ongoing assaults with moderate self-assurance to a menace actor commonly tracked as MuddyWater, an Iranian hacker team acknowledged for its offensives mostly against Middle Jap nations.
Earth Vetala is explained to have leveraged spear-phishing e-mails containing embedded one-way links to a popular file-sharing provider known as Onehub to distribute malware that ranged from password dumping utilities to tailor made backdoors, ahead of initiating communications with a command-and-manage (C2) server to execute obfuscated PowerShell scripts.
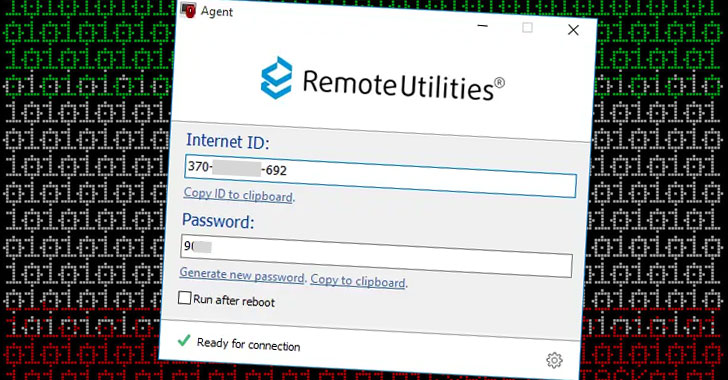
The back links them selves immediate victims to a .ZIP file that incorporates a genuine distant administration software package formulated by RemoteUtilities, which is capable of downloading and uploading information, capturing screenshots, browsing information and directories, and executing and terminating procedures.
 Affected Countries
Affected Countries
Noting that the strategies and approaches concerning the two campaigns that distribute RemoteUtilities and ScreenConnect are broadly related, Development Micro said the targets of the new wave of assaults are largely organizations positioned in Azerbaijan, Bahrain, Israel, Saudi Arabia, and the UAE.
In one unique occasion involving a compromised host in Saudi Arabia, the researchers discovered that the adversary tried to unsuccessfully configure SharpChisel — a C# wrapper for a TCP/UDP tunneling tool known as chisel — for C2 communications, just before downloading a remote obtain tool, a credential stealer, and a PowerShell backdoor able of executing arbitrary remote commands.
“Earth Vetala signifies an attention-grabbing risk,” Craze Micro explained. “While it possesses distant accessibility capabilities, the attackers seem to deficiency the abilities to use all of these equipment properly. This is surprising because we feel this attack is connected to the MuddyWater risk actors — and in other connected strategies, the attackers have demonstrated greater stages of specialized ability.”
Identified this write-up interesting? Follow THN on Fb, Twitter and LinkedIn to read extra exclusive content we article.
Some parts of this article are sourced from:
thehackernews.com

 FTC Busts $110m Charity Fraud Operation
FTC Busts $110m Charity Fraud Operation