Claroty reviews that adversaries, CISOs and researchers have all turned their attention to acquiring critical security bugs in ICS networks.
It is on: Adversaries, CISOs and scientists are all at the same time associated in a frantic race to find cybersecurity vulnerabilities hiding inside of industrial networks, in accordance to the newest Biannual ICS Risk and Vulnerability report from Claroty.
The report analyzed all publicly disclosed vulnerabilities in ICS networks in the 2nd 50 % of 2020 and found a virtually 33 p.c raise in ICS disclosures in excess of 2018, both from corporations like Claroty and from unbiased scientists.
Industries with the most disclosures incorporate critical infrastructure parts like critical production, strength, drinking water, wastewater and business amenities.
Worse nonetheless, far more than 71 per cent of the bugs ended up remotely exploitable, and just about every disclosure in the second half of 2020 ranked highly on MITRE’s 2020 CWE Leading 25 Most Unsafe Computer software Weaknesses list since they had been easy to exploit and probably catastrophic, the report stated.
ICS Cybersecurity Appeals to Researchers
For the duration of the second 50 % of 2020, Claroty counted 449 vulnerabilities claimed throughout 59 ICS sellers and there ended up 893 for the complete 12 months. To put that in viewpoint, in 2018, the full quantity of disclosed ICS bugs for the total calendar year was 672, and in 2019 the year’s rely was 716, Claroty documented.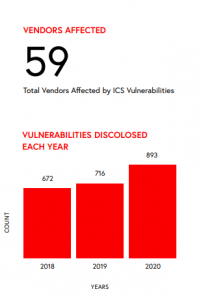
More and more, all those reports are from impartial researchers, the report explained. In simple fact, Claroty found that 50 new scientists released disclosures in the 2nd fifty percent of 2020, who hadn’t published in the two prior several years.
“There has been a shift in the direction of ICS study with strong advancement in security study teams for this next biannual report, as far more businesses attempt and recognize the new attack landscape,” Amir Preminger, vice president of analysis at Claroty, explained to Threatpost. “With this maximize in the volume of players coming into the current market and focusing on ICS security, there will naturally be an boost in vulnerabilities [that are found].”
Adversaries Switch Consideration Toward Industrial Bugs
Adversaries are also ratcheting up their stress on industrial networks. For occasion, Claroty observed the addition of industrial procedures into the Snake ransomware eliminate record.
“The ICS environment has come to be a additional attractive focus on for cybercriminals and this incentive is not just about what will lead to the most destruction, but also what products they can get their hands on,” Preminger explained. “Attacks will grow increasingly sophisticated and qualified, so it is important that organizations use distinct partitions of detection and practice security in depth.”
Legacy programs with prolonged shelf life are also weak spots.
“While ICS and SCADA vulnerability study is maturing, there are nonetheless a lot of decades-outdated security issues nonetheless uncovered,” the report explained. “For the time currently being, attackers may have an edge in exploiting them, since defenders are normally hamstrung by uptime requirements and an raising will need for detection abilities in opposition to exploitable flaws that could lead to procedure interruption or manipulation.”
ICS CISOs & SolarWinds PTSD
The report additional that headlines about the SolarWinds attack have built CISOs in each and every sector think twice about the sheer scope of their networks and who could want to attack them.
“Nation-condition actors are plainly looking at several features of the network perimeter to exploit, and cybercriminals are also focusing precisely on ICS processes, which emphasizes the need to have for security systems this sort of as network-centered detection and secure distant accessibility in industrial environments,” Preminger included.
The excellent news is that the industry is starting up to react.
“It is heartening to see a growing interest in ICS within just the security research local community, as we will have to glow a brighter gentle on these vulnerabilities in buy to hold threats at arm’s length,” Preminger claimed. “More vulnerabilities identified signifies the marketplace is extra protected, so it is reassuring to see the security group consider this seriously.
Download our exceptional Totally free Threatpost Insider Ebook Healthcare Security Woes Balloon in a Covid-Era Environment, sponsored by ZeroNorth, to master much more about what these security challenges suggest for hospitals at the day-to-day stage and how health care security teams can put into action greatest techniques to guard providers and patients. Get the total tale and Download the E-book now – on us!
Some parts of this article are sourced from:
threatpost.com


 Unpatched WordPress Plugin Code-Injection Bug Afflicts 50K Sites
Unpatched WordPress Plugin Code-Injection Bug Afflicts 50K Sites