Learn all the approaches MITRE ATT&CK can assist you defend your business. Establish your security method and guidelines by generating the most of this essential framework.
What is the MITRE ATT&CK Framework?
MITRE ATT&CK (Adversarial Tactics, Techniques, and Frequent Knowledge) is a commonly adopted framework and expertise base that outlines and categorizes the practices, methods, and treatments (TTPs) utilized in cyberattacks. Made by the nonprofit corporation MITRE, this framework presents security pros with insights and context that can assistance them comprehend, determine, and mitigate cyber threats correctly.
The tactics and practices in the framework are organized in a dynamic matrix. This would make navigation easy and also provides a holistic view of the total spectrum of adversary behaviors. As a final result, the framework is a lot more actionable and usable than if it ended up a static checklist.
The MITRE ATT&CK Framework can be found here: https://attack.mitre.org/
Look Out: MITRE ATT&CK Framework Biases
According to Etay Maor, Senior Director of Security Technique at Cato Networks, “The expertise furnished in the MITRE ATT&CK framework is derived from real-entire world evidence of attackers’ behaviors. This helps make it prone to specified biases that security specialists need to be mindful of. It truly is critical to recognize these restrictions.”
- Novelty Bias – Techniques or actors that are new or exciting are reported, even though procedures that are remaining made use of over and more than are not.
- Visibility Bias – Intel report publishers have visibility biases that are dependent on how they assemble details, ensuing in visibility for some techniques and not other folks. Also, methods are also seen in a different way all through incidents and afterward.
- Producer Bias – Reports published by some businesses could not replicate the broader sector or globe as a whole.
- Sufferer Bias – Some sufferer businesses are extra probably to report, or to be claimed on, than many others.
- Availability Bias – Report authors typically contain approaches that quickly arrive to thoughts in their experiences.
MITRE ATT&CK Defender Use Conditions
The MITRE ATT&CK framework will help security professionals investigate and examine numerous assaults and strategies. This can support with danger intelligence, detection and analytics, simulations, and evaluation and engineering. The MITRE ATT&CK Navigator is a instrument that can support check out and visualize the matrix, improving the assessment for defensive coverage, security scheduling, system frequency, and extra.
Etay Maor provides, “The framework can go as deep as you want it to be or it can be as significant degree as you want it to be. It can be made use of as a software to clearly show the mapping and if we are fantastic or poor at certain areas, but it could go as deep as knowing the pretty specific procedure and even the line of code that was made use of in a particular attack.”
Below are a few examples of how the framework and the Navigator can be utilised:
Threat Actor Evaluation
Security industry experts can leverage MITRE ATT&CK to investigate certain menace actors. For illustration, they can drill down into the matrix and discover which techniques are used by unique actors, how they are executed, which tools they use, etc. This details can help investigate certain attacks. It also expands the researchers’ understanding and way of contemplating by introducing them to extra modes of procedure attackers choose.
At a greater degree, the framework can be utilised to answer C-degree queries about breaches or risk actors. For case in point, if requested- “We imagine we may well be a goal for Iranian nation state danger actors.” The framework permits drilling down into Iranian threat actors like APT33, exhibiting which techniques they use, attack IDs, and much more.
Several Menace Actor Examination
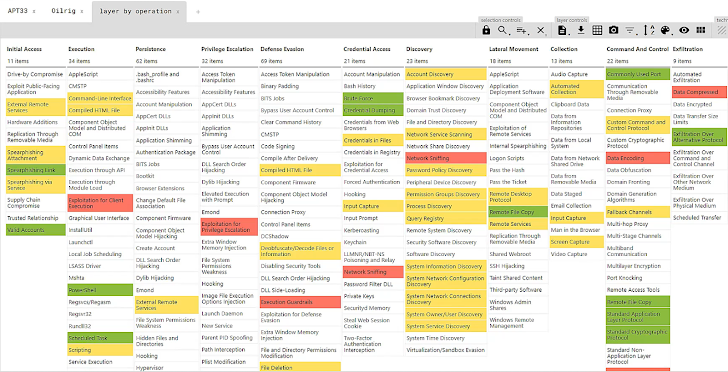
Apart from exploring certain actors, the MITRE ATT&CK framework also permits examining several menace actors. For instance, if a problem is elevated that “Owing to modern political and armed forces gatherings in Iran we imagine there will be a retaliation in the type of a cyber attack. What are the frequent attack tactics of Iranian menace actors?”, the framework can be utilized to identify frequent tactics utilised by a variety of nation-state actors.
This is what a visualized many risk actor assessment could seem like, with red and yellow symbolizing techniques utilised by various actors and eco-friendly representing an overlap.
Hole Investigation
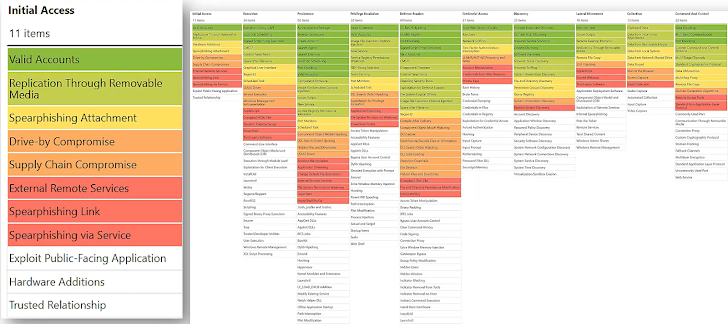
The MITRE ATT&CK framework also assists review existing gaps in defenses. This allows defenders to identify, visualize and type which kinds the organization does not have coverage for.
Here’s what it could seem like, with colors applied for prioritization.
Atomic Tests
Eventually, the Atomic Pink Workforce is an open up source library of tests mapped to the MITRE ATT&CK framework. These assessments can be employed for tests your infrastructure and programs primarily based on the framework, to aid determine and mitigate protection gaps.
The MITRE CTID (Middle for Danger-Informed Protection)
The MITRE CTID (Centre for Danger-Informed Protection) is an R&D centre, funded by private entities, that collaborates with the two private sector businesses and nonprofits. Their objective is to revolutionize the tactic to adversaries via source pooling and emphasizing proactive incident response fairly than reactive actions. This mission is driven by the belief, inspired by John Lambert, that defenders have to shift from contemplating in lists to wondering in graphs if they want to defeat attackers’ benefits.
Etay Maor remarks, “This is very crucial. We have to have to facilitate collaboration among the Defenders across different concentrations. We are very passionate about this.”
A major initiative within just this context is the “Attack Flow” task. Attack Move tackles the challenge confronted by defenders, who often concentration on particular person, atomic attacker behaviors. Alternatively, Attack Movement utilizes a new language and resources to describe the circulation of ATT&CK strategies. These procedures are then merged into designs of habits. This approach permits defenders and leaders to obtain a deeper knowledge of how adversaries operate, so they can refine their approaches accordingly.
You can see listed here what an Attack Movement looks like.
With these attack flows, defenders can respond to thoughts like:
- What have adversaries been accomplishing?
- How are adversaries switching?
The responses can enable them capture, share and review styles of attack.
Then, they will be able to respond to the most important issues:
- What is the next most probable factor they will do?
- What have we skipped?
CTID invitations the neighborhood to take part in its routines and add to its information foundation. You can speak to them on LinkedIn.
To discover additional about the MITRE ATT&CK framework, enjoy the whole masterclass in this article.
Observed this short article fascinating? Follow us on Twitter and LinkedIn to study far more unique written content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 SCARLETEEL Cryptojacking Campaign Exploiting AWS Fargate in Ongoing Campaign
SCARLETEEL Cryptojacking Campaign Exploiting AWS Fargate in Ongoing Campaign