A Microsoft Windows policy loophole has been noticed remaining exploited primarily by native Chinese-talking threat actors to forge signatures on kernel-mode drivers.
“Actors are leveraging multiple open-source applications that alter the signing day of kernel method motorists to load malicious and unverified drivers signed with expired certificates,” Cisco Talos said in an exhaustive two-part report shared with The Hacker News. “This is a major danger, as entry to the kernel gives complete accessibility to a system, and therefore overall compromise.”
Adhering to liable disclosure, Microsoft reported it has taken measures to block all certificates to mitigate the risk. It additional stated that its investigation discovered “the action was confined to the abuse of various developer plan accounts and that no Microsoft account compromise has been identified.”
The tech giant, other than suspending developer software accounts associated in the incident, emphasised that the danger actors had now obtained administrative privileges on compromised methods prior to use of the drivers.
It truly is well worth pointing out that the Windows maker experienced rolled out comparable blocking protections in December 2022 to stop ransomware attackers from making use of Microsoft-signed motorists for put up-exploitation activity.
Driver signature enforcement, which needs kernel-mode drivers to be digitally signed with a certificate from Microsoft’s Dev Portal, is a essential line of protection versus destructive drivers, which could be most likely weaponized to evade security answers, tamper with technique processes, and sustain persistence.
The new weakness learned by Cisco Talos would make it doable to forge signatures on kernel-manner motorists, therefore making it possible for Windows certificate insurance policies to be bypassed.
This is designed doable thanks to an exception carved out by Microsoft to manage compatibility, which permits cross-signed drivers if they were being “signed with an finish-entity certificate issued prior to July 29th 2015 that chains to a supported cross-signed [certificate authority].”
“The 3rd exception creates a loophole that permits a freshly compiled driver to be signed with non-revoked certificates issued prior to or expired prior to July 29, 2015, supplied that the certification chains to a supported cross-signed certification authority,” the cybersecurity organization mentioned.
As a final result, a driver signed in this method will not be prevented from being loaded on a Windows system, therefore enabling risk actors to choose benefit of the escape clause to deploy thousands of destructive, signed drivers with out publishing them to Microsoft for verification.
These rogue motorists are deployed employing signature timestamp forging computer software this kind of as HookSignTool and FuckCertVerifyTimeValidity, which have been publicly readily available considering that 2019 and 2018, respectively.
HookSignTool has been obtainable via GitHub due to the fact January 7, 2020, whilst FuckCertVerifyTimeValidity was very first fully commited to the code hosting services on December 14, 2018.
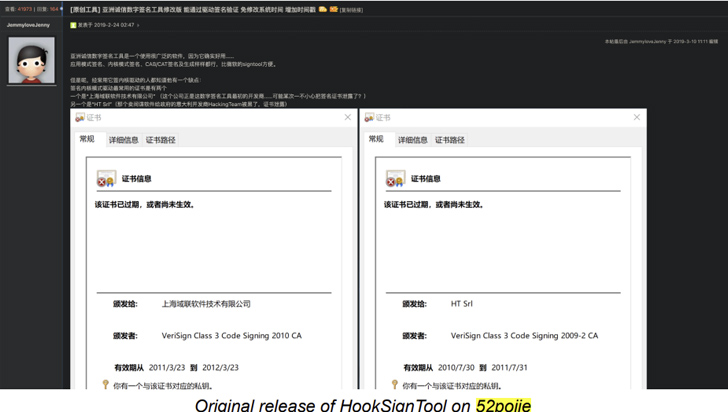
“HookSignTool is a driver signature forging device that alters the signing date of a driver during the signing method by means of a combination of hooking into the Windows API and manually altering the import table of a legitimate code signing software,” Cisco Talos spelled out.
Specifically, it requires hooking to the CertVerifyTimeValidity perform, which verifies the time validity of a certification, to transform the signing timestamp in the course of execution.
“This very small job helps prevent the signtool from verifing [sic] cert time validity and permit you indicator your bin with outdated cert without having altering technique time manually,” the GitHub site for FuckCertVerifyTimeValidity reads.
Impending WEBINAR🔐 PAM Security – Professional Methods to Secure Your Sensitive Accounts
This pro-led webinar will equip you with the knowledge and techniques you want to completely transform your privileged obtain security approach.
Reserve Your Location
“It set up hook into crypt32!CertVerifyTimeValidity and make it usually return and make kernel32!GetLocalTime return what you want as you can include “-fuckyear 2011″ to signtool’s command line to signal a cert from year 2011.”
That reported, pulling off a prosperous forgery needs a non-revoked code signing certificate that was issued before July 29, 2015, along with the certificate’s private critical and passphrase.
Cisco Talos reported it found out more than a dozen code signing certificates with keys and passwords contained in a PFX file hosted on GitHub in a forked repository of FuckCertVerifyTimeValidity. It can be not instantly very clear how these certificates had been acquired.
What’s far more, it has been noticed that HookSignTool has been made use of to re-signal cracked motorists in buy to bypass digital rights administration (DRM) integrity checks, with an actor named “Juno_Jr” releasing a cracked version of PrimoCache, a legit computer software caching option, in a Chinese application cracking forum on November 9, 2022.
“In the cracked model […], the patched driver was re-signed with a certification initially issued to ‘Shenzhen Luyoudashi Technology Co., Ltd.,’ which is contained in the PFX file on GitHub,” Talos researchers stated. “This potential to resign a cracked driver gets rid of a substantial roadblock when attempting to bypass DRM checks in a signed driver.”

Which is not all. HookSignTool is also currently being utilized by a previously undocumented driver determined as RedDriver to forge its signature timestamp. Energetic considering that at minimum 2021, it capabilities as a driver-dependent browser hijacker that leverages the Windows Filtering System (WFP) to intercept browser targeted traffic and reroute it to localhost (127…1).
The focus on browser is picked at random from a challenging-coded list made up of the approach names of quite a few well-known Chinese language browsers like Liebao, QQ Browser, Sogou, and UC Browser, as properly as Google Chrome, Microsoft Edge, and Mozilla Firefox.
“I in the beginning located RedDriver even though looking into certificate timestamp forging on Windows drivers,” Chris Neal, outreach researcher for Cisco Talos informed The Hacker News. “It was 1 of the very first samples I ran into that was immediately suspicious. What caught my awareness was the checklist of web browsers stored inside of the RedDriver file.”
The greatest goal of this browser traffic redirection is not crystal clear, while it goes without having declaring that such a capacity could be abused to tamper with browser site visitors at the packet degree.
RedDriver infection chains begin with the execution of a binary named “DnfClientShell32.exe,” which, in convert, initiates encrypted communications with a command-and-manage (C2) server to download the destructive driver.
“We failed to notice the shipping and delivery of the original file, but it truly is quite most likely that the file was packaged to masquerade as a video game file, and was hosted on a destructive obtain hyperlink,” Neal said. “The sufferer probably thought they have been downloading a file from a legit supply and ran the executable. ‘DNFClient’ is the name of a file belonging to ‘Dungeon Fighter Online’ which is an very popular match in China and generally referred to as ‘DNF.'”
“RedDriver was most likely made by very expert danger actors as the learning curve for producing malicious motorists is steep,” Cisco Talos mentioned. “While the danger seems to goal native Chinese speakers, the authors are probable Chinese speakers as effectively.”
“The authors also demonstrated a familiarity or knowledge with software growth lifecycles, another talent established that demands preceding advancement experience.”
Discovered this write-up fascinating? Observe us on Twitter and LinkedIn to browse additional special information we submit.
Some parts of this article are sourced from:
thehackernews.com


 How to Apply MITRE ATT&CK to Your Organization
How to Apply MITRE ATT&CK to Your Organization