The have to have for vCISO services is growing. SMBs and SMEs are dealing with a lot more 3rd-get together pitfalls, tightening regulatory demands and stringent cyber insurance policies requirements than at any time in advance of. Nevertheless, they often lack the sources and abilities to employ an in-house security executive staff. By outsourcing security and compliance leadership to a vCISO, these organizations can a lot more easily get hold of cybersecurity skills specialized for their marketplace and fortify their cybersecurity posture.
MSPs and MSSPs on the lookout to meet this expanding vCISO demand from customers are usually confronted with the similar obstacle. The demand for cybersecurity talent considerably exceeds the offer. This has led to a aggressive industry where the expenses of hiring and retaining competent gurus can be prohibitive for MSSPs/MSPs as very well. The will need to maintain skills of both security and compliance further exacerbates this challenge.
Cynomi, the to start with AI-driven vCISO platform, can aid.
Cynomi enables you – MSPs, MSSPs and consulting firms – to supply vCISO products and services at scale – with no straining your existing sources. Cynomi is modeled right after the knowledge of the world’s most effective CISOs, enabling you and your shoppers to attain accessibility to expert-level security and compliance insights and tools.
Cynomi gives the two principal vCISO pillars, security and compliance, in an automatic and actionable way. This contains security assessments, gap analysis, compliance readiness, coverage generation, task management and reporting. With Cynomi, you will gain from enhanced revenue, a escalating client foundation, reduction in risk assessment time, a reduce in report generation time, perfectly-structured processed and shorter personnel onboarding times.
Let us see how quick Cynomi is to do the job on:
Setting Up and Taking care of Multi-Tenant Accounts
Focusing on associates, Cynomi was built to support multi-tenancy. You can independently generate and take care of a independent sub-account for each of your purchasers, allowing you to easily take care of and track just about every just one, as very well as giving them accessibility to Cynomi.
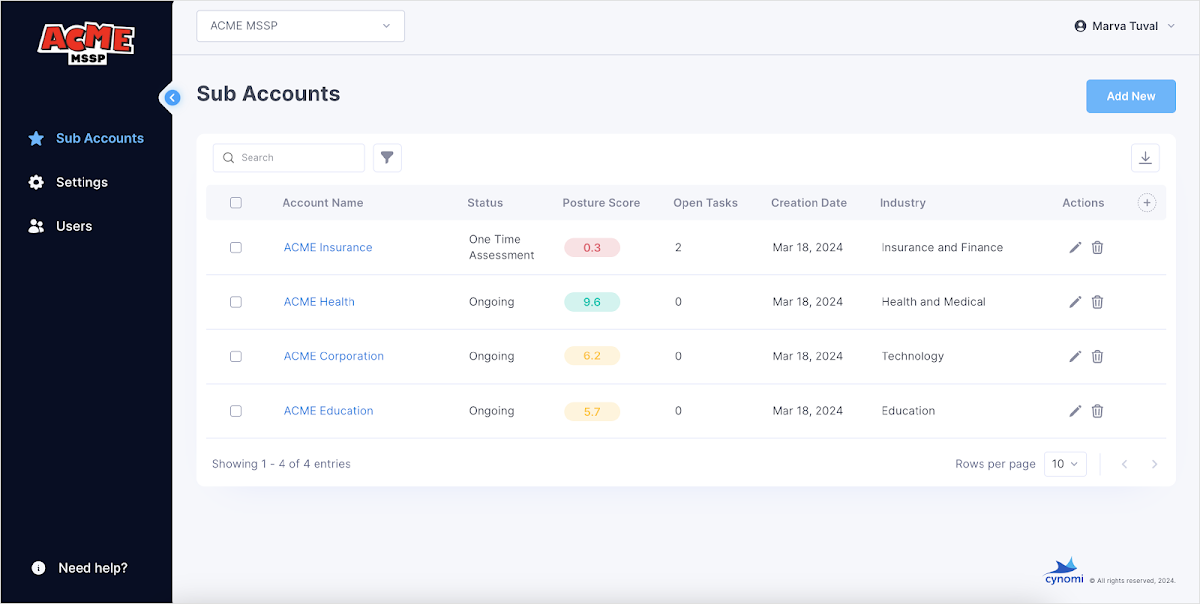 Determine 1: Cynomi account administration display screen
Determine 1: Cynomi account administration display screen
To assist your scalability and growth, you can delegate roles and ownership among your workforce for each individual shopper account. You will nevertheless take pleasure in admin-level cross-account visibility and privileges.
For centralized administration of all your shoppers, Cynomi offers a unified account management monitor in which you can edit user specifics, resend invites, unlock blocked accounts and much more.
Where ever you are on the platform, you might be generally just a click away from the admin panel and all your user accounts.
Developing a Cyber Profile with an Onboarding Questionnaire
Onboarding a new customer starts with accumulating significant-stage data about them, allowing for to develop a pertinent remediation plan. This features an onboarding questionnaire about their infrastructure. The moment completed, Cynomi generates a tailor-made established of brief abide by-up questionnaires for security posture evaluation.
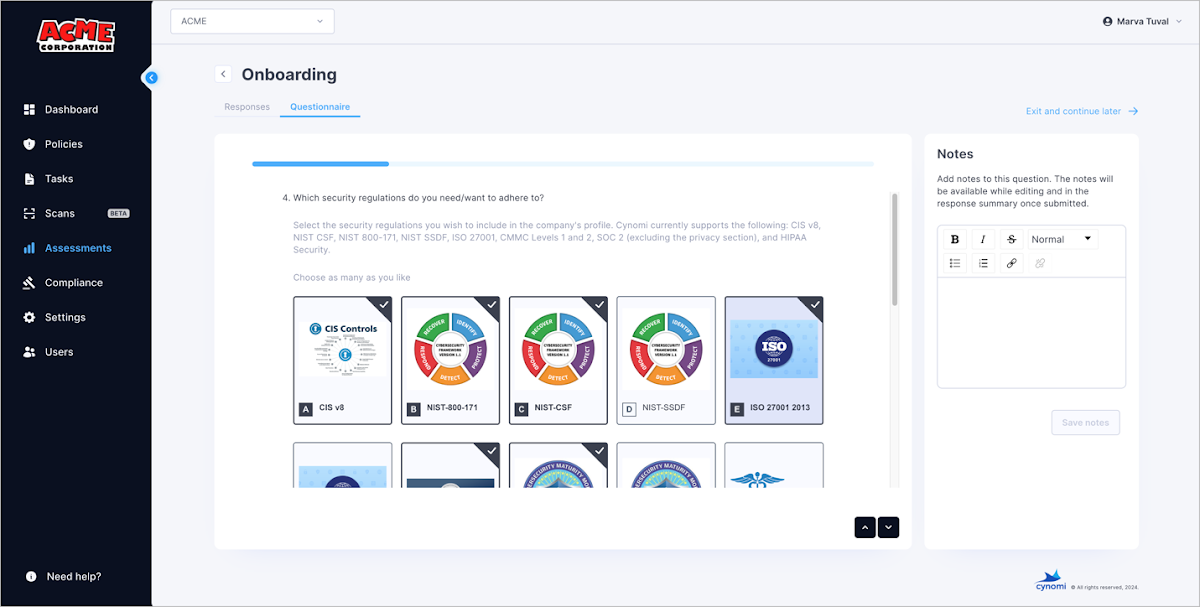 Figure 2: Cynomi onboarding questionnaire
Figure 2: Cynomi onboarding questionnaire
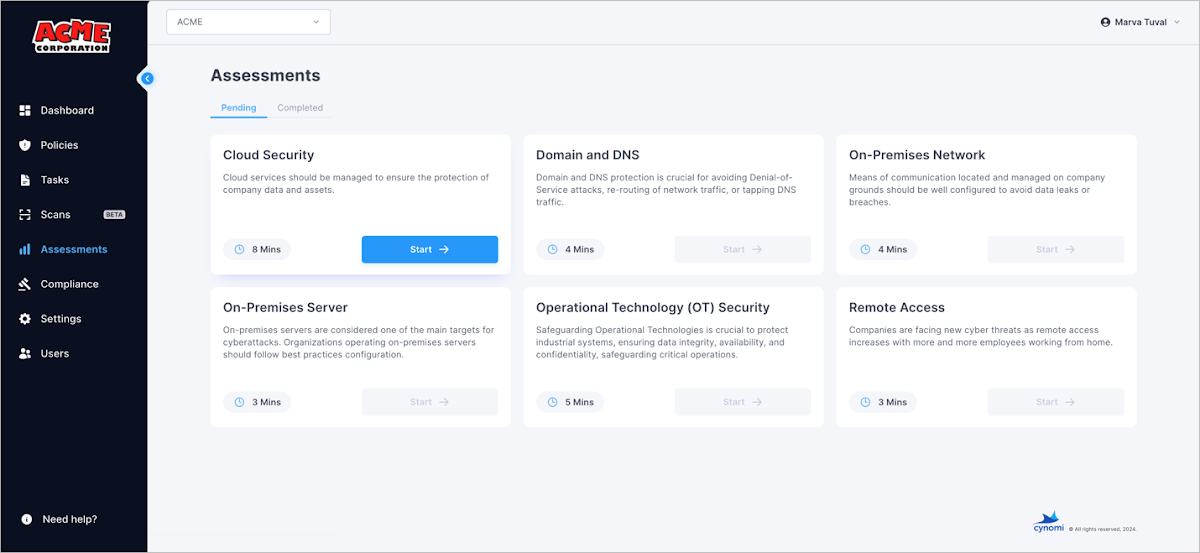 Determine 3: Cynomi personalized-designed observe-up questionnaires
Determine 3: Cynomi personalized-designed observe-up questionnaires
Finishing all the questionnaires provides a detailed look at of shopper security posture and gaps. Based on the responses, Cynomi presents custom made tailored insurance policies that cover all actions expected for remediating security gaps.
Questionnaires can be revised at any time if a client’s setting changes. Procedures will be mechanically up-to-date accordingly.
Inside and Exterior Scans
To augment and full your knowledge of your client’s cyber profiles, Cynomi makes it possible for you to scan and assess their external and inside property.
External Scanning:
For examining the security of externally uncovered property, Cynomi scans IPs and URLs and discovers vulnerabilities as nicely as secured configurations. This involves scanning risky ports, examining protocols and encryption, verifying email configuration parameters, technology updates of web purposes and extra.
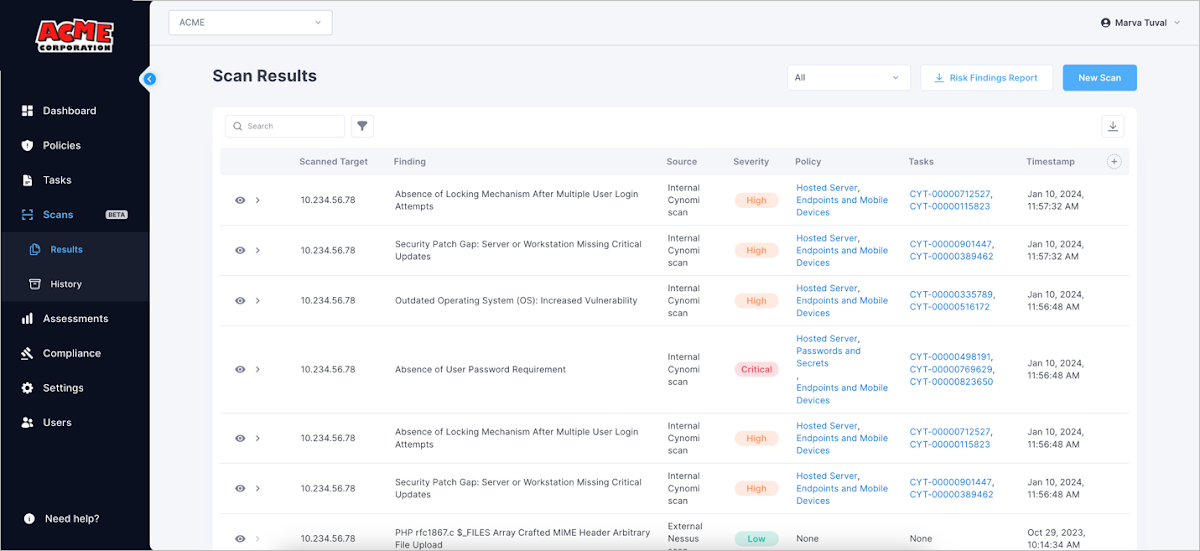 Figure 4: Cynomi scan benefits display
Figure 4: Cynomi scan benefits display
People can drill down into each and every scan discovering to see an in-depth description and remediation possibilities. Any detected vulnerabilities are mechanically extra to the account’s task checklist, according to their severity.
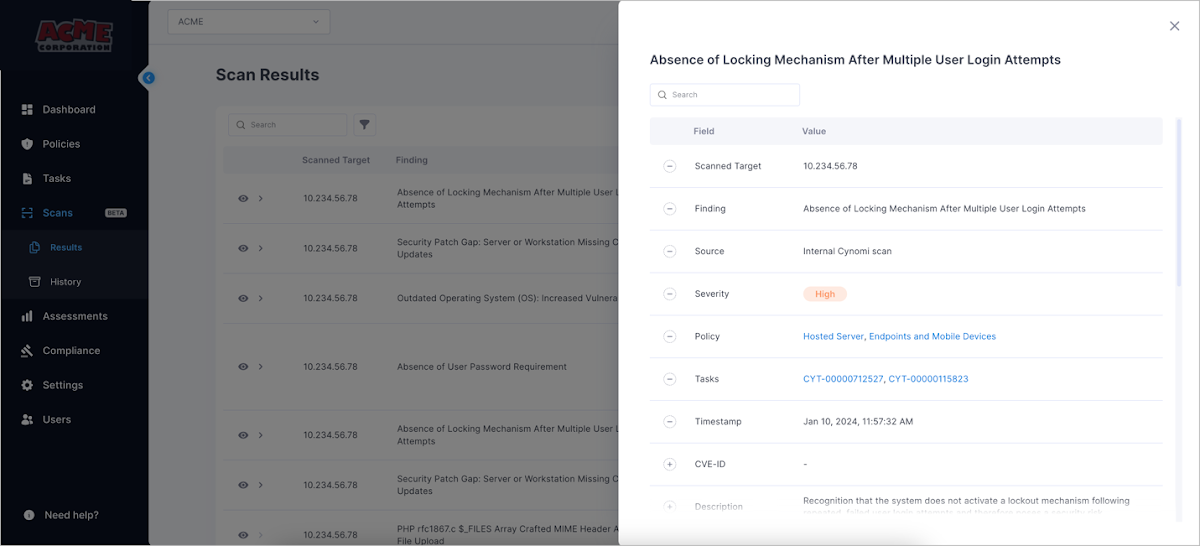 Figure 5: Drill-down to a specific finding
Figure 5: Drill-down to a specific finding
Scan success are accessible in just a number of minutes.
Interior Scanning:
For discovering vulnerabilities in the client’s interior networks. Scans include customer belongings like energetic listing and endpoints and evaluate its security hygiene and configuration.
You can also upload your NESSUS exterior scan, Qualys external scan or Microsoft Secure Score CSV data files.
Scan conclusions are aggregated in an aggregated table and linked to the applicable responsibilities and guidelines they are linked to.
Security Evaluation
Cynomi constantly parses every single client’s cyber profile versus business-unique security benchmarks, regulatory frameworks and marketplace-specific threat intelligence. These are coupled with the information and facts from the security questionnaires and the scans.
Based on the company-distinct profile, the appropriate cyber domains are dynamically picked with the optimized prerequisites. Every single prerequisite is assigned a criticality degree, symbolizing the great importance of this prerequisite for the organization’s security posture. Challenges these kinds of as ransomware and details leak are calculated as very well, primarily based on the organization’s sensitivity to all those attacks.
The result is a solitary pane of glass see of just about every client’s total security posture and its progress about time.
The dashboard contains:
- Total security posture score
- Vulnerability and exploit gap assessment
- Risk score for a distinct risk vector
- Remediation plan with actionable prioritized tasks
- Position versus various compliance frameworks necessities
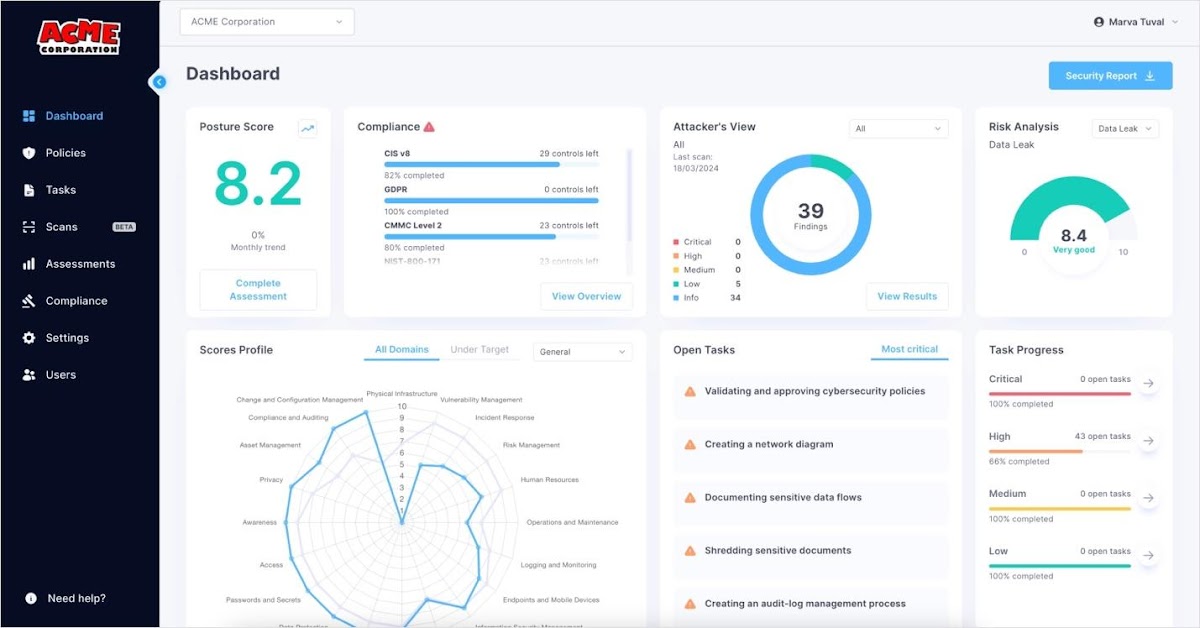 Determine 6: Cynomi most important dashboard
Determine 6: Cynomi most important dashboard
In depth, Steady Compliance Assessment
For conference compliance requirements, Cynomi presents the customer position towards different compliance and security frameworks (listing repeatedly up to date):
- CIS v8
- ISO 27001
- NIST CSF 1.1
- NIST CSF2.
- NIST-171
- NIST-SSDF
- SOC 2
- CMMC L1, CMMC L2
- GDPR
- NIS2
- PCI-DSS
- HIPAA security
- Cyber Necessities
- FTC Safeguard Rule
- SEC compliance
- ICS Cyber Security
- CCPA
- FFIEC
The compliance module is actionable and makes it possible for seeing the information of every control in each individual framework and how each individual process maps into every framework.
The compliance position versus frameworks is up to date constantly so you are usually informed of your client’s readiness degree.
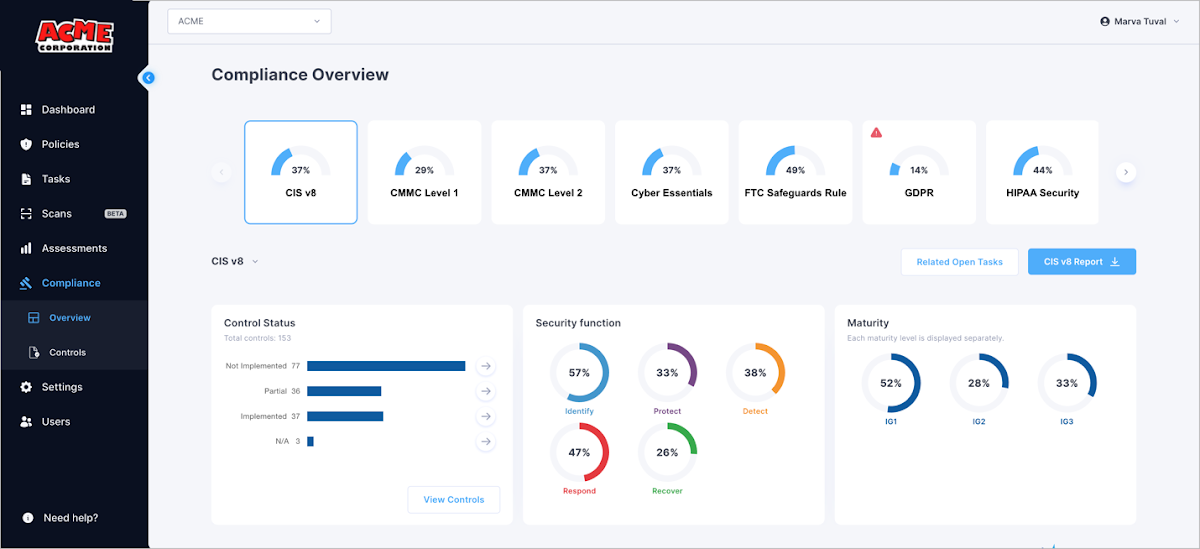 Figure 7: Cynomi compliance dashboard
Figure 7: Cynomi compliance dashboard
You can also download a dedicated compliance status report for each consumer. The report involves:
- All round compliance position
- A record of controls
- Maturity degree
- Handle position
- Command mapping to framework
- Implementation status
- A hyperlink to the appropriate Cynomi jobs
With this facts, you can effortlessly have an understanding of where by your purchasers stand and what gaps need to be shut in buy to comply with unique frameworks. You can then create a remediation plan for each individual framework you selected with just a several clicks.
Tailor-created Security Insurance policies
It’s time to get down to organization. Cynomi routinely generates a set of policies for each consumer. They are customized-developed leveraging many years of designed-in CISO skills and crafted to be effortless to observe and actionable.
On the guidelines perspective, you’ll come across:
- The corporation rating for all generated guidelines
- The choice to drill down into the information of every single coverage, which includes intent, scope and protection needs
- Information and facts on the jobs and progress that require to be concluded for securing the policy’s area
For illustration, this coverage display shows the client’s rating for each policy and lets you to drill down to see a breakdown of the guidelines prerequisites.
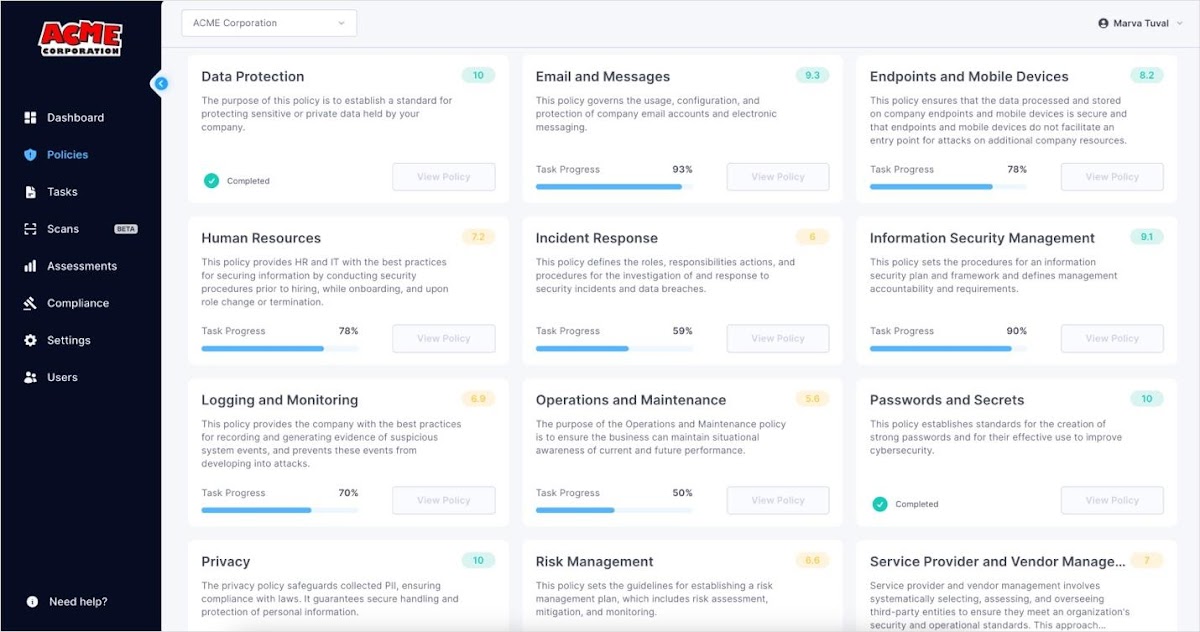 Determine 8: Cynomi guidelines display
Determine 8: Cynomi guidelines display
Policies are editable and customizable.
Actionable, Prioritized Remediation Tasks
Modeled just after the expertise of the world’s most effective CISOs, every coverage requirement is also translated into an actionable task for remediation. Duties are quick and intuitive to understand and observe and are shown in an AI-produced prioritized list that incorporates its severity and position.
Process kinds incorporate:
- Specialized controls
- Administrative procedures
- Security parts configurations
- And far more
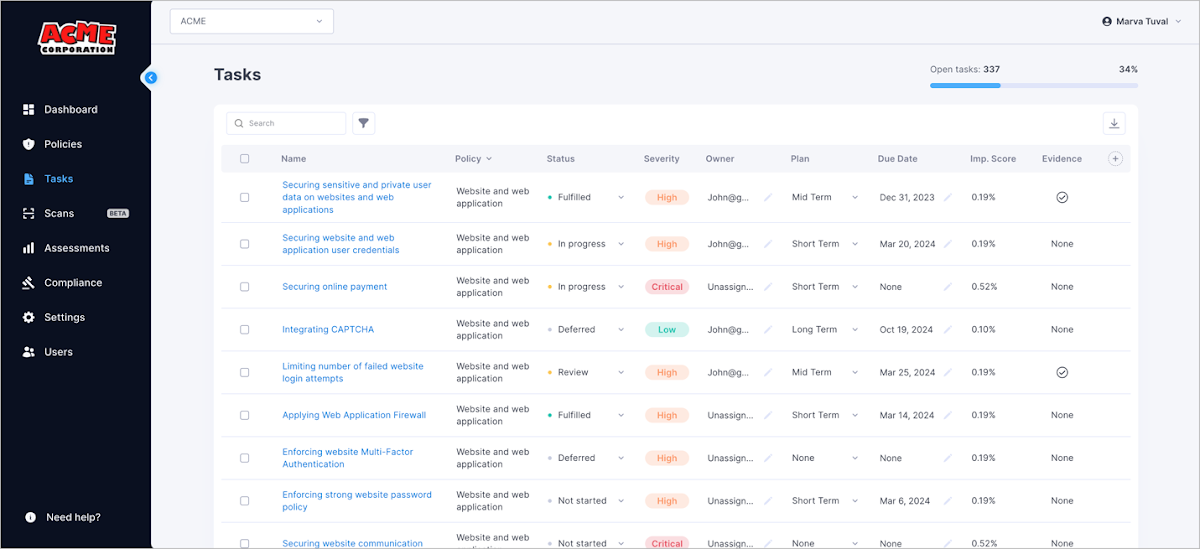 Determine 9: Cynomi tasks monitor
Determine 9: Cynomi tasks monitor
The list and responsibilities can be edited. This flexibility enables the running vCISO to postpone or defer specific tasks with out impacting coverage position or severity.
To keep track of and deal with duties, people can utilize filters, jump back to responsibilities that are already in development, or emphasis on high severity responsibilities only. All progress is tracked, and duties done are quickly reflected in the client’s overall security posture score.
To execute and comprehend responsibilities, every endeavor can be drilled into for step-by-step steering on putting a handle in spot or mitigating the risk. Tasks are also customizable, letting you to increase very best exercise steerage, as nicely as evidence that supports the job.
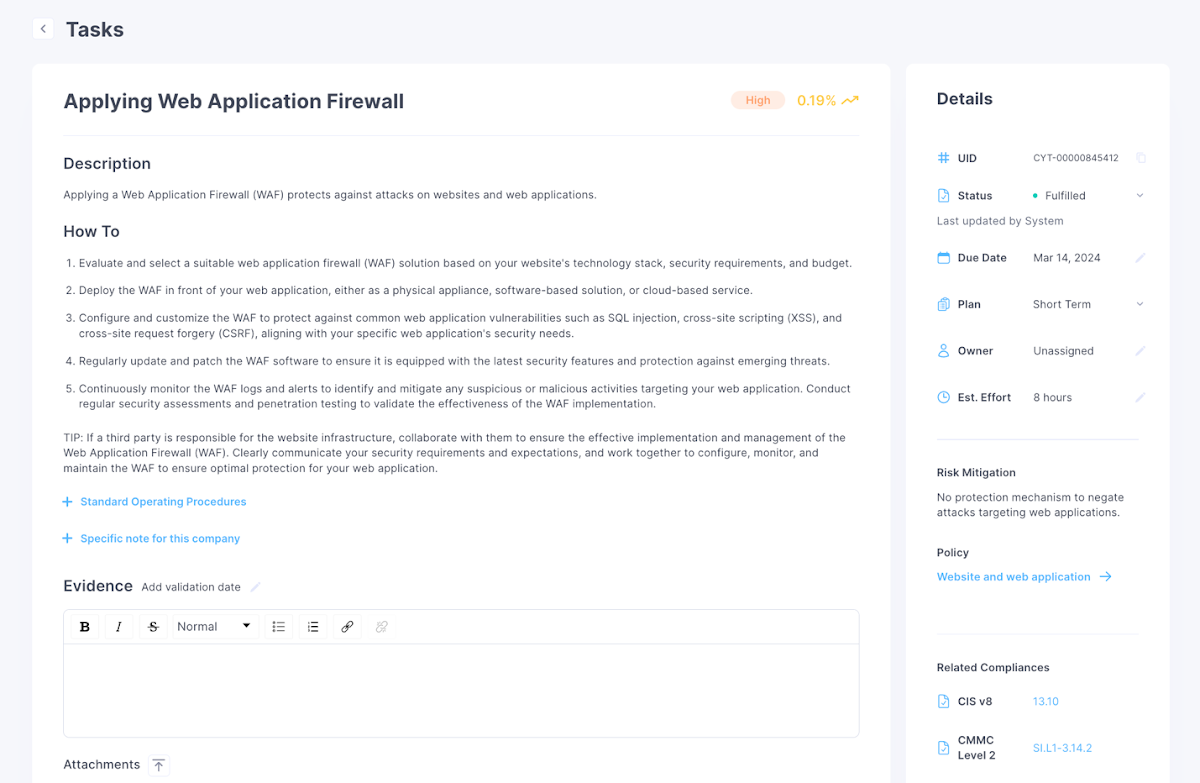 Determine 10: Drill-down to a distinct endeavor
Determine 10: Drill-down to a distinct endeavor
Plan and Roadmap
Cynomi leverages AI and automations to build a prompt plan. Then, the Cynomi system offers the consumer with a wealth of equipment and capabilities for scheduling, ongoing undertaking administration optimization and development monitoring:
- Assigning jobs to quick-, medium- and extensive-phrase plans
- Allocating responsibilities to plans
- Introducing owing dates
- Filtering according to framework, because of date, position, and a lot more
- Modifying responsibilities for every switching requirements
- Introducing information and facts and proof to every activity, for every account or throughout the board, with specification, details and suggestions
- Introducing item and provider suggestions to duties for upselling new providers
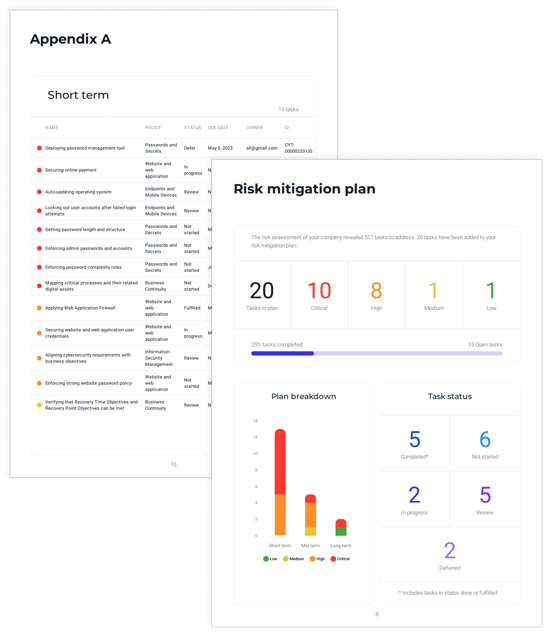 Figure 11: Cynomi automated risk mitigation plan
Figure 11: Cynomi automated risk mitigation plan
Buyer-facing Reports
Cynomi features designed-in purchaser-dealing with reporting for every single consumer. You can crank out reviews at the click on of a button with your have branding displaying the client’s security degree, improvement, traits, compliance gaps and comparisons with market benchmarks. Experiences involve:
- Full Report – Your client’s cybersecurity posture. Use the report to existing your clients’ position to them and your proposed remediation plan. Over time, updating the report will demonstrate the security enhancements you served them make.
- Risk Results Report – Your clients’ risk publicity primarily based on the system scans.
- Compliance Report – Your clients’ compliance readiness and standing.
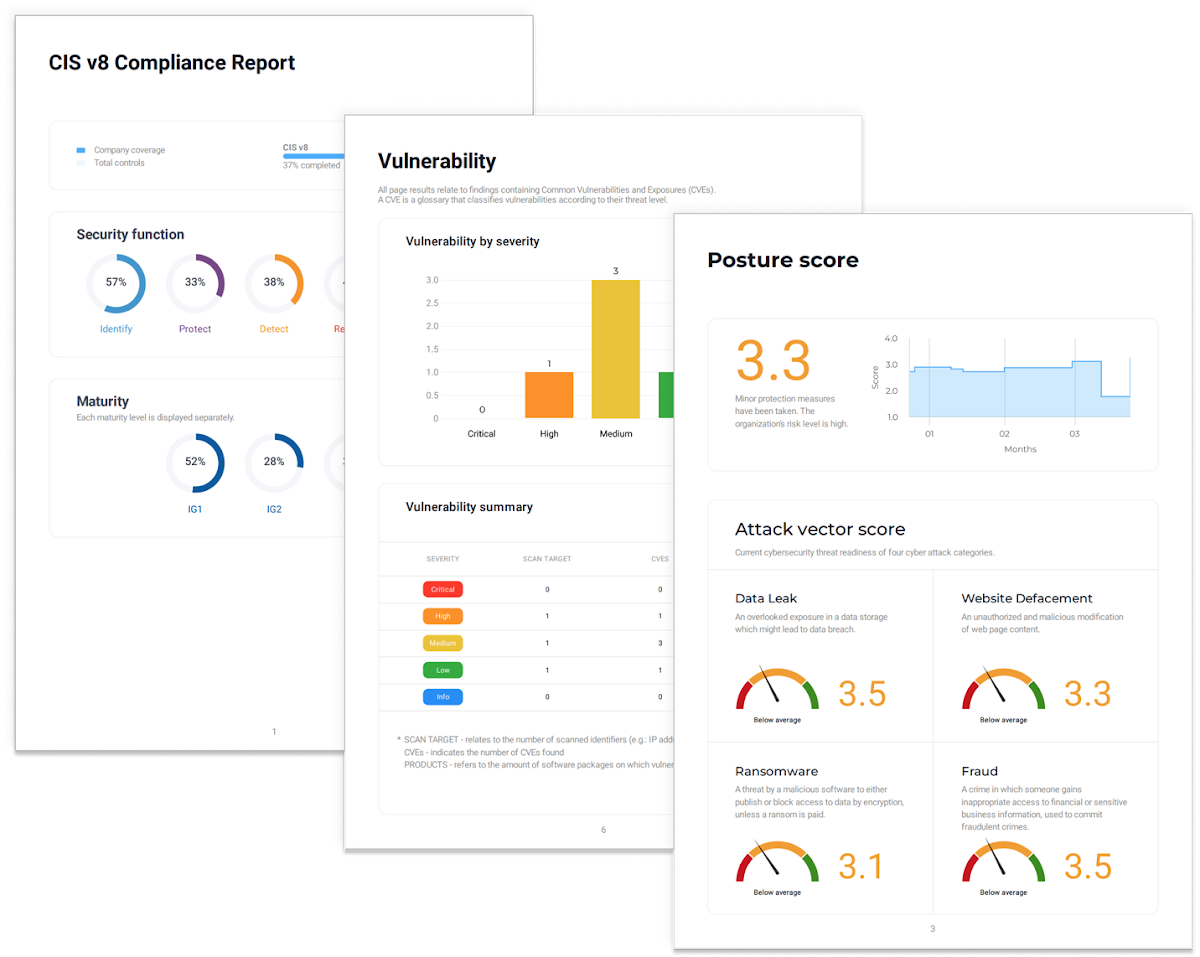 Determine 12: Cynomi stories
Determine 12: Cynomi stories
These studies can assist you to very easily clearly show your purchasers their present cyber posture standing, the development you aided them make and the impression of your do the job. Use these studies to open up conversations with administration, IT and other stakeholders. Present them the security challenges, enable them have an understanding of prerequisites and show development as each and every activity is finished.
Steady Optimization
Not like a person-time assessment resources, Cynomi continually updates your client’s risk score, compliance readiness policies and duties and demonstrates development in excess of time. These are based on modifications in your shopper ecosystem, regulatory necessities and business-certain risk intelligence. With this information and facts, you can relaxation assured that you will usually remain on best of your clients’ compliance and cybersecurity posture and reveal the benefit of your strategic cybersecurity company to them.
The Bottom Line
Cynomi’s AI-run vCISO system is intended to assist MSPs and MSSPs develop their small business and earnings by vCISO providers. Cynomi allows company companies provide comprehensive vCISO products and services to SMBs and SMEs, from risk assessments to security policies to plans and reporting, throughout each vCISO pillars: security and compliance. By knowledge the influence of just about every endeavor and motion on each security and compliance, MSPs/MSSPs can make the most qualified selections for their clientele. This allows MSPs and MSSPs to develop their consumer foundation and safe recurring earnings with current customers.
Cynomi also decreases vCISO tasks’ time by over 40% and aids onboard new employees rapidly, so tasks can be delegated to them, regardless of seniority. By simplifying and standardizing processes, MSPs/MSSPs can onboard staff and clients rapidly and reduce time-to-value by fifty percent.
Finally, Cynomi’s stories allow MSPs and MSSPs to leverage experiences and demonstrate tangible affect. This opens up conversations with management and boosts upsell of solutions and products.
Check out Cynomi web site to check it on your own.
Identified this article intriguing? This post is a contributed piece from one particular of our valued companions. Abide by us on Twitter and LinkedIn to read through far more exclusive material we article.
Some parts of this article are sourced from:
thehackernews.com


 Researchers Uncover First Native Spectre v2 Exploit Against Linux Kernel
Researchers Uncover First Native Spectre v2 Exploit Against Linux Kernel