Aspects of a new country-state sponsored phishing campaign has been uncovered environment its sights on European governmental entities in what is actually observed as an endeavor to get hold of intelligence on refugee and offer movement in the location.
Business security firm Proofpoint, which detected the malicious emails for the initially time on February 24, 2022, dubbed the social engineering attacks “Asylum Ambuscade.”
“The email incorporated a malicious macro attachment which used social engineering themes pertaining to the Unexpected emergency Meeting of the NATO Security Council held on February 23, 2022,” scientists Michael Raggi and Zydeca Cass explained in a report released Tuesday.
“The email also contained a destructive attachment which attempted to down load destructive Lua malware named SunSeed and qualified European government staff tasked with handling transportation and population movement in Europe.”

The findings create on an advisory issued by the Point out Provider of Special Communication and Info Safety of Ukraine (DSSZZI), which warned last 7 days of phishing messages concentrating on its navy personnel with ZIP file attachments with the goal of thieving delicate own info.
Proofpoint declined to attribute the freshly noticed marketing campaign to a distinct danger actor, but mentioned that the overlaps in the timeline of the two sets of attacks, the phishing lures employed, and the victimology designs aligns with that of a Belarusian nation-point out team named UNC1151 (aka TA445 or Ghostwriter).
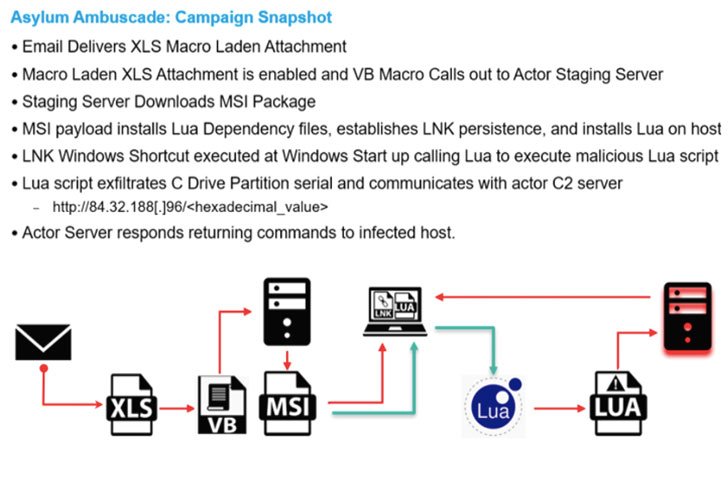
A single of the noteworthy factors of Asylum Ambuscade is the most likely use of a compromised Ukrainian armed provider member’s email account to broadcast malware-laced email messages that contains a macro-enabled XLS file that provides SunSeed onto contaminated hosts, implying that the most current campaign may perhaps be a continuation of these assaults.
“The social engineering lures used in this phishing campaign had been incredibly well timed, pursuing a NATO Security Council assembly on February 23, 2022 and a news story about a Russian federal government ‘kill list’ concentrating on Ukrainians that started circulating in Western media outlets on February 21, 2022,” the scientists pointed out.
SunSeed, for its component, features as a downloader that establishes communications with an actor-controlled server to retrieve up coming-stage payloads for execution.
The Sunnyvale-centered cybersecurity firm observed that the assaults particularly singled out folks who have been tasked with duties associated to transportation, fiscal and spending budget allocation, administration, and populace movement inside Europe.

The disclosure arrives as Russia’s intensifying military services invasion of Ukraine has polarized cyberspace, with hacktivists, cybercriminals, white hat researchers, and technology corporations picking a facet in the conflict.
In a different update posted before right now, Ukraine’s Laptop Crisis Reaction Workforce (CERT-UA) explained the ongoing developments as an “data and psychological war,” urging men and women in the country to carefully watch their accounts for unrecognized products, transform on two-aspect authentication, and use conclude-to-stop encrypted messaging applications.
What’s more, email security business Avanan explained it witnessed an eightfold boost in email-borne assaults originating from Russia starting on February 27, at the very least some of them focusing on manufacturing, global transport, and transportation providers positioned in the U.S. and Europe.
“In light-weight of the ongoing Russia-Ukraine war, steps by proxy actors like TA445 will proceed to goal European governments to obtain intelligence all around the movement of refugees from Ukraine and on issues of worth to the Russian authorities,” the researchers said.
Discovered this post interesting? Stick to THN on Facebook, Twitter and LinkedIn to study far more exceptional articles we post.
Some parts of this article are sourced from:
thehackernews.com


 Hyundai plans to introduce 17 electric vehicles by 2030
Hyundai plans to introduce 17 electric vehicles by 2030