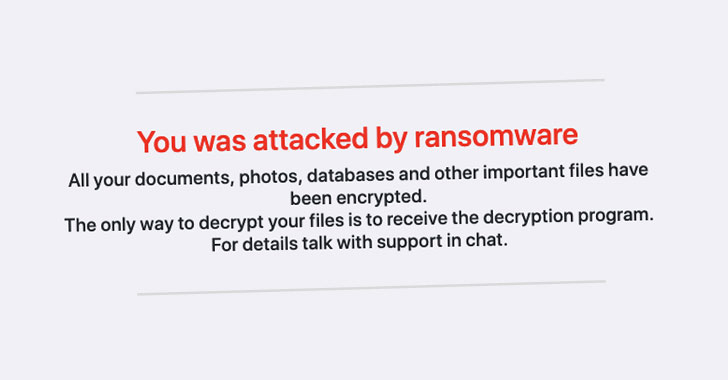
An “aggressive” monetarily motivated risk team tapped into a zero-day flaw in SonicWall VPN appliances prior to it remaining patched by the enterprise to deploy a new strain of ransomware known as FIVEHANDS.
The team, tracked by cybersecurity organization Mandiant as UNC2447, took edge of an “poor SQL command neutralization” flaw in the SSL-VPN SMA100 products (CVE-2021-20016, CVSS score 9.8) that will allow an unauthenticated attacker to attain distant code execution.
“UNC2447 monetizes intrusions by extorting their victims initial with FIVEHANDS ransomware followed by aggressively making use of pressure through threats of media attention and presenting target knowledge for sale on hacker community forums,” Mandiant researchers mentioned. “UNC2447 has been noticed targeting businesses in Europe and North The united states and has persistently exhibited state-of-the-art abilities to evade detection and lessen submit-intrusion forensics.”

CVE-2021-20016 is the very same zero-working day that the San Jose-primarily based organization claimed was exploited by “refined threat actors” to stage a “coordinated attack on its interior devices” before this 12 months. On January 22, The Hacker News exclusively discovered that SonicWall had been breached by exploiting “possible zero-day vulnerabilities” in its SMA 100 sequence remote accessibility products.
Thriving exploitation of the flaw would grant an attacker the skill to entry login credentials as properly as session info that could then be made use of to log into a susceptible unpatched SMA 100 sequence appliance.
In accordance to the FireEye-owned subsidiary, the intrusions are stated to have transpired in January and February 2021, with the threat actor utilizing malware named SombRAT to deploy the FIVEHANDS ransomware. It truly is well worth noting that SombRAT was identified in November 2020 by BlackBerry scientists in conjunction with a campaign identified as CostaRicto carried out by a mercenary hacker group.

UNC2447 assaults involving ransomware infections have been to start with observed in the wild in October 2020, at first compromising targets with HelloKitty ransomware, before swapping it for FIVEHANDS in January 2021. By the way, equally the ransomware strains, published in C++, are rewrites of an additional ransomware called DeathRansom.
“Based on complex and temporal observations of HelloKitty and FIVEHANDS deployments, HelloKitty may well have been utilized by an general affiliate software from Could 2020 through December 2020, and FIVEHANDS due to the fact approximately January 2021,” the researchers stated.
FIVEHANDS also differs from DeathRansom and HelloKitty in the use of a memory-only dropper and extra characteristics that allow for it to acknowledge command-line arguments and utilize Windows Restart Manager to close a file at present in use prior to encryption.
The disclosure arrives fewer than two weeks following FireEye divulged a few previously unfamiliar vulnerabilities in SonicWall’s email security software that have been actively exploited to deploy a web shell for backdoor entry to the victim. FireEye is tracking this malicious exercise under the moniker UNC2682.
Found this short article appealing? Observe THN on Facebook, Twitter and LinkedIn to go through a lot more exceptional content material we publish.
Some parts of this article are sourced from:
thehackernews.com

 The EU's Apple antitrust investigation is moving forward
The EU's Apple antitrust investigation is moving forward