A politically motivated hacker team tied to a series of espionage and sabotage assaults on Israeli entities in 2021 incorporated a earlier undocumented remote obtain trojan (RAT) that masquerades the Windows Calculator app as aspect of an effort and hard work to continue to be under the radar consciously.
Cybersecurity company Cybereason, which has been tracking the functions of the Iranian actor regarded as Moses Staff, dubbed the malware “StrifeWater.”
“The StrifeWater RAT seems to be utilized in the original stage of the attack and this stealthy RAT has the skill to get rid of alone from the procedure to go over the Iranian group’s tracks,” Tom Fakterman, Cybereason security analyst, explained in a report. “The RAT possesses other abilities, this sort of as command execution and monitor capturing, as well as the capability to obtain supplemental extensions.”

Moses Personnel arrived to light-weight toward the conclusion of very last yr when Test Position Investigation unmasked a collection of assaults aimed at Israeli corporations due to the fact September 2021 with the objective of disrupting the target’s company operations by encrypting their networks, with no possibility to regain obtain or negotiate a ransom.
The intrusions ended up noteworthy for the actuality that they relied on the open-resource library DiskCryptor to carry out volume encryption, in addition to infecting the systems with a bootloader that stops them from starting off devoid of the suitable encryption crucial.
To date, victims have been documented past Israel, which include Italy, India, Germany, Chile, Turkey, the U.A.E., and the U.S.
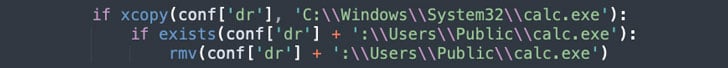
The new piece of the attack puzzle identified by Cybereason arrives in the form of a RAT that is deployed below the identify “calc.exe” (the Windows Calculator binary) and is used during the early phases of the an infection chain, only to be eliminated prior to the deployment of the file-encrypting malware.
The removal and the subsequent alternative of the destructive calculator executable with the legitimate binary, the researchers suspect, is an try on the portion of the danger actor to go over up tracks and erase evidence of the trojan, not to mention permit them to evade detection until the final phase of the attack when the ransomware payload is executed.
StrifeWater, for its component, is no various from its counterparts and arrives with several attributes, chief amid them becoming the skill to record program data files, execute process commands, take screen captures, generate persistence, and down load updates and auxiliary modules.
“The conclude purpose for Moses Personnel appears to be additional politically enthusiastic fairly than monetary,” Fakterman concluded. “Moses Staff employs ransomware post-exfiltration not for economic acquire, but to disrupt operations, obfuscate espionage exercise, and to inflict harm to devices to advance Iran’s geopolitical goals.”
Discovered this post interesting? Comply with THN on Fb, Twitter and LinkedIn to read through far more exceptional information we submit.
Some parts of this article are sourced from:
thehackernews.com


 Critical Bug Found in WordPress Plugin for Elementor with Over a Million Installations
Critical Bug Found in WordPress Plugin for Elementor with Over a Million Installations