Cruddy cryptography indicates victims whose data files have been encrypted by the Ukraine-tormenting ransomware can break the chains without the need of paying out extortionists.
A no cost decryptor is out to unlock a ransomware found piggybacking on the HermeticWiper information wiper malware that ESET and Broadcom’s Symantec identified focusing on equipment at fiscal, protection, aviation and IT companies outfits in Ukraine, Lithuania and Latvia previous 7 days.
The point that there was ransomware clinging to the details-wiping malware didn’t surprise cybersecurity authorities, of training course. It was predicted by Katie Nickels, director of intel at Red Canary, for 1: She tweeted that there was pretty most likely a “broader intrusion chain.”
As you happen to be studying this, notice this place: adversaries likely experienced handle of the Advert server presently. They had been by now in. There is a broader intrusion chain past just the wiper, it just just isn’t publicly regarded still. I am seeing for any facts on what occurs Prior to wiper deployment. https://t.co/59SZTpTlXA
— Katie Nickels (@likethecoins) February 23, 2022
What may well have been a bit much more stunning was the welcome discovery, designed by CrowdStrike’s Intelligence Crew earlier this week, that HermeticRansom experienced a lame encryption system that permit the ransomware’s tentacles be untangled.
Avast Risk Labs experienced noticed the new ransomware pressure past Thursday, Feb. 24. Avast, which named the new strain HermeticRansom, on Thursday released a absolutely free decryptor that included a decryption script CrowdStrike produced to GitHub, a user-pleasant GUI and a set of directions on its use.
The decryptor can be downloaded in this article.
Crypto Possible Weakened by Coding Errors
HermeticRansom, aka PartyTicket, was discovered at many victimized companies, among the other malware family members that bundled what CrowdStrike named the “sophisticated” HermeticWiper, aka DriveSlayer.
No matter of how advanced the wiper malware was, the ransomware that hopped a trip on it experienced much less-than-stellar encryption, with a logic flaw in the encryption procedure that enabled researchers to crack via, CrowdStrike said: “Analysis of the [PartyTicket/HermeticRansom] ransomware implies it superficially encrypts information and does not effectively initialize the encryption critical, producing the encrypted file with the affiliated .encryptedJB extension recoverable.”
At the time it posted its report, CrowdStrike hadn’t traced the ransomware to a identified danger actor. It didn’t rather feel like a critical try at ransomware, at any amount, scientists explained, specified the coding problems that built its encryption “breakable and slow.”
Possibly the malware author was unfamiliar with crafting in Go or rushed its improvement without the need of extensively screening it, analysts surmised.
Either way, it seemed to analysts as if extortion wasn’t the principal goal: “The relative immaturity and political messaging of the ransomware, the deployment timing and the focusing on of Ukrainian entities are dependable with its use as an additional payload alongside DriveSlayer action, alternatively than as a authentic ransomware extortion endeavor,” they wrote.
Down below is a display capture of HermeticRansom’s extortion observe:
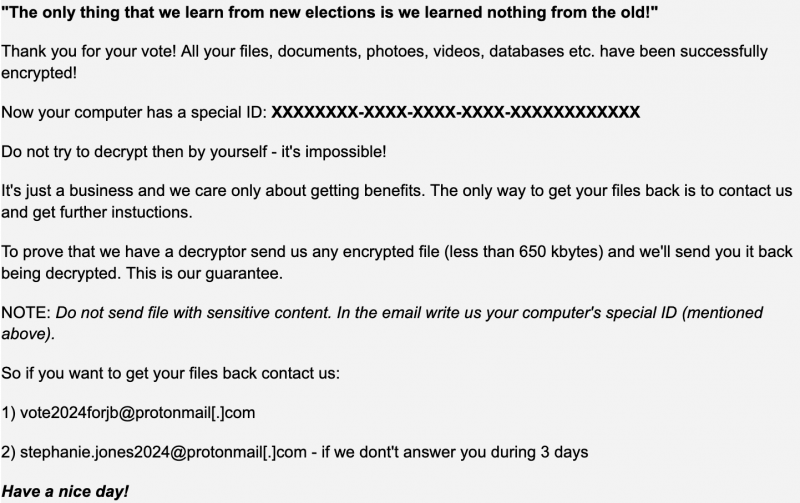
HermeticRansom ransomware demand note. Resource: CrowdStrike Intelligence Workforce.
HermeticWiper History
HermeticWiper, uncovered past week, has been utilised towards hundreds of devices in Ukraine – assaults that adopted dispersed denial-of-company (DDoS) attacks launched from Ukraine websites on Feb. 23.
One particular of the HermeticWiper malware samples was compiled back on Dec. 28, pointing to the wiper assaults acquiring been readied two months right before Russia’s army assault.
HermeticWiper was only 1 of an onslaught of cyberattacks and malware that have been unleashed prior to and in the course of the crisis, including the novel FoxBlade trojan, a wave of pre-invasion DDoS attacks in mid-February, furthermore another campaign of wiper attacks concentrating on Ukraine and aimed at eroding rely on in January – just a handful of of an ongoing barrage of cyberattacks in the cyber warzone.
Sign-up Right now for Log4j Exploit: Lessons Realized and Risk Reduction Best Procedures – a Live Threatpost function sked for Thurs., March 10 at 2PM ET. Be part of Sonatype code specialist Justin Young as he helps you sharpen code-hunting abilities to reduce attacker dwell time. Master why Log4j is still risky and how SBOMs match into computer software source-chain security. Register Now for this a single-time No cost occasion, Sponsored by Sonatype.

Some parts of this article are sourced from:
threatpost.com


 CNN+ streaming service arrives this spring for $6 per month
CNN+ streaming service arrives this spring for $6 per month