Password security has very long been an issue for businesses and their cybersecurity expectations. Account passwords are typically the weakest link in the in general security posture for a lot of organizations.
Quite a few providers have applied Microsoft’s default password policies for a long time. When these can be customized, firms often acknowledge the default values for their firm.
The Windows default password coverage is a fantastic start, but are there security vulnerabilities involved with it? Let’s appear at the existing recommendations from foremost cybersecurity authorities and see how they measure up versus the Windows default password policy.
Windows default password policy options
Several, if not most, organization environments these days use Microsoft Active Listing as their id and entry administration option in the enterprise. Active Directory has served organizations in this ability for many years.
Just one of the created-in abilities presented by Microsoft Energetic Directory Area Companies (Adds) is the developed-in ability to supply password coverage for an business.
What is a password plan? A password policy presents the set of demanded password features that stop-buyers will have to fulfill when choosing their account password. Down below is a seem at Lively Directory Default Domain Coverage Password Coverage configuration with usual values that many businesses may use.
A freshly promoted Windows Server 2019 Area Controller Default Domain Group Coverage demonstrates the default configurations for Password Coverage.
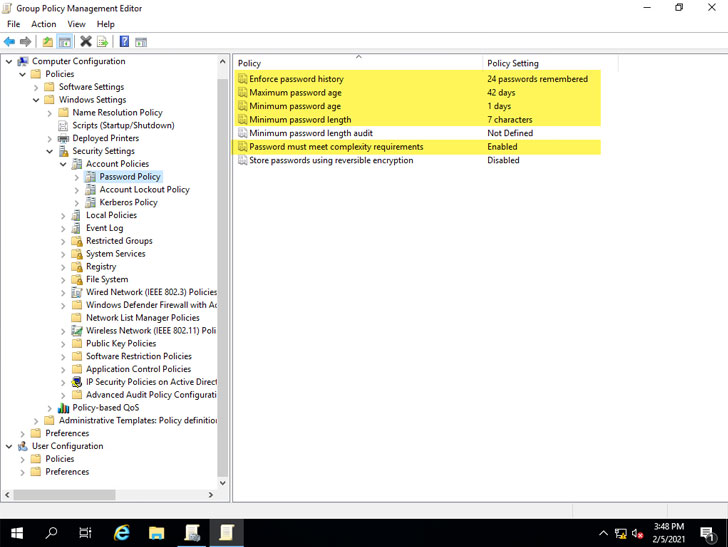 Default Windows Password Coverage options described in Default Domain Team Policy
Default Windows Password Coverage options described in Default Domain Team Policy
As you can see, distinct policy options are configured for you by default. These include things like:
- Enforce password heritage – 24 passwords remembered
- Maximum password age – 42 times
- Minimal password age – 1 working day
- Minimum amount password size – 7 characters
- Password will have to meet up with complexity demands – Enabled
- Retail outlet passwords using reversible encryption – Disabled
How do these defaults maintain up with the current suggestions from primary cybersecurity authorities about password recommendations?
Are Windows default password plan settings insecure?
There have been adjustments and strong tips designed in the latest yrs pertaining to password security that signify a change in password security recommendations. Sector cybersecurity gurus are emphasizing the need to verify passwords from identified weak password lists (dictionaries) and are putting significantly less target on password expiration insurance policies that have lengthy been a aspect of business password procedures.
The Countrywide Institute of Criteria and Technology (NIST) released the NIST Special Publication 800-63B (Electronic Identity Suggestions – Authentication and Lifecycle Management).
In Section 5.1.1, ‘Memorized Secrets,’ they observe this precise steerage in regards to evaluating passwords with acknowledged passwords from a dictionary or breach listing:
“When processing requests to set up and modify memorized secrets, verifiers SHALL review the possible secrets and techniques versus a list that includes values recognised to be generally-employed, predicted, or compromised. For example, the listing May well consist of, but is not limited to:
- Passwords obtained from preceding breach corpuses.
- Dictionary phrases.
- Repetitive or sequential characters (e.g. ‘aaaaaa’, ‘1234abcd’).
- Context-particular phrases, this sort of as the title of the provider, the username, and derivatives
- thereof.”
Yet another portion of the NIST guidance to observe concerning compulsory password alterations on periodic intervals:
“Verifiers Should NOT need memorized strategies to be transformed arbitrarily (e.g., periodically). Nevertheless, verifiers SHALL drive a change if there is proof of compromise of the authenticator.”
The NIST guidance in regards to periodic password variations is now passively encouraged by Microsoft. In the Security baseline (DRAFT) for Windows 10 v1903 and Windows Server v1903, Microsoft notes the pursuing concerning enforced periodic password adjustments:
“New scientific research calls into question the value of quite a few very long-standing password-security practices this sort of as password expiration procedures, and details rather to improved options these kinds of as enforcing banned-password lists (a good instance staying Azure Advert password security) and multi-element authentication. Although we endorse these options, they are unable to be expressed or enforced with our advised security configuration baselines, which are built on Windows’ constructed-in Group Coverage configurations and simply cannot include things like client-distinct values.”
Microsoft’s assistance will help to point out a flaw with the created-in Active Directory Team Coverage abilities. There are no developed-in signifies to implement banned-passwords very easily. Even though Microsoft does doc the approach to sign up a password filter .dll in its guidebook in this article, businesses need to write their very own tailor made password filter .dlls. This method can entail its individual established of problems.
Looking at the other Group Policy Password Plan defaults enabled, the 7-character bare minimum password duration falls brief of what is famous by a lot of foremost cybersecurity greatest tactics and recommendations from top authorities.
Note underneath the unique password policy typical least password length and if they advise evaluating passwords with a dictionary list.
- SANS Institute (admins) – 12 figures, dictionary
- NIST – 8 figures, dictionary
- NCSC – dictionary
- Microsoft Technet – 14 people
- Microsoft Exploration – 8 characters, dictionary
How can businesses easily audit their current password procedures in their environment and be certain these satisfy the recommended password security most effective methods? How can banned password lists be easily executed in Active Listing environments with no this designed-in ability?
Specops Password Auditor and Password Policy
Each the Specops Password Auditor (Absolutely free) and Specops Password Plan from Specops Program give particularly strong instruments that can aid corporations audit their present password insurance policies and speedily put into action breached password protection and custom dictionaries.
Organizations can put into action this functionality devoid of the need to have to method and produce a custom password filter .dll.
Specops Password Auditor provides an easy way to achieve visibility to password security risks in your setting quickly. Notably, this incorporates accounts with blank passwords, passwords set not to expire, breached passwords, stale admin accounts, and quite a few other people. One of the capabilities it gives is the ability to audit your password insurance policies.
Under, the Specops Password Auditor will allow you to quickly and quickly audit your existing area password guidelines and compare them against top market-conventional password plan suggestions.
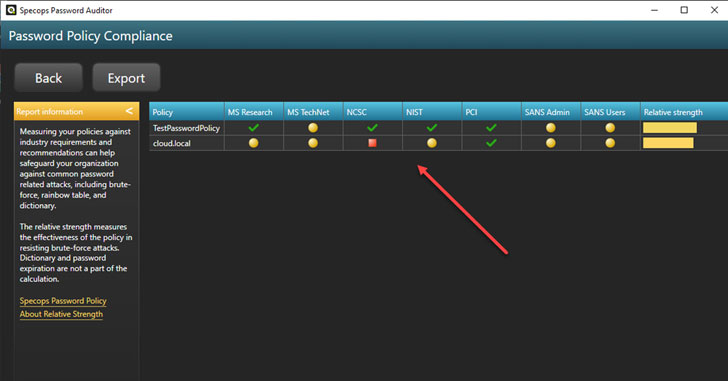 Evaluating Lively Directory Domain Coverage with field best follow suggestions for passwords
Evaluating Lively Directory Domain Coverage with field best follow suggestions for passwords
You can drill into each suggestion and see which unique requirement is not satisfied by your latest Active Listing password plan.
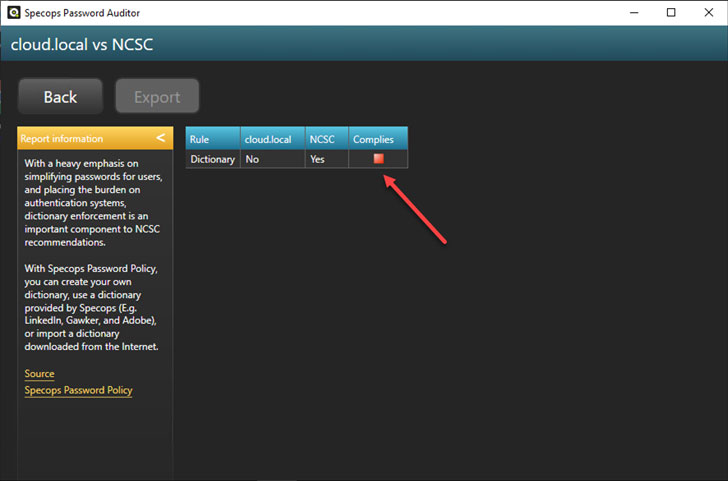 Viewing password policy options in comparison to precise field greatest practices
Viewing password policy options in comparison to precise field greatest practices
In addition to the visibility and capabilities presented by Specops Password Auditor, Specops Password Coverage supplies an effortless way to put into action banned-password lists in your Lively Directory natural environment. It also usually takes this a phase further by allowing you to implement breached password security.
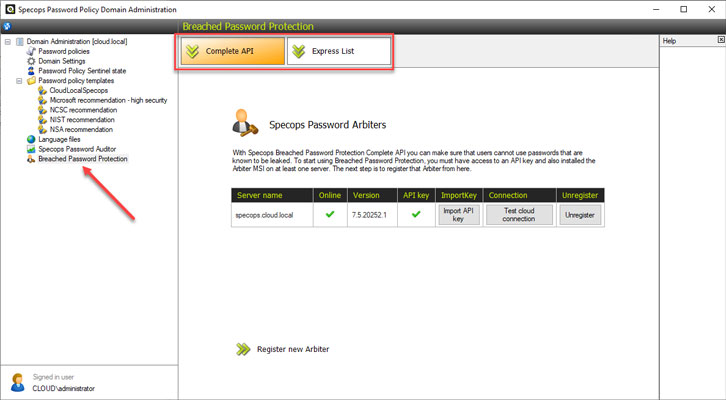 Specops Password Coverage breached password protection
Specops Password Coverage breached password protection
You can also drive buyers to alter passwords if their password becomes breached.
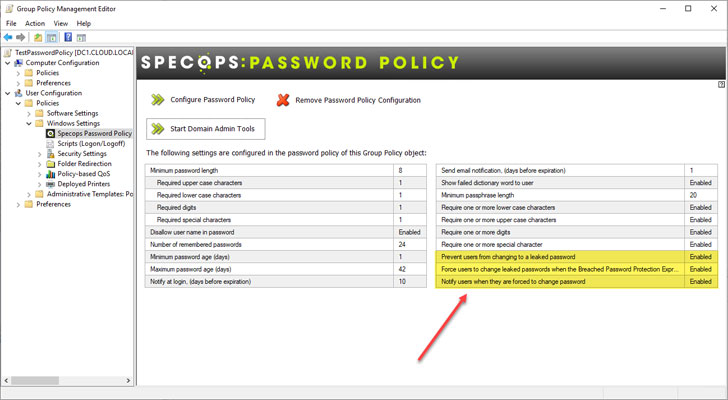 Force a password alter if an close-consumer password gets breached
Force a password alter if an close-consumer password gets breached
The breached and banned-password listing functionality furnished by Specops Password Policy extends the Windows default password plan. For this reason, organizations have a a lot extra sturdy and secure password plan for their natural environment.
Wrapping Up
Password security is crucial for the powerful in general security of your enterprise-critical data. Hackers are frequently employing credential theft as an simple way into your IT infrastructure.
Microsoft Active Listing Area Companies (Adds) is a greatly applied alternative in most business environments for id and accessibility administration. It also handles the enforcement of password policy for a lot of.
The Windows default password plan as configured and enforced by Lively Listing falls brief in numerous regions. Notably, it lacks any created-in means to test passwords versus tailor made dictionary lists or breached password lists.
Specops Password Auditor and Password Coverage allows companies promptly get visibility to password dangers in the ecosystem and simply increase banned-passwords and breached password record defense.
Download Specops Password Auditor.
Identified this write-up interesting? Comply with THN on Facebook, Twitter and LinkedIn to read through a lot more exceptional information we article.
Some parts of this article are sourced from:
thehackernews.com

 Sumo Logic Agrees Deal to Acquire DFLabs
Sumo Logic Agrees Deal to Acquire DFLabs