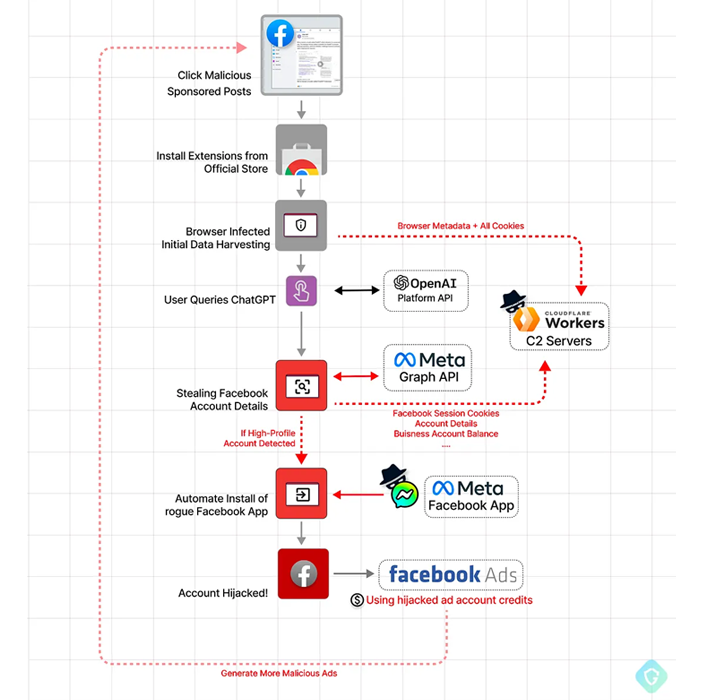
A faux ChatGPT-branded Chrome browser extension has been located to come with abilities to hijack Fb accounts and make rogue admin accounts, highlighting just one of the distinct procedures cyber criminals are applying to distribute malware.
“By hijacking significant-profile Facebook small business accounts, the menace actor creates an elite military of Facebook bots and a destructive paid out media apparatus,” Guardio Labs researcher Nati Tal said in a technological report.
“This allows it to press Facebook paid out advertisements at the expenditure of its victims in a self-propagating worm-like fashion.”
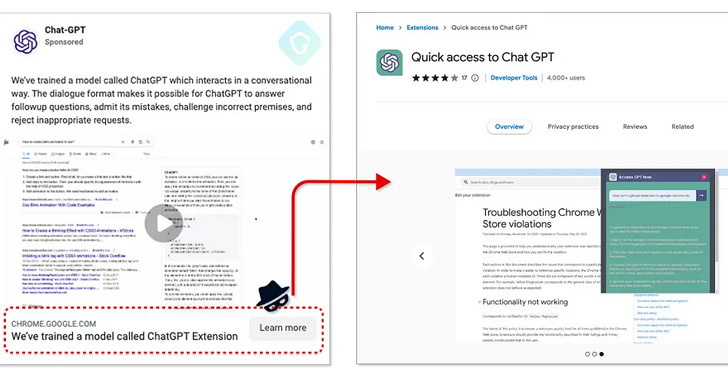
The “Speedy access to Chat GPT” extension, which is said to have attracted 2,000 installations for every day considering the fact that March 3, 2023, has considering that been pulled by Google from the Chrome Web Shop as of March 9, 2023.
The browser incorporate-on is promoted by way of Fb-sponsored posts, and when it features the ability to hook up to the ChatGPT provider, it truly is also engineered to surreptitiously harvest cookies and Facebook account knowledge utilizing an now energetic, authenticated session.
This is reached by building use of two bogus Fb applications – portal and msg_kig – to manage backdoor accessibility and acquire whole regulate of the focus on profiles. The approach of adding the apps to the Fb accounts is thoroughly automatic.
The hijacked Facebook enterprise accounts are then used to publicize the malware, therefore correctly growing its military of Fb bots.
The advancement comes as threat actors are capitalizing on the significant attractiveness of OpenAI’s ChatGPT considering the fact that its launch late past calendar year to create faux variations of the synthetic intelligence chatbot and trick unsuspecting people into installing them.
Final thirty day period, Cyble discovered a social engineering marketing campaign that relied on an unofficial ChatGPT social media website page to direct people to destructive domains that obtain info stealers, these types of as RedLine, Lumma, and Aurora.
WEBINARDiscover the Concealed Hazards of 3rd-Celebration SaaS Apps
Are you aware of the risks related with third-social gathering app access to your company’s SaaS applications? Be part of our webinar to understand about the kinds of permissions remaining granted and how to limit risk.
RESERVE YOUR SEAT
Also spotted are fake ChatGPT apps distributed by using the Google Participate in Retail store and other third-bash Android application merchants to thrust SpyNote malware onto people’s products.
“Sadly, the achievement of the viral AI tool has also attracted the notice of fraudsters who use the technology to perform really innovative financial commitment ripoffs towards unwary internet consumers,” Bitdefender disclosed previous week.
Identified this write-up intriguing? Adhere to us on Twitter and LinkedIn to examine more special information we submit.
Some parts of this article are sourced from:
thehackernews.com

 How to Apply NIST Principles to SaaS in 2023
How to Apply NIST Principles to SaaS in 2023