The vulnerability is ‘critical’ with a CVSS severity ranking of 9.8 out of 10.
Software service supplier F5 is warning a critical vulnerability permits unauthenticated hackers with network accessibility to execute arbitrary instructions on its Large-IP devices.
The F5 Large-IP is a blend of software program and components that is designed all over access regulate, software availability and security options.
The vulnerability is tracked as CVE-2022-1388 with a severity ranking of 9.8 out of 10 by the Widespread Vulnerabilities Scoring Method (CVSS) edition 3.90.
In accordance to F5, the flaw resides in the representational condition transfer (Relaxation) interface for the iControl framework which is employed to communicate amongst the F5 devices and end users.
Menace actors can mail undisclosed requests and leverage the flaw to bypass the iControl Rest authentication and accessibility the F5 Huge-IP techniques, an attacker can execute arbitrary commands, create or delete data files or disable servers.
“This vulnerability may permit an unauthenticated attacker with network accessibility to the Significant-IP method by the administration port and/or self IP addresses to execute arbitrary system instructions, generate or delete documents, or disable services,” said F5 in an advisory. “There is no knowledge plane exposure this is a manage aircraft issue only,” they added.
A self-IP deal with is an IP tackle on a Significant-IP system, that a shopper uses to associate with VLAN.
The Cybersecurity and Infrastructure Security Agency (CISA) issued an inform and recommended users to apply the required updates.
Impacted Variations
The security vulnerability that impacts the Huge-IP solution version are:
- 1. to 16.1.2
- 1. to 15.1.5
- 1. to 14.1.4
- 1. to 13.1.4
- 1. to 12.1.6
- 6.1 to 11.6.5
The F5 will not introduce fixes for versions 11.x (11.6.1 – 11.6.5) and 12.x (12.1. – 12.1.6).
The patches for versions v17.., v16.1.2.2, v15.1.5.1, v14.1.4.6, and v13.1.5 have been introduced by F5.
The advisory by F5 clarifies that the CVE-2022-1388 has no effect on other F5 products – Significant-IQ Centralized Management, F5OS-A, F5OS-C, or Targeted traffic SDC.
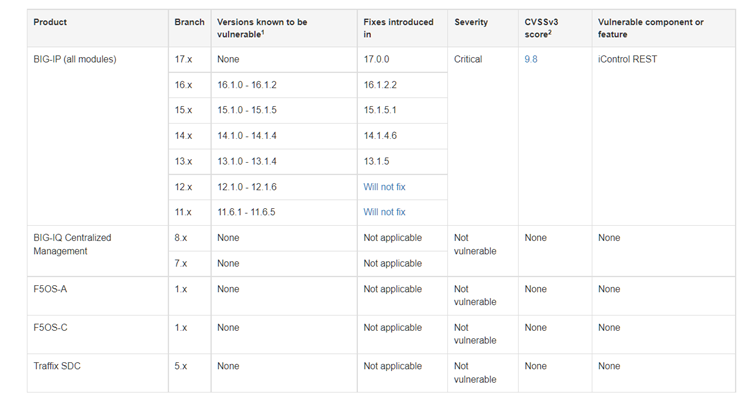
F5 afflicted products and fixed versions (Supply: F5)
The Major-IP gadgets are generally built-in into the enterprises there is a significant threat of common attack.
Security researcher Nate Warfield reported in a tweet that almost 16,000 Major-IP units are uncovered to the internet. A query shared by Warfield shows the exposed products on Shodan.
Most of the uncovered Big-IP units are located in the United states, China, India, and Australia. These programs are allotted to Microsoft company, Google LLC, DigitalOcean, and Linode.
Mitigations
A few “temporary mitigation” procedures were being recommended by F5, for those people who just cannot deploy security patches immediately.
In accordance to F5 “You can block all obtain to the iControl Relaxation interface of your Huge-IP program by way of self IP addresses”. This can be completed by altering the Port Lockdown configurations to Permit None for just about every self-IP tackle in the method.
An additional mitigation technique is to restrict iControl Relaxation entry by means of the administration interface or modify the Big-IP httpd configuration.
On top of that, F5 has also introduced a additional generic advisory to tackle one more established of 17 substantial severity vulnerabilities found and set in Significant-IP.
In July 2020, a critical RCE bug still left hundreds of F5 Significant-IP users’ accounts susceptible to an attacker.
Some parts of this article are sourced from:
threatpost.com


 Top Threats your Business Can Prevent on the DNS Level
Top Threats your Business Can Prevent on the DNS Level