Cybersecurity scientists have dissected the inner workings of an information-stealing malware known as Saintstealer that’s designed to siphon credentials and procedure data.
“Immediately after execution, the stealer extracts username, passwords, credit rating card specifics, and so on.,” Cyble scientists claimed in an analysis past 7 days. “The stealer also steals data from many spots across the procedure and compresses it in a password-protected ZIP file.”
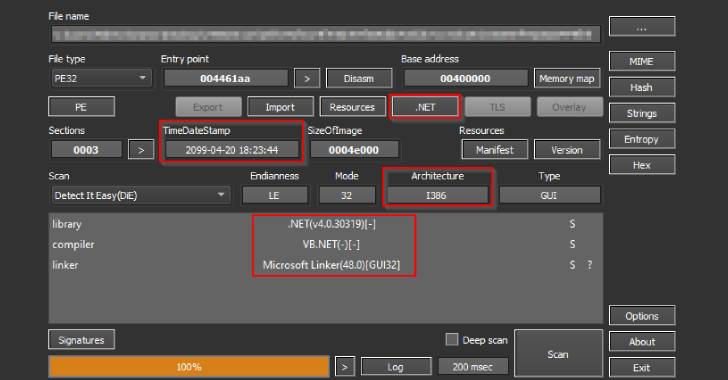
A 32-bit C# .NET-primarily based executable with the name “saintgang.exe,” Saintstealer is geared up with anti-examination checks, opting to terminate itself if it’s running either in a sandboxed or virtual environment.
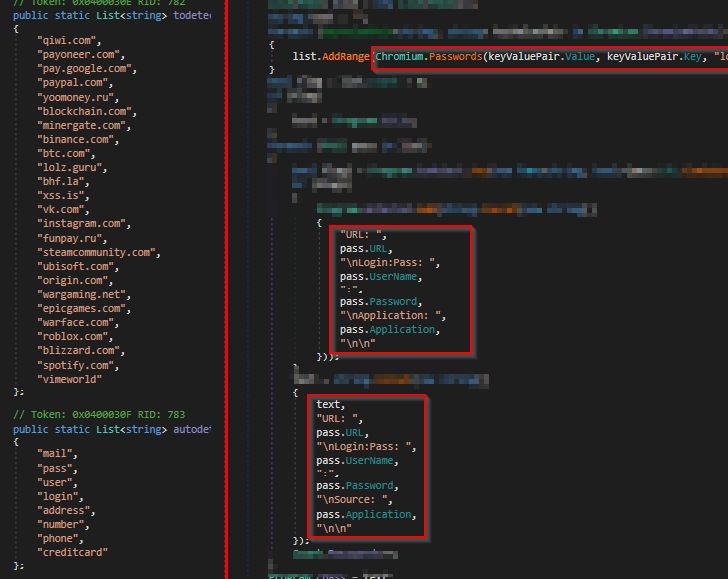
The malware can seize a vast variety of info that ranges from having screenshots to collecting passwords, cookies, and autofill details saved in Chromium-primarily based browsers these types of as Google Chrome, Opera, Edge, Courageous, Vivaldi, and Yandex, amongst other folks.
It can also steal Discord multi-issue authentication tokens, data files with .txt, .doc, and .docx extensions as well as extract information from VimeWorld, Telegram, and VPN apps like NordVPN, OpenVPN, and ProtonVPN.
Apart from transmitting the compressed information to a Telegram channel, the metadata similar to the exfiltrated info is despatched to a distant command-and-manage (C2) server.
What is actually additional, the IP tackle linked to the C2 domain — 141.8.197[.]42 — is tied to several stealer families these kinds of as Nixscare stealer, BloodyStealer, QuasarRAT, Predator stealer, and EchelonStealer.
“Details stealers can be destructive to persons as effectively as substantial businesses,” the researchers said. “If even unsophisticated stealers like Saintstealer obtain infrastructural obtain, it could have devastating outcomes on the cyberinfrastructure of the focused group.”
The disclosure will come as a new infostealer named Prynt Stealer has surfaced in the wild that can also perform keylogging functions and financial theft utilizing a clipper module.
“It can concentrate on 30+ Chromium-dependent browsers, 5+ Firefox-dependent browsers, and a assortment of VPN, FTP, messaging, and gaming apps,” Cyble pointed out past thirty day period.
Sold for $100 for a one-thirty day period license and $900 for a lifetime membership, the malware joins a prolonged record of other not long ago marketed stealers, which includes Jester, BlackGuard, Mars Stealer, META, FFDroider, and Lightning Stealer.
Located this report intriguing? Adhere to THN on Fb, Twitter and LinkedIn to examine additional special information we publish.
Some parts of this article are sourced from:
thehackernews.com

 What to expect at Google I/O 2022
What to expect at Google I/O 2022