TLDR:
Undertake a modern-day, test-driven methodology for securing your corporation with Detection-as-Code.
In excess of the earlier decade, threat detection has develop into enterprise-critical and even additional complicated. As enterprises go to the cloud, handbook risk detection processes are no lengthier able to hold up. How can teams automate security evaluation at scale and tackle the troubles that threaten company aims? The response lies in treating risk detections like application or detection-as-code.
Enjoy Panther’s On-Demand Webinar: Scaling Security with Detection-as-Code with Cedar to discover out how Cedar works by using Panther to leverage Detection-as-Code to construct higher-signal alerts.
Detection-as-Code: A New (Hope) Paradigm Detections determine logic for analyzing security log facts to discover attacker behaviors. When a rule is matched, an alert gets sent to your crew for containment or investigation.
What is detection-as-code?
Detection-as-Code is a modern, flexible, and structured solution to writing detections that apply software engineering most effective methods to security. By adopting this new paradigm, teams can create scalable procedures for creating and hardening detections to identify refined threats throughout quickly growing environments.
Gains of Adopting a Code-Driven Workflow
Menace detection plans that are wonderful-tuned for distinct environments and programs are the most impactful. By treating detections as well-penned code that can be examined, checked into supply management, and code-reviewed by friends, groups can make bigger-top quality alerts that cut down tiredness and quickly flag suspicious exercise.
1 — Establish Customized, Versatile Detections with a Programming Language
Composing detections in a universally-acknowledged, versatile, and expressive language these as Python gives many rewards as an alternative of applying domain-precise languages (DSL) that are as well minimal. With languages, this kind of as Python, you can write a lot more innovative and customized detections to healthy the wants precise to your enterprise. These guidelines also are inclined to be more readable and straightforward to recognize as the complexity increases.
A different gain of this approach is utilizing a loaded set of developed-in or third-get together libraries formulated by the security group for interacting with APIs or processing facts, which boosts the usefulness of the detection.
2 — Examination-Pushed Development (TDD)
A suitable QA for detection code can empower teams to learn detection blind-places early on, include tests for bogus alerts, and boost detection efficacy. A TDD method enables security groups to think like an attacker, document that understanding, and curate an inner repository of perception into the attacker’s lifecycle.
The benefit of TDD is much more than just validation of code correctness. A TDD approach to crafting detections increases the excellent of detection code and allows a lot more modular, extensible, and versatile detections. Engineers can easily make alterations to their detection without concern of breaking alerts or hamstringing every day functions.
3 — Collaboration with Variation Manage Systems
When composing new detections or modifying them, edition management enables groups to promptly and very easily revert to preceding states. It also confirms that teams are using the most up-to-date detection instead than referencing out-of-date or mistaken code. Variation regulate can also support give wanted context for distinct detections that brought on an inform or assistance pinpoint when detections are transformed.
As new and supplemental information enters the procedure about time, detections should also transform. A transform command approach is necessary to enable teams deal with and adjust the detections as wanted, while at the same time making sure that all variations are nicely-documented and well-reviewed.
4 — Automatic Workflows for Trustworthy Detections
A Continuous Integration/Constant Deployment (CI/CD) pipeline can be useful for security groups that have long preferred to go security further more left. Working with a CI/CD pipeline aids accomplish the adhering to two goals:
- Remove silos between groups as they function alongside one another on a prevalent system, code-critique every single other’s operate, and remain arranged.
- Provide automated testing and supply pipelines for your security detections. Teams can continue to be agile by focusing on setting up good-tuned detections. In its place of manually screening, deploying, and ensuring that the detections aren’t extremely tuned, which could set off wrong alerts.
5 — Reusable Code
Last but not least, Detection-as-Code can promote code reusability throughout a massive set of detections. As groups create massive quantities of detections more than time, they get started to see distinct patterns emerge. Engineers can reuse the current code to perform the same or really equivalent functionality throughout different detections without the need of beginning from scratch.
Code reusability can be a very important aspect of detection-creating that will allow teams to share features among detections or modify and adapt detections for precise use-scenarios. For example, suppose you required to repeat a set of Allow for/Deny lists (let’s say for access management) or a distinct processing logic in many sites. In that circumstance, you can use Helpers in languages such as Python to share capabilities concerning detections.
Introduction to Panther
Panther is a security analytics platform developed to ease the problems of standard SIEMs. Panther is built for security engineers, by security engineers. Somewhat than inventing but a different proprietary language for expressing detection logic, Panther gives security groups a Python regulations-engine to create expressive danger detection and automate detection and response at cloud-scale. Panther’s modular and open up technique features uncomplicated integrations and adaptable detections to support you establish a contemporary security functions pipeline.
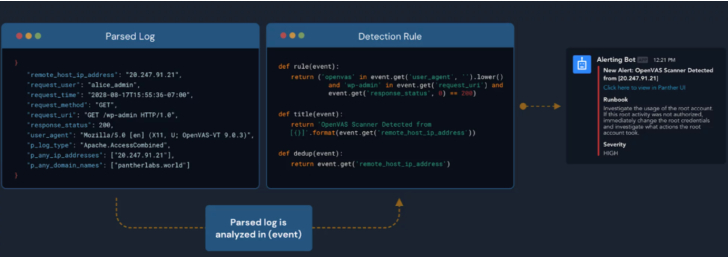 Detection-as-Code workflow in Panther
Detection-as-Code workflow in Panther
Panther gives reliable and resilient detections that can make it easy to:
- Create expressive and flexible detections in Python for requirements certain to your organization.
- Framework and normalize logs into a demanding schema that enables detections with Python and queries with SQL.
- Carry out actual-time danger detection and electricity investigations against substantial volumes of security knowledge.
- Profit from 200+ pre-developed detections mapped to specific threats, suspicious action, and security frameworks like MITRE ATT&CK.
Detection-as-Code workflow in Panther
An Instance Detection in Panther
When writing a detection in Panther, you start with a rule() perform that identifies a unique behavior to determine. For case in point, let us suppose you want an warn when a brute pressure Okta login is suspected. The next detection can help detect this conduct with Panther:
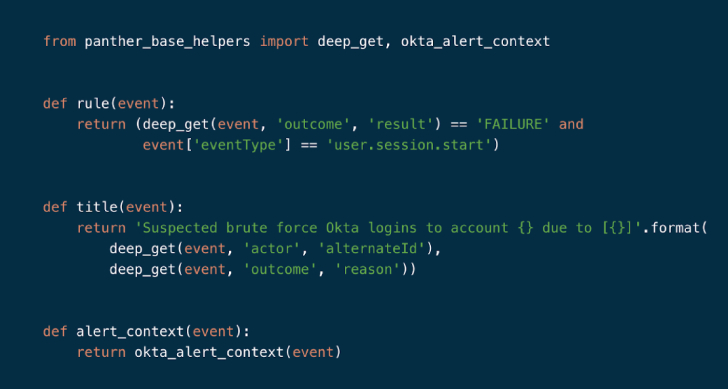 Okta Brute Power Login Rule in Panther
Okta Brute Power Login Rule in Panther
In the higher than example:
- The rule() perform can take 1 argument of ‘event’ and returns a boolean value.
- The title() operate controls the produced notify concept sent to analysts. Values from the occasions can then be interpolated to incorporate practical contexts.
Principles can be enabled and tested right in the Panther UI, or modified and uploaded programmatically with the Panther Analysis resource, which permits you to examination, deal, and deploy detections by using the command-line interface (CLI). And to support with incident triage, Panther rules have metadata these types of as severity, log kinds, unit exams, runbooks, and a lot more.
Get Begun
Are you having total benefit of all your security information to detect threats and suspicious action? Understand how to secure your cloud, network, programs, and endpoints with Panther Organization. Ask for a demo right now.
Observed this short article appealing? Comply with THN on Facebook, Twitter and LinkedIn to read a lot more exceptional articles we publish.
Some parts of this article are sourced from:
thehackernews.com


 Experts Detail Saintstealer and Prynt Stealer Info-Stealing Malware Families
Experts Detail Saintstealer and Prynt Stealer Info-Stealing Malware Families