The malware regarded as DirtyMoe has acquired new worm-like propagation abilities that make it possible for it to increase its arrive at without having necessitating any person conversation, the most up-to-date investigation has observed.
“The worming module targets more mature very well-recognized vulnerabilities, e.g., EternalBlue and Sizzling Potato Windows privilege escalation,” Avast researcher Martin Chlumecký said in a report revealed Wednesday.
“A single worm module can create and attack hundreds of 1000’s of private and general public IP addresses for each day lots of victims are at risk considering the fact that lots of machines still use unpatched devices or weak passwords.”

Energetic since 2016, the DirtyMoe botnet is used for carrying out cryptojacking and distributed denial-of-provider (DDoS) attacks, and is deployed by suggests of exterior exploit kits like PurpleFox or injected installers of Telegram Messenger.
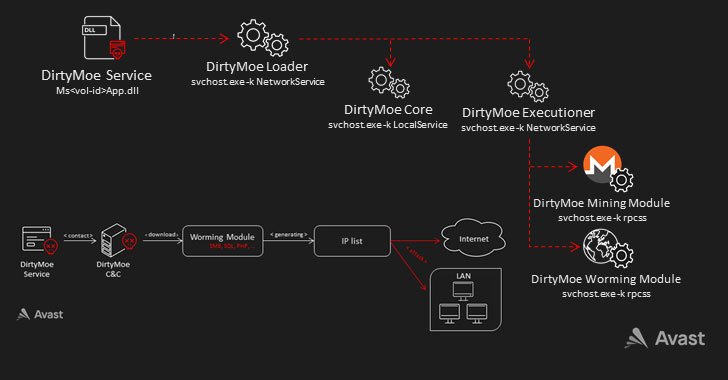
Also employed as element of the attack sequence is a DirtyMoe services that triggers the launch of two further procedures, specifically the Core and the Executioner, which is used to load the modules for Monero mining and to distribute the malware in a worm-like method.
The worming modules attack target equipment by using various vulnerabilities to set up the malware, with every single module concentrating on a particular flaw based on info gathered submit reconnaissance –
- CVE-2019-9082: ThinkPHP – Various PHP Injection RCEs
- CVE-2019-2725: Oracle Weblogic Server – ‘AsyncResponseService’ Deserialization RCE
- CVE-2019-1458: WizardOpium Community Privilege Escalation
- CVE-2018-0147: Deserialization Vulnerability
- CVE-2017-0144: EternalBlue SMB Distant Code Execution (MS17-010)
- MS15-076: RCE Enable Elevation of Privilege (Sizzling Potato Windows Privilege Escalation)
- Dictionary attacks aimed at MS SQL Servers, SMB, and Windows Administration Instrumentation (WMI) services with weak passwords

“The most important goal of the worming module is to reach RCE less than administrator privileges and set up a new DirtyMoe occasion,” Chlumecký explained, incorporating a single of the component’s core features is to deliver a checklist of IP addresses to attack based on the geological site of the module.
In addition, another in-advancement worming module was identified to incorporate exploits targeting PHP, Java Deserialization, and Oracle Weblogic Servers, implying that the attackers are wanting to broaden the scope of the infections.
“Worming goal IPs are generated utilizing the cleverly built algorithm that evenly generates IP addresses throughout the environment and in relation to the geological place of the worming module,” Chlumecký stated. “Moreover, the module targets community/house networks. Since of this, community IPs and even non-public networks driving firewalls are at risk.”
Found this posting intriguing? Abide by THN on Facebook, Twitter and LinkedIn to browse a lot more exclusive content we article.
Some parts of this article are sourced from:
thehackernews.com

 Clearcover makes getting car insurance online fast and easy
Clearcover makes getting car insurance online fast and easy