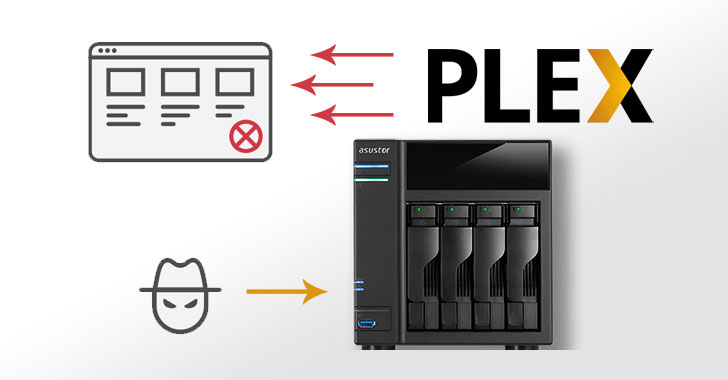
A new dispersed denial-of-company attack (DDoS) vector has ensnared Plex Media Server programs to amplify destructive targeted traffic from targets to get them offline.
“Plex’s startup processes unintentionally expose a Plex UPnP-enabled service registration responder to the common Internet, where by it can be abused to generate reflection/amplification DDoS attacks,” Netscout researchers claimed in a Thursday inform.
Plex Media Server is a private media library and streaming method that operates on contemporary Windows, macOS, and Linux operating units, as perfectly as variants customized for particular-function platforms these as network-connected storage (NAS) devices and digital media players. The desktop application organizes video, audio, and photos from a user’s library and from on the net companies, permitting entry to and stream the contents to other appropriate gadgets.

DDoS attacks ordinarily require flooding a authentic goal with junk network visitors that will come from a significant range of gadgets that have been corralled into a botnet, efficiently resulting in bandwidth exhaustion and main to significant service disruptions.
A DDoS amplification attack takes place when an attacker sends a variety of specifically-crafted requests to a third-social gathering server that leads to the server to reply with massive responses to a victim. This is performed by spoofing the supply IP handle to seem as if they are the target instead of the attacker, ensuing in site visitors that overwhelms victim means.
Hence when the third events react to the attacker’s ask for, the replies are routed to the server staying specific instead than the attacker unit that despatched the ask for.
Now in accordance to Netscout, DDoS-for-employ services are weaponizing Plex Media Servers to beef up their attack infrastructure, delivering an average amplification factor of about 4.68.
Plex helps make use of Uncomplicated Assistance Discovery Protocol (SSDP) to scan other media devices and streaming purchasers, but this gives way to a trouble when the probe locates an SSDP-enabled broadband internet accessibility router, and in the course of action, exposes the Plex service registration responder immediately on the Internet on UDP port 32414.
Generating matters even worse, the cybersecurity firm explained it determined about 27,000 abusable servers on the Internet to day.
“The collateral impression of PMSSDP reflection/amplification attacks is likely significant for broadband Internet access operators whose prospects have inadvertently exposed PMSSDP reflectors/amplifiers to the Internet,” Netscout researchers Roland Dobbins and Steinthor Bjarnason stated.
“This could involve partial or comprehensive interruption of end-client broadband internet entry, as nicely as extra assistance disruption thanks to obtain/distribution/aggregation/main/peering/transit connection capability usage.”
Netscout endorses network operators to filter traffic directed in direction of UDP/32414 and disable SSDP on operator-provided broadband internet access gear to mitigate the attack.
The advancement will come just after Netscout, before this thirty day period, described that Windows Remote Desktop Protocol (RDP) servers are remaining abused by DDoS-for-employ the service of companies as a reflection/amplification DDoS vector.
Observed this article intriguing? Adhere to THN on Fb, Twitter and LinkedIn to examine far more unique information we submit.
Some parts of this article are sourced from:
thehackernews.com

 Reliance Jio, Airtel likely increase combined revenue market share to 80%: Fitch
Reliance Jio, Airtel likely increase combined revenue market share to 80%: Fitch