Scammers are bypassing Apple’s App Retailer security, thieving 1000’s of dollars’ well worth of cryptocurrency from the unwitting, working with the TestFlight and WebClips programs.
For about a year now, crypto-traders and lovelorn singles alike have been losing their funds to CryptoRom, a malware marketing campaign that combines catfishing with crypto-scamming.
In accordance to analysis from Sophos, CryptoRom’s perpetrators have now improved their procedures. They’re leveraging new iOS attributes – TestFlight and WebClips – to get fake apps onto victims’ phones without the need of getting issue to the rigorous app keep approval approach.
Productive CryptoRom ripoffs have resulted in five-, 6- and even 7-figure losses for victims.
What is CryptoRom?
We do silly factors when we’re in like. In truth, scientifically talking, our inhibitions and selection-generating capabilities turn into impaired in the confront of romance and sexual arousal.
Possibly which is why hackers have been so profitable in targeting courting applications above the yrs. Very last year, the Federal Trade Fee reported that “romance scams” price U.S. citizens about 300 million dollars in 2020, up 50 p.c from 2019.
Capitalizing on this trend, final 12 months a new and properly-coordinated marketing campaign started concentrating on consumers of dating applications like Bumble, Tinder and Grindr. According to a Sophos report previous drop, the attackers’ M.O. is to start out there, then transfer the conversation to messaging applications.
“Once the target gets to be familiar, they check with them to put in faux buying and selling purposes with genuine searching domains and buyer assist,” researchers explained.
The investing apps are inclined to be cryptocurrency-related, since, extra so than with fiat currency, cryptocurrency payments are irreversible.
“They transfer the discussion to expense and ask them to spend a little volume, and even enable them withdraw that cash with revenue as bait,” according to Sophos. “After this, they will be advised to invest in many economical products and solutions or requested to commit in specific ‘profitable’ trading gatherings. The new good friend even lends some funds into the faux application, to make the victim believe they’re actual and caring. When the target wishes their revenue back or will get suspicious, they get locked out of the account.”
The ruse can go on very a even though just before victims catch on. Just one nameless human being explained to Sophos that they misplaced a lot more than $20,000, whilst one more complained of investing $100,000 into the pretend application, although bringing a brother and mates into the scheme unwittingly.
In the worst circumstance as a result significantly, 1 user wrote that “I have invested all my retirement money and bank loan dollars, about $1,004,000. I experienced no concept that they would freeze my account, requiring me to pay $625,000, which is 20 percent taxes on the full earnings right before they will unfreeze my account.”
What’s New This Time?
A essential ingredient to the CryptoRom attack circulation is people phony apps. Victims might acquire a connection to download what purports to be BTCBOX, for example, or Binance – properly authentic cryptocurrency buying and selling platforms. These applications seem to have specialist user interfaces, and even occur with consumer-service chat choices.
Apple and Google use rigorous vetting to weed out destructive cell applications like these from their formal stores. But, as Threatpost has lined prior to, hackers have intelligent tricks to get all-around common security screening. In the previous, for example, CryptoRom’s most popular technique was to use the Apple Developer Software and Company Signatures.
Now, CryptoRom is taking advantage of two new iOS options.
The first, TestFlight, is a aspect builders can use to distribute beta variations of their applications to testers.
“Unfortunately,” wrote the researchers, “just as we’ve seen transpire with other different application distribution techniques supported by Apple, ‘TestFlight Signature’ is offered as a hosted service for alternative iOS application deployment, generating it all much too simple for malware authors to abuse.”
CryptoRom has shifted from Company Signatures in the direction of TestFlight Signatures since, wrote Sophos, “it is a bit cheaper” – demanding only an .IPA file with a compiled iOS application. Applications also look”more legitimate when dispersed with the Apple Take a look at Flight Application,” researchers extra “The overview process is also believed to be less stringent than App Retailer overview.”
Even more so than TestFlight, CryptoRom attackers have been applying WebClips, a aspect that allows web one-way links to be extra to the iOS dwelling screen like standard applications. Malicious WebClips mimic actual apps like RobinHood (in the following circumstance, “RobinHand”).
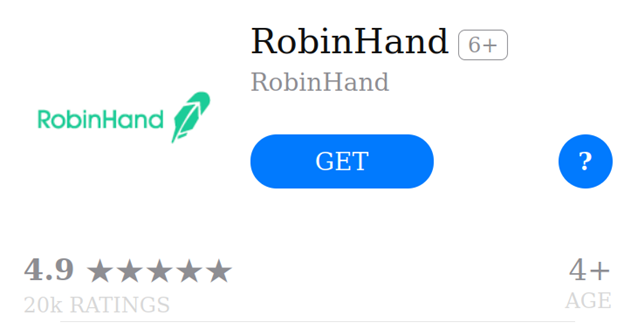
A destructive WebClip supplying in the Apple App Shop. Resource: Sophos.
“In addition to App Keep internet pages, all these fake internet pages also had linked websites with related templates to persuade buyers,” the researchers wrote. “This shows how low cost and simple it is to mimic well-liked brand names whilst siphoning hundreds of pounds from victims.”
Shifting to the cloud? Find emerging cloud-security threats alongside with strong information for how to defend your assets with our No cost downloadable Book, “Cloud Security: The Forecast for 2022.” We investigate organizations’ prime risks and challenges, very best methods for protection, and assistance for security achievements in this sort of a dynamic computing atmosphere, such as handy checklists.
Some parts of this article are sourced from:
threatpost.com


 Cadillac will offer two new features to select Super Cruise drivers this summer
Cadillac will offer two new features to select Super Cruise drivers this summer