A number of vulnerabilities have been disclosed in Hitachi Vantara’s Pentaho Small business Analytics application that could be abused by malicious actors to upload arbitrary facts information and even execute arbitrary code on the fundamental host technique of the application.
The security weaknesses were claimed by scientists Alberto Favero from German cybersecurity company Hawsec and Altion Malka from Census Labs earlier this year, prompting the corporation to issue required patches to deal with the issues.

Pentaho is a Java-centered small business intelligence platform that provides information integration, analytics, on-line analytical processing (OLAP), and mining capabilities, and counts major providers and organizations like Bell, CERN, Cipal, Logitech, Nasdaq, Telefonica, Teradata, and the Nationwide September 11 Memorial and Museum between its clients.
The listing of flaws, which influence Pentaho Organization Analytics versions 9.1 and lower, is as follows –
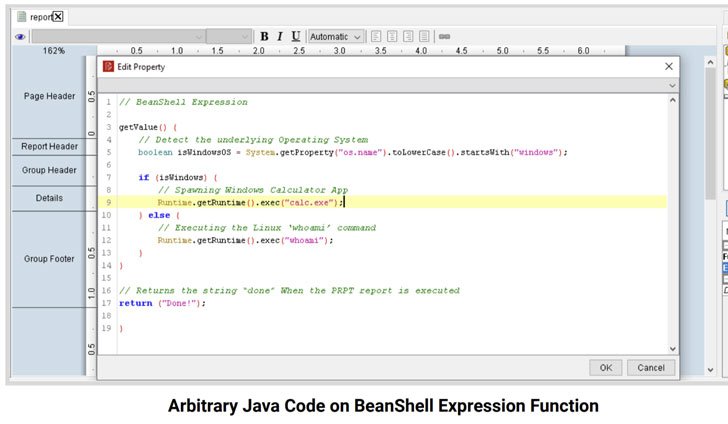
- CVE-2021-31599 (CVSS rating: 9.9) – Remote Code Execution by Pentaho Report Bundles
- CVE-2021-31600 (CVSS score: 4.3) – Jackrabbit Consumer Enumeration
- CVE-2021-31601 (CVSS score: 7.1) – Inadequate Obtain Handle of Info Resource Management
- CVE-2021-31602 (CVSS rating: 5.3) – Authentication Bypass of Spring APIs
- CVE-2021-34684 (CVSS rating: 9.8) – Unauthenticated SQL Injection
- CVE-2021-34685 (CVSS score: 2.7) – Bypass of Filename Extension Limitations
Thriving exploitation of the flaws could permit authenticated people with adequate job permissions to add and run Pentaho Report Bundles to run destructive code on the host server and exfiltrate sensitive application info, and circumvent filename extension limitations enforced by the software and add files of any kind.
What is actually a lot more, they could also be leveraged by a small-privilege authenticated attacker to retrieve credentials and link information of all Pentaho info sources, permitting the party to harvest and transmit facts, in addition to enabling an unauthenticated person to execute arbitrary SQL queries on the backend databases and retrieve facts.
In gentle of the critical character of the flaws and the risk they pose to the fundamental procedure, end users of the application are hugely proposed to update to the most current version.
Uncovered this write-up appealing? Adhere to THN on Fb, Twitter and LinkedIn to go through a lot more special information we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Securing SaaS Apps — CASB vs. SSPM
Securing SaaS Apps — CASB vs. SSPM