The Chinese cyber espionage actor regarded as Camaro Dragon has been noticed leveraging a new strain of self-propagating malware that spreads through compromised USB drives.
“Even though their most important concentration has historically been Southeast Asian nations, this most up-to-date discovery reveals their world wide reach and highlights the alarming job USB drives enjoy in spreading malware,” Examine Position explained in new study shared with The Hacker Information.
The cybersecurity corporation, which identified evidence of USB malware bacterial infections in Myanmar, South Korea, Good Britain, India, and Russia, reported the conclusions are the outcome of a cyber incident that it investigated at an unnamed European clinic in early 2023.
The probe located that the entity was not specifically focused by the adversary but fairly suffered a breach by using an employee’s USB push, which turned contaminated when it was plugged into a colleague’s pc at a conference in Asia.
“For that reason, on returning to the health care establishment in Europe, the employee inadvertently introduced the infected USB travel, which led to unfold of the infection to the hospital’s laptop techniques,” the business stated.

Camaro Dragon shares tactical similarities with that of action clusters tracked as Mustang Panda and LuminousMoth, with the adversarial crew not too long ago connected to a Go-dependent backdoor named TinyNote and a malicious router firmware implant named HorseShell.
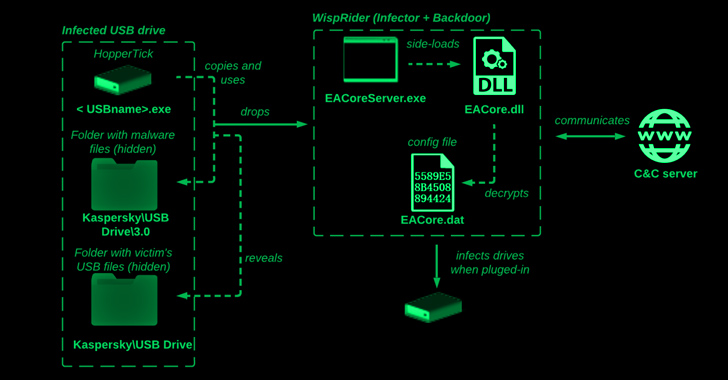
The most up-to-date infection chain includes a Delphi launcher recognised as HopperTick which is propagated by way of USB drives and its most important payload dubbed WispRider, which is responsible for infecting the gadgets when they are attached to a equipment.
“When a benign USB thumb travel is inserted into an contaminated personal computer, the malware detects a new machine inserted into the Computer and manipulates its data files, developing several hidden folders at the root of the thumb push,” Verify Stage researchers stated.
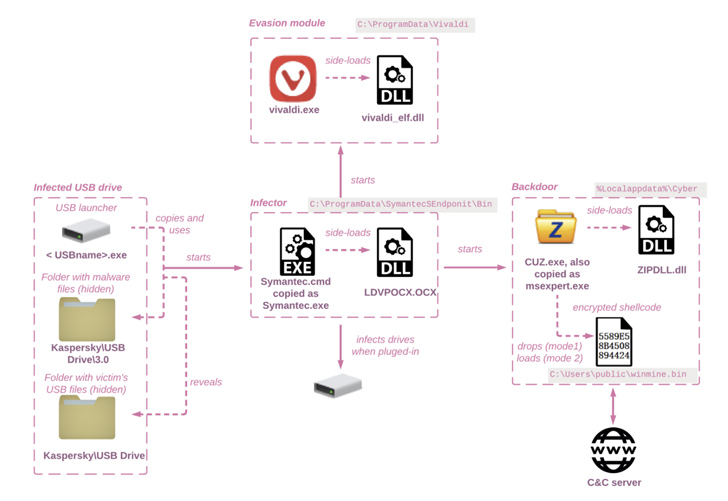
WispRider, moreover infecting the existing host if not currently, is tasked with communicating with a remote server, compromising any newly linked USB units, executing arbitrary instructions, and performing file functions.
Pick out variants of WispRider also functionality as a backdoor with abilities to bypass an Indonesian antivirus remedy known as Smadav as perfectly as resort to DLL side-loading by applying elements from security computer software like G-Knowledge Complete Security.
A further publish-exploitation payload shipped together with WispRider is a stealer module referred to as disk watch (HPCustPartUI.dll) that phases information with predefined extensions (i.e., docx, mp3, wav, m4a, wma, aac, cda, and mid) for exfiltration.
Future WEBINAR🔐 Mastering API Security: Being familiar with Your Genuine Attack Surface area
Learn the untapped vulnerabilities in your API ecosystem and choose proactive methods in direction of ironclad security. Be part of our insightful webinar!
Be a part of the Session.wn-button,.wn-label,.wn-label:followingexhibit:inline-block.test_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px strong #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-best-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-right-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-measurement:13pxmargin:20px 0font-fat:600letter-spacing:.6pxcolor:#596cec.wn-label:right afterwidth:50pxheight:6pxcontent:”border-top:2px reliable #d9deffmargin: 8px.wn-titlefont-size:21pxpadding:10px 0font-bodyweight:900text-align:leftline-top:33px.wn-descriptiontext-align:leftfont-dimensions:15.6pxline-height:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-color:#4469f5font-size:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-fat:500letter-spacing:.2px
This is not the first time Chinese risk actors have been observed taking gain of USB devices as an an infection vector to get to environments far further than the scope of the risk actor’s principal passions.
In November 2022, Google-owned Mandiant attributed UNC4191, a danger actor with a suspected China nexus, to a established of espionage assaults in the Philippines that guide to the distribution of malware such as MISTCLOAK, DARKDEW, and BLUEHAZE.
A subsequent report from Pattern Micro in March 2023 disclosed overlaps concerning UNC4191 and Mustang Panda, connecting the latter to the use of MISTCLOAK and BLUEHAZE in spear-phishing campaigns focusing on nations around the world in Southeast Asia.
The enhancement is a signal that the danger actors are actively altering their equipment, strategies, and processes (TTPs) to bypass security methods, whilst simultaneously relying on a vast assortment of personalized equipment to exfiltrate delicate data from target networks.
“The Camaro Dragon APT group proceeds to make use of USB products as a strategy for infecting specific units, correctly combining this procedure with other established methods,” the scientists said.
Located this short article intriguing? Adhere to us on Twitter and LinkedIn to browse additional exclusive material we publish.
Some parts of this article are sourced from:
thehackernews.com

 Unveiling the Unseen: Identifying Data Exfiltration with Machine Learning
Unveiling the Unseen: Identifying Data Exfiltration with Machine Learning