Why Information Exfiltration Detection is Paramount?
The entire world is witnessing an exponential rise in ransomware and details theft utilized to extort businesses. At the exact same time, the business faces numerous critical vulnerabilities in databases software and company internet sites. This evolution paints a dire picture of info exposure and exfiltration that every single security leader and team is grappling with. This article highlights this challenge and expounds on the positive aspects that Equipment Finding out algorithms and Network Detection & Response (NDR) strategies convey to the desk.
Facts exfiltration frequently serves as the ultimate act of a cyberattack, earning it the last window of possibility to detect the breach before the facts is designed community or is made use of for other sinister things to do, this sort of as espionage. Having said that, details leakage just isn’t only an aftermath of cyberattacks, it can also be a consequence of human mistake. Even though avoidance of facts exfiltration by way of security controls is best, the escalating complexity and dispersion of infrastructures, accompanied by the integration of legacy devices, would make avoidance a physically demanding activity. In these types of situations, detection serves as our ultimate basic safety net – in truth, far better late than in no way.
Addressing the Problem of Detecting Info Exfiltration
Attackers can exploit various security gaps to harvest and exfiltrate knowledge, using protocols like DNS, HTTP(S), FTP and SMB. The MITRE ATT&CK framework describes quite a few these types of exfiltration attack designs. Even so, maintaining speed with each individual protocol and infrastructure modification is a challenging endeavor, complicating the integration towards holistic security monitoring. What is desired is device- or network-certain quantity-based analysis of applicable thresholds.
This is the place Network Detection & Response (NDR) technology methods in. ML-driven NDR will allow for essential network checking by offering two significant qualities:
Decoding Machine Finding out for Details Exfiltration Detection
Right before Machine Studying, thresholds for distinct networks or clients ended up manually established. For that reason, an inform was brought on when a system despatched a lot more than the precise threshold of knowledge outside the network. Having said that, Machine Learning algorithms introduced a number of rewards for knowledge exfiltration detection:
 Visualization: When the visitors quantity surpasses a particular threshold, as identified by the uncovered profile, an inform will be activated.
Visualization: When the visitors quantity surpasses a particular threshold, as identified by the uncovered profile, an inform will be activated.
ML-driven Network Detection & Response to the Rescue
Network Detection & Reaction (NDR) remedies deliver a thorough and insightful strategy to detect abnormal network actions and unpredicted surges in details transmission. Leveraging Device Learning (ML), these options set up a network interaction baseline, facilitating the swift identification of outliers. This applies to volume assessment and covert channels alike. Through this advanced, proactive stance, NDRs can detect the first signals of intrusion, usually effectively before data exfiltration transpires.
A single NDR solution, distinguished by its specific data volume monitoring, is ExeonTrace. This Swiss NDR method, driven by award-successful ML algorithms, passively inspects and analyzes network visitors in actual time, identifying potentially dangerous or unauthorized facts movement. Furthermore, ExeonTrace integrates seamlessly with existing infrastructure, thus doing away with the necessity for supplemental hardware brokers. The positive aspects of ExeonTrace prolong past mere security, aiding in the comprehension of normal and anomalous network conduct – a critical factor in establishing a strong and productive security posture.
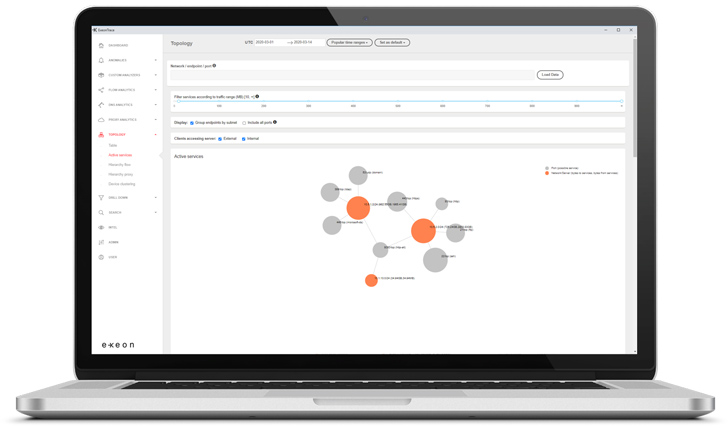 ExeonTrace System: Knowledge Volume Outlier Detection
ExeonTrace System: Knowledge Volume Outlier Detection
Important Takeaways
In present-day electronic landscape, networks are continually growing, and vulnerabilities are escalating. As a final result, powerful details exfiltration detection will become indispensable. Having said that, with the complexity of present day networks, location manual thresholds for outlier detection can not only be cumbersome but also almost extremely hard. Via volume-based mostly detections and visitors behaviour monitoring, a person can identify facts exfiltration, pinpointing irregular alterations in knowledge volume and add/down load visitors styles. Herein lies the power of Equipment Discovering (ML) in Network Detection & Response (NDR) programs: it mechanically identifies infrastructure-distinct thresholds and outliers.
Amongst these NDR methods, ExeonTrace stands out, giving thorough network visibility, helpful anomaly detection, and a fortified security stance. These functions make certain that organization functions proceed with security and effectiveness. Request a demo to locate out how to leverage ML-pushed NDR to detect details exfiltration and anomalous network behaviours for your organisation.
Located this post attention-grabbing? Stick to us on Twitter and LinkedIn to browse a lot more exceptional content material we post.
Some parts of this article are sourced from:
thehackernews.com


 Critical Flaw Found in WordPress Plugin for WooCommerce Used by 30,000 Websites
Critical Flaw Found in WordPress Plugin for WooCommerce Used by 30,000 Websites