Security researchers have get rid of extra mild on the cryptocurrency mining procedure performed by the 8220 Gang by exploiting identified security flaws in the Oracle WebLogic Server.
“The threat actor employs fileless execution methods, utilizing DLL reflective and course of action injection, letting the malware code to run solely in memory and stay clear of disk-based mostly detection mechanisms,” Craze Micro scientists Ahmed Mohamed Ibrahim, Shubham Singh, and Sunil Bharti explained in a new assessment posted right now.
The cybersecurity company is tracking the economically enthusiastic actor underneath the identify H2o Sigbin, which is identified to weaponize vulnerabilities in Oracle WebLogic Server this sort of as CVE-2017-3506, CVE- 2017-10271, and CVE-2023-21839 for original access and drop the miner payload by using multi-phase loading approach.
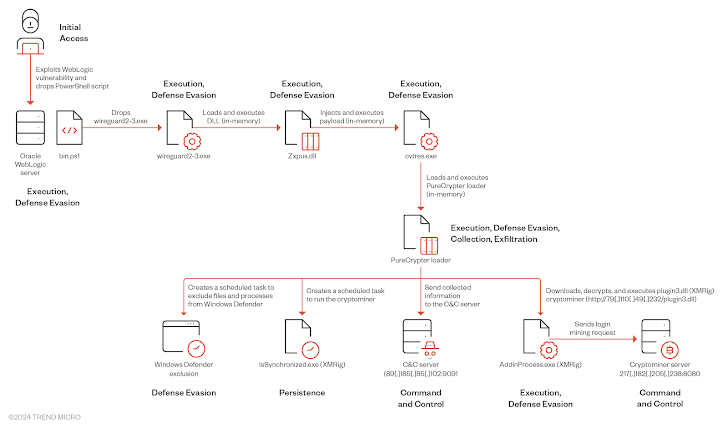
A successful foothold is adopted by the deployment of PowerShell script that is liable for dropping a to start with-phase loader (“wireguard2-3.exe”) that mimics the respectable WireGuard VPN application, but, in fact, launches an additional binary (“cvtres.exe”) in memory by usually means of a DLL (“Zxpus.dll”).

The injected executable serves as a conduit to load the PureCrypter loader (“Tixrgtluffu.dll”) that, in transform, exfiltrates components details to a distant server and generates scheduled duties to run the miner as effectively as excludes the malicious information from Microsoft Defender Antivirus.
In reaction, the command-and-handle (C2) server responds with an encrypted concept containing the XMRig configuration aspects, subsequent which the loader retrieves and executes the miner from an attacker-controlled domain by masquerading it as “AddinProcess.exe,” a legit Microsoft binary.
The advancement will come as the QiAnXin XLab crew comprehensive a new installer software employed by the 8220 Gang termed k4spreader given that at the very least February 2024 to produce the Tsunami DDoS botnet and the PwnRig mining application.
The malware, which is at the moment under progress and has a shell version, has been leveraging security flaws these kinds of as Apache Hadoop YARN, JBoss, and Oracle WebLogic Server to infiltrate inclined targets.
“k4spreader is prepared in cgo, like system persistence, downloading and updating alone, and releasing other malware for execution,” the firm claimed, incorporating it truly is also developed to disable the firewall, terminate rival botnets (e.g., kinsing), and printing operational status.
Discovered this report appealing? Comply with us on Twitter and LinkedIn to read far more special articles we article.
Some parts of this article are sourced from:
thehackernews.com


 Combatting the Evolving SaaS Kill Chain: How to Stay Ahead of Threat Actors
Combatting the Evolving SaaS Kill Chain: How to Stay Ahead of Threat Actors