Corporations in East Asia are currently being specific by a very likely Chinese-talking actor dubbed DragonSpark when using unheard of techniques to go past security layers.
“The assaults are characterized by the use of the minimal recognized open resource SparkRAT and malware that attempts to evade detection through Golang resource code interpretation,” SentinelOne claimed in an evaluation posted currently.
A hanging element of the intrusions is the constant use of SparkRAT to conduct a range of things to do, like thieving details, obtaining handle of an infected host, or operating additional PowerShell instructions.
The danger actor’s conclude objectives keep on being mysterious as still, although espionage or cybercrime is probably to be the motive. DragonSpark’s ties to China stem from the use of the China Chopper web shell to deploy malware – a commonly utilised attack pathway amongst Chinese threat actors.
On top of that, not only do the open up source tools utilised in the cyber assaults originate from developers or firms with hyperlinks to China, the instructure for staging the payloads are situated in Taiwan, Hong Kong, China, and Singapore, some of which belong to respectable enterprises.
The command-and-handle (C2) servers, on the other hand, are situated in Hong Kong and the U.S., the cybersecurity company claimed.
Initial access avenues entail compromising internet-uncovered web servers and MySQL databases servers to fall the China Chopper web shell. The foothold is then leveraged to have out lateral movement, privilege escalation, and malware deployment employing open source tools like SharpToken, BadPotato, and GotoHTTP.
Also sent to the hosts are custom malware capable of executing arbitrary code and SparkRAT, a cross-system remote entry trojan that can operate procedure commands, manipulate documents and processes, and siphon facts of desire.
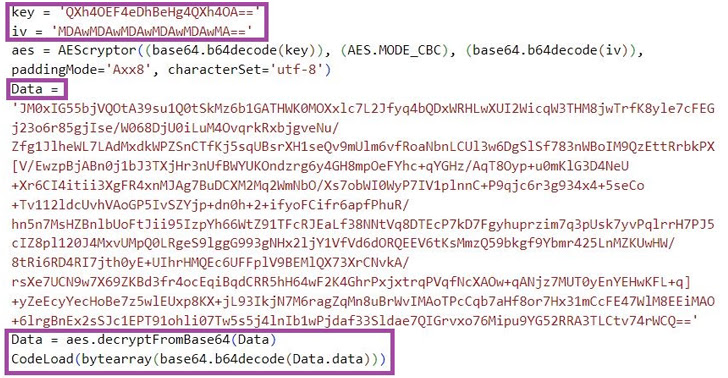
An additional malware of be aware is the Golang-based m6699.exe, which interprets at runtime the source code contained in just it so as to fly under the radar and launch a shellcode loader which is engineered to speak to the C2 server for fetching and executing the future-phase shellcode.
“Chinese-talking menace actors are regarded to frequently use open source software in malicious campaigns,” the researchers concluded.
“Considering that SparkRAT is a multi-system and element-rich device, and is routinely current with new attributes, we estimate that the RAT will keep on being beautiful to cybercriminals and other risk actors in the future.”
Discovered this post exciting? Comply with us on Twitter and LinkedIn to go through more exclusive information we put up.
Some parts of this article are sourced from:
thehackernews.com


 ICO Offers Data Protection Advice to SMBs
ICO Offers Data Protection Advice to SMBs