GitHub has put out an advisory detailing what may be an ongoing phishing marketing campaign focusing on its users to steal credentials and two-element authentication (2FA) codes by impersonating the CircleCI DevOps platform.
The Microsoft-owned code hosting provider said it acquired of the attack on September 16, 2022, including the campaign impacted “many target organizations.”
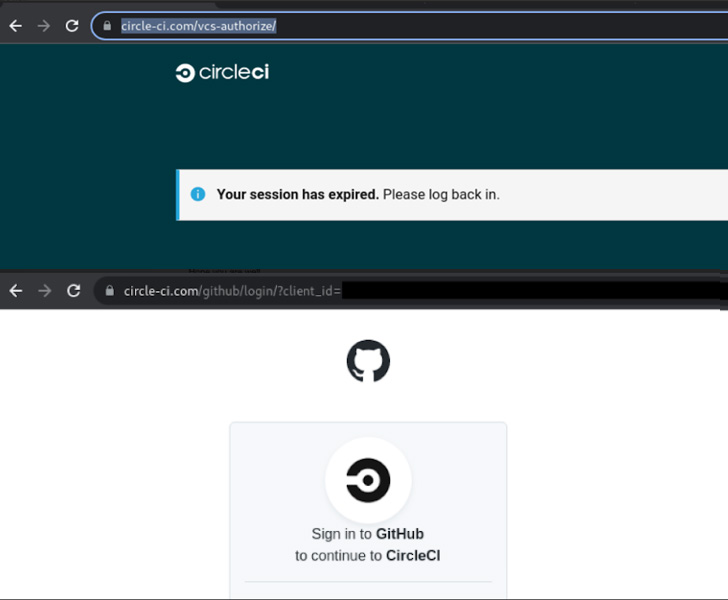
The fraudulent messages assert to notify buyers that their CircleCI classes have expired and that they should log in using GitHub qualifications by clicking on a website link.

Another bogus email revealed by CircleCI prompts people to indication in to their GitHub accounts to acknowledge the firm’s new Conditions of Use and Privateness Coverage by next the link embedded in the concept.
Regardless of the lure, executing so redirects the goal to a lookalike GitHub login web site intended to steal and exfiltrate the entered qualifications as well as the Time-based One Time Password (TOTP) codes in actual-time to the attacker, efficiently permitting a 2FA bypass.
“Accounts safeguarded by hardware security keys are not vulnerable to this attack,” GitHub’s Alexis Wales claimed.
Among the other techniques embraced by the risk actor upon gaining unauthorized entry to the user account include things like making GitHub personal obtain tokens (PATs), authorizing OAuth purposes, or introducing SSH keys to preserve obtain even just after a password change.
The attacker has also been noticed downloading personal repository contents, and even developing and adding new GitHub accounts to an organization need to the compromised account have corporation administration permissions.
GitHub claimed it has taken actions to reset passwords and remove maliciously-extra qualifications for impacted end users, together with notifying those people impacted and suspending the actor-managed accounts. It did not disclose the scale of the attack.
The corporation is even further urging businesses to consider using phishing-resistant components security keys to reduce such assaults.
The most up-to-date phishing attack arrives a minimal over 5 months right after GitHub experienced a remarkably targeted marketing campaign that resulted in the abuse of third-bash OAuth consumer tokens maintained by Heroku and Travis CI to download personal repositories.
Identified this write-up exciting? Abide by THN on Fb, Twitter and LinkedIn to read through more distinctive content we publish.
Some parts of this article are sourced from:
thehackernews.com


 Microscopic robots walk autonomously using simple 'brains'
Microscopic robots walk autonomously using simple 'brains'