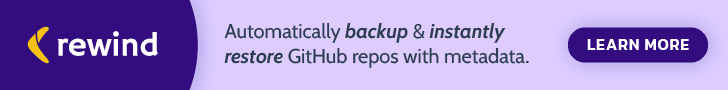
As numerous as 23 new large severity security vulnerabilities have been disclosed in unique implementations of Unified Extensible Firmware Interface (UEFI) firmware utilised by various vendors, such as Bull Atos, Fujitsu, HP, Juniper Networks, Lenovo, among the other folks.
The vulnerabilities reside in Insyde Software’s InsydeH2O UEFI firmware, in accordance to company firmware security enterprise Binarly, with a the greater part of the anomalies diagnosed in the Process Management Method (SMM).
UEFI is a software program specification that delivers a typical programming interface connecting a computer’s firmware to its working method through the booting procedure. In x86 methods, the UEFI firmware is commonly stored in the flash memory chip of the motherboard.
“By exploiting these vulnerabilities, attackers can efficiently install malware that survives functioning system re-installations and lets the bypass of endpoint security remedies (EDR/AV), Safe Boot, and Virtualization-Primarily based Security isolation,” the scientists stated.
Effective exploitation of the flaws (CVSS scores: 7.5 – 8.2), could let a malicious actor to operate arbitrary code with SMM permissions, a specific-intent execution mode in x86-based mostly processors that handles electrical power management, hardware configuration, thermal checking, and other features.
“SMM code executes in the greatest privilege degree and is invisible to the OS, which makes it an eye-catching target for destructive exercise,” Microsoft notes in its documentation, incorporating the SMM attack vector could be abused by a piece of nefarious code to trick yet another code with greater privileges into carrying out unauthorized functions.
Worse, the weaknesses can also be chained with each other to bypass security attributes and set up malware in a method that survives working system re-installations and reach prolonged-expression persistence on compromised systems — as noticed in the case of MoonBounce — though stealthily producing a communications channel to exfiltrate delicate info.
Insyde has produced firmware patches that address these shortcomings as part of the coordinated disclosure course of action. But the fact that the program is applied in many OEM implementations means it could take a sizeable sum of time ahead of the fixes really trickle down to impacted gadgets.
Uncovered this report exciting? Observe THN on Fb, Twitter and LinkedIn to examine more distinctive material we post.
Some parts of this article are sourced from:
thehackernews.com

 Hacker Group ‘Moses Staff’ Using New StrifeWater RAT in Ransomware Attacks
Hacker Group ‘Moses Staff’ Using New StrifeWater RAT in Ransomware Attacks